What Is a DNS Leak? How to Test for and Avoid DNS Leaks in 2026
If you’re a VPN user, you might be worried about your VPN failing to encrypt your traffic properly, resulting in a DNS leak. You might be wondering: What is a DNS leak? In this guide, we’ll answer that question and teach you how to avoid DNS leaks.
Whenever you connect to a website, you send a DNS request to its server. Unless you’re on an encrypted connection, your DNS requests are visible to your ISP and any potential interlopers. A VPN keeps your DNS requests private by sending your traffic through an encrypted tunnel, but even VPNs can leak. So what is a DNS leak and how can you prevent your DNS requests from leaking?
Key Takeaways:
- A DNS leak occurs when your VPN fails to encrypt your DNS traffic and your DNS queries revert to your ISP’s DNS servers.
- A good VPN runs its own DNS server and encrypts your traffic in order to best protect your data.
- You can easily test for DNS leaks by using an online DNS leak test.
- To prevent DNS leaks, have your VPN’s kill switch active at all times. If there’s the option to disable DNS leak protection, make sure to never click it.
In this article, we’ll explain how DNS and IP addresses work, how to change your DNS server to a more private one and how to do a DNS leak test for your VPN. Read on for the full scoop.
-
11/20/2022
We rewrote this article to simplify it and make it easier to understand. We also added guides for how to test for DNS leaks and how to avoid them.
How Do DNS and IP Addresses Work?
The concepts of DNS and IP addresses are closely linked. Every device on the internet has its own unique IP address, which lets it communicate with other online devices. However, numerical IP addresses are difficult to remember. This is why, when you want to access a website, you use its domain name instead.
DNS stands for “domain name system.” In a nutshell, it’s a phone book of IP addresses, where each IP address has its corresponding domain name. For example, let’s say you want to visit Google. Instead of typing in the IP address 192.168.10.254, you can just type in the domain name google.com and your browser will take you to Google’s website.
Protect Your Privacy. Get Our Free VPN Guide Now!
- Comprehend the essential role a VPN plays in safeguarding your digital life
- Gain a deep understanding of how VPNs function under the hood
- Develop the ability to distinguish fact from fiction in VPN promotions
Changing DNS Servers
DNS servers are key to this process because they translate domain names into IP addresses. Before you get to the website you’re trying to access, your device sends a DNS request to a DNS server. This server translates the domain name into an IP address, facilitating your communication with the website’s server.

This means that you need to have complete trust in the DNS server, because its operator can technically see all of your traffic.
By default, that DNS server operator is your ISP, and that should raise some concerns. ISPs collect a lot of data and they use legal loopholes to sell it to third parties, including advertisers. For this reason, you’ll probably want to hide your traffic from your ISP’s DNS server.
The easiest way to do that is to use a trustworthy VPN service. Check out our list of the best VPN providers. A VPN provider runs its own DNS servers, which are subject to the VPN’s no-logs policy. This means that they don’t collect any of your browsing data.
What Is a DNS Leak?
A DNS leak happens when your VPN fails and your DNS requests default back to your ISP’s DNS server making them known to your ISP. Unfortunately, not all VPN providers are good enough to protect your data. In fact, many free VPNs are part of data harvesting scams, which is why some prudence is necessary when choosing a VPN provider.
There are other ways DNS leaks can happen as well. For instance, if you’re connected to a public WiFi network and someone takes control of the router, they might be able to manipulate your traffic so that it bypasses the VPN tunnel, exposing your DNS requests. However, most DNS leaks happen because of human error while setting up a custom VPN or DNS server.
Most commercial VPN services use various mechanisms to prevent DNS leaks, and we’ll talk about that later in this article.
How Do I Test for DNS Leaks?
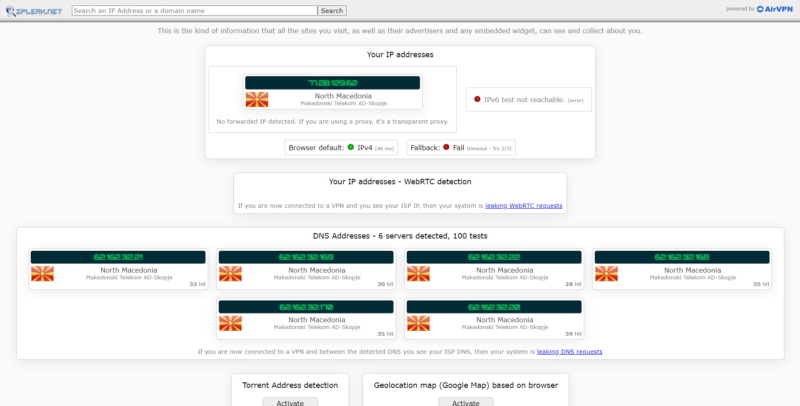
Performing a DNS leak check is easy. There are plenty of reliable tests you can do online, and we frequently use the DNS leak test at IPleak.net to test for leaks.
To do an IPleak test, first, run the test using an unprotected connection and note the results you get. Then, connect to a VPN and compare the two results. If they match, you’ve probably sprung a leak. Here’s what that looks like in practice.
- Test Your Unprotected Connection
Simply go to the IPLeak website and the DNS leak test will start running automatically. The website performs an IP leak test as well. You should be able to see your real IP address and your ISP’s DNS servers, as well as your internet protocol version. Make note of both your IP address and what DNS servers you see, or simply take a screenshot.
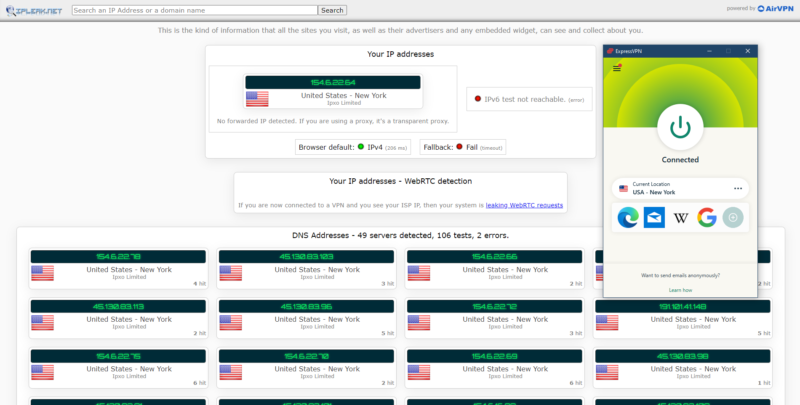
- Connect to a VPN Server and Rerun the Test
Connect to the VPN of your choice and refresh the IPLeak web page. If you are protected, you should see the VPN server’s IP address and your VPN provider’s DNS servers. If you see the same results as before, you have a leaky VPN.
How Do I Use Wireshark to Test for DNS Leaks?
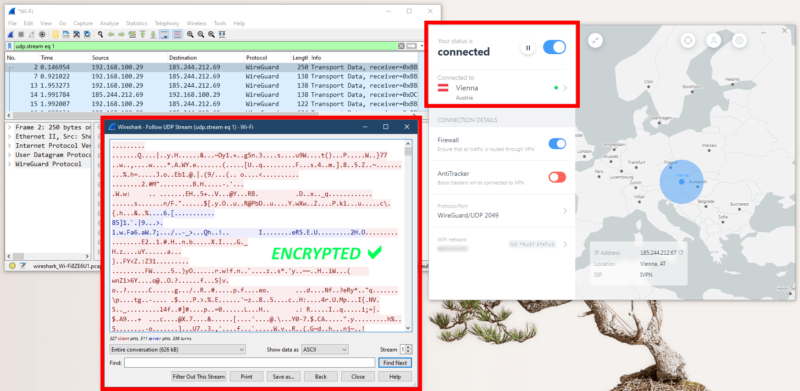
However, if you don’t want to trust a third-party website, you can do your own DNS leak check using packet sniffing software, like Wireshark. Here at Cloudwards, we use Wireshark to test if a VPN encrypts DNS traffic properly. However, the process is a bit more involved than the standard DNS leak test.
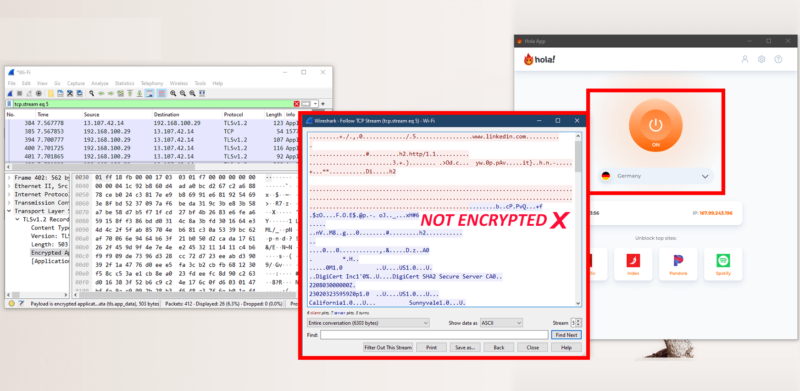
You can see the full process in our guide on how to use Wireshark, but the short version is that you need to analyze a brief stream of data captured while accessing an HTTP website (not HTTPS). If Wireshark shows you using a VPN tunneling protocol (like WireGuard) and packet inspection only shows gibberish, then the VPN is doing its job properly.
How Do I Avoid DNS Leaks?
Avoiding DNS leaks should be easy enough if you use a reliable and secure VPN. As we mentioned, there are several crucial VPN features that work to prevent DNS leaks.
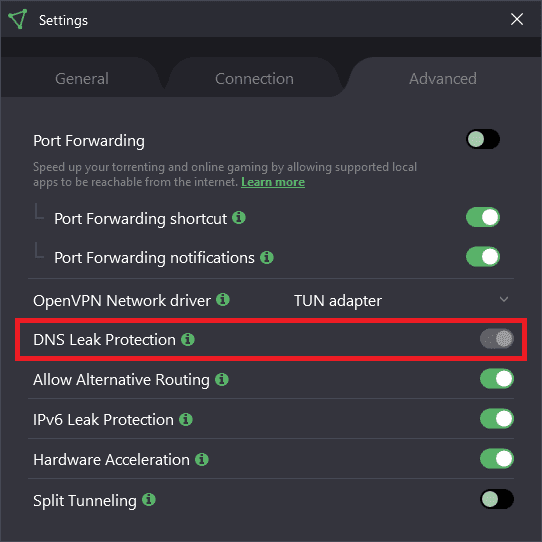
The foremost of these is the aptly named DNS leak protection, which works by blocking all DNS traffic that isn’t directed toward the VPN’s DNS servers.
We advise that our readers never switch off DNS leak protection, if given the choice. Most VPNs have the “option” grayed out or have removed it completely, indicating that it’s a built-in feature that’s integral to the VPN, rather than something you can switch off.
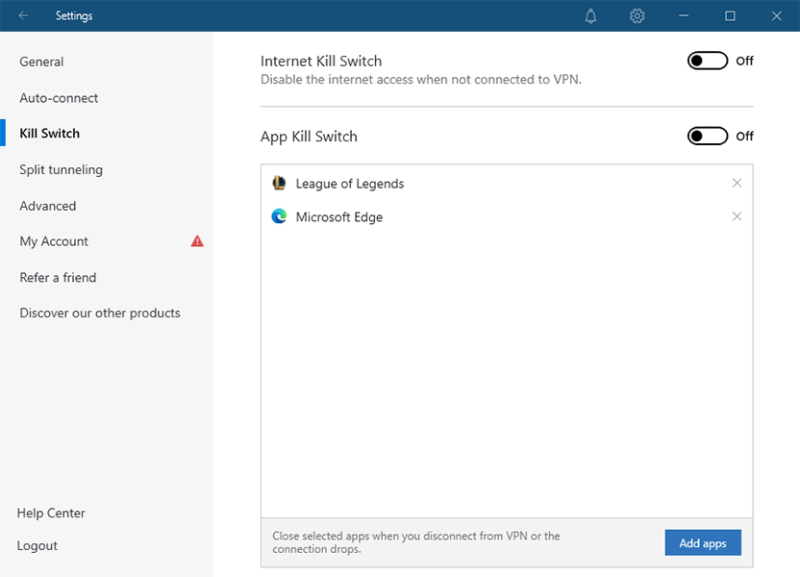
Another important feature is the kill switch, which comes standard with most VPN providers nowadays. Sometimes, a VPN can lose the connection to its servers. In this case, your DNS requests might revert back to your ISP. A kill switch prevents this from happening by completely disconnecting you from the internet when your VPN connection drops.
Final Thoughts
DNS leaks can compromise your online privacy and anonymity, but it’s easy to avoid them. Using a trustworthy VPN provider that’s been proven to protect against DNS leaks is the best way to stop your traffic data from being exposed.
Have you ever used a VPN to change your DNS? Have you ever had a DNS leak when using a VPN? Let us know in the comments below, and as always, thank you for reading.
FAQ
A DNS leak means that your DNS requests are no longer handled by your VPN provider’s DNS server, and your internet service provider can see your web traffic.
An online DNS leak test is the easiest way to detect a DNS leak, though you could also use packet inspection software if you’re more experienced.
The easiest way to fix a DNS leak is to activate the kill switch in your VPN settings. If it’s already on and you’re still experiencing leaks, it might be time to get a new VPN provider.
If you value your online privacy, then yes, DNS leak protection is absolutely necessary.


