Dangers of Public WiFi: Risks and Staying Safe in 2026
Public networks are notoriously dangerous, but people still connect to unsecured WiFi without properly protecting their data. We’ll explore the dangers of public WiFi and show you how to protect your information when you’re on the go.
Public WiFi networks are everywhere — in hotels, coffee shops, restaurants and shopping centers — and they’re a convenient way to access the internet when you’re on the go. However, people often overlook the dangers of public WiFi despite the risks that unsecured networks pose, including data theft and malware deployment.
Fortunately, there are ways to protect yourself on public networks, like connecting to a quality VPN, verifying the hotspot you’re using and not sharing personal data.
For travelers who want to bypass these risks entirely, using a cellular data plan is often a much safer alternative than hunting for a hotspot; checking out eSIM reviews can help you find a reliable provider that offers a private, encrypted connection without the vulnerabilities of shared WiFi.
In this guide, we’ll take an in-depth look at the risks of using public WiFi and how you can keep your information safe when you’re connected.
-
01/06/2025 Facts checked
Article fully rewritten the latest risks, top tips for staying safe and new FAQs.
What Are the Dangers of Using Public WiFi?
Not all public networks are dangerous, but it’s always riskier to connect to unsecured networks than to a secure, encrypted option. Public WiFi can leave your devices and data vulnerable to attack by malicious actors. Below are some of the dangers you could face.
1. Man-in-the-Middle Attacks
A man-in-the-middle (MITM) attack happens when a third party secretly intercepts connections and collects data as it travels to its destination. You connect to an authentic WiFi network, but a hacker reads or even changes traffic before it reaches its destination.
Hackers use packet-sniffers to eavesdrop on your data or manipulate it without your knowledge. The packet-sniffer monitors the information you send while relaying your traffic to its intended destination at the same time, so the attack goes unnoticed.
2. Fake WiFi Hotspots
A hacker may use a mobile hotspot to clone real networks (like the free WiFi at local coffee shops) so you mistakenly connect to a fake network rather than the real one. The hacker can read, store and use all data sent over this fake network, including email contents, online shopping purchases or banking logins.
This is a slightly different version of an MITM attack; rather than intercepting data traveling on a genuine network, the hacker creates their own network. It might have a name similar to an authentic one you’ve used before — like “Free_CoffeeShopWiFi” instead of “CoffeeShopWiFi.”
3. Malware Distribution
A hacker can target public WiFi to distribute malicious software in a few ways:
- Compromising the network: Using a legitimate network, hackers can inject malware, spyware or ransomware into data packets transmitted between users and the internet.
- File sharing: A hacker can detect devices that have file sharing enabled and exploit the open network to access your files and deploy malware.
- Malicious ads: You may get a pop-up window recommending you update apps or visit certain websites, but the pop-up deploys malware when you click on it.
4. Spoofing
Spoofing refers to techniques a hacker uses to impersonate trusted networks, devices or websites with the intent to steal sensitive data. There are several kinds of spoofing on public WFi:
- DNS spoofing: This is also known as login page phishing. A hacker can redirect your traffic to a phishing website by altering DNS (Domain Name System) records. The site may look very similar to the real one, and prompt you to enter login details or other sensitive information.
- ARP spoofing: In this type of MITM attack, the hacker manipulates the ARP (Address Resolution Protocol) so it appears as though your device is connected to the router, when your traffic is really being routed through the hacker’s device.
- MAC address spoofing: A hacker can detect and obtain the MAC (media access control) address of your device and change their device’s MAC address to mimic yours. By using their device to impersonate yours, they can bypass restrictions and get unfettered access to your personal data.
5. Session Hijacking
Session hijacking is a cyberattack in which a hacker intercepts your session ID — usually a cookie that websites use to keep you logged in. This allows them to take over your session and access your account without needing login credentials. The hacker can then make changes as though they are you, like altering passwords or making purchases.
Why Avoid Online Banking on Public WiFi?
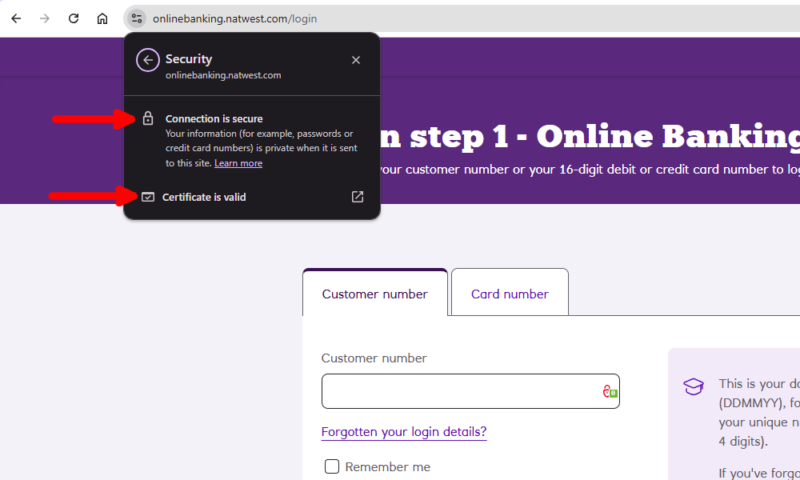
Avoid online banking on public WiFi because public networks often lack proper encryption, so data is sent as plain text. These vulnerabilities make it easier for hackers to infiltrate the network, read the plain text data in your internet traffic and steal your banking information.
You don’t even have to send money or make transactions to be at risk. Something as innocuous as checking your account balance can be enough for hackers to obtain sensitive details. Your account login, associated addresses or credit card details could be stolen, making you a target for identity theft and fraud.
Is It Safe to Use Unsecured WiFi in Hotels?
Generally, unsecured hotel WiFi isn’t safe to use unless you have proper protection in place. While the hotel network may be legitimate, any other guest who has access to the network can also potentially access the data you send and receive. Hackers can also exploit unsecured networks for MITM attacks or to distribute malware.
How to Tell if a Public WiFi Network Is Unsafe?
It can be tricky to tell whether a public network is safe or not, but there are some telltale signs:
- You don’t need a password to connect to the network.
- The network has a generic or suspicious name, like “Free Wi-Fi.”
- Websites don’t use HTTPS or have the padlock symbol to show they’re secure.
- There are pop-ups or redirects to websites that ask for personal information.
- There’s no obvious owner and the network isn’t affiliated with an official business.
- Your speeds are significantly slower when opening apps or sites.
Does a VPN Protect You on Public WiFi?
Yes, a VPN (virtual private network) protects you on public WiFi. It encrypts your connection, making it impossible for anyone to intercept your data or see your online activity — even if the network you’re using is unsecured and unencrypted.
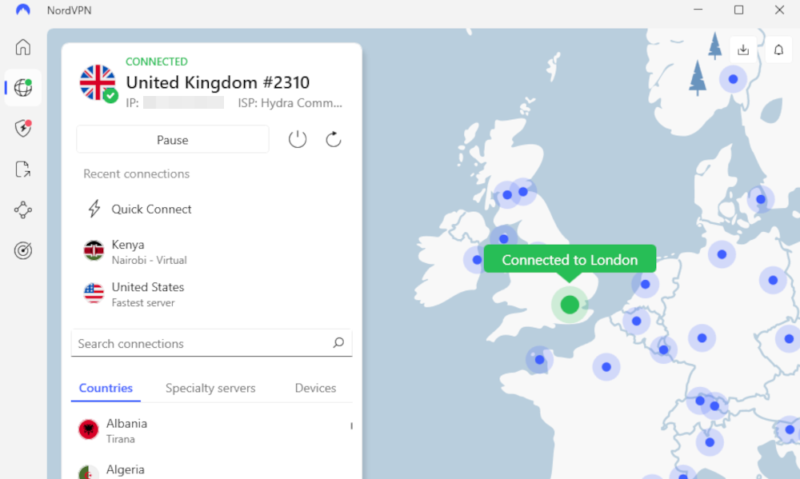
A service like NordVPN can be set to auto-connect to a server when you use an untrusted WiFi network. This way, you don’t have to remember to activate the connection when you’re on the go; you can rest assured your data is safe, even if you don’t manually connect to the VPN. Learn more in our NordVPN review — it’s our top-recommended VPN.
How Can You Stay Safe on Public WiFi?
While there are plenty of reasons to be wary of using public WiFi, there are also plenty of security measures and steps you can take to use public networks safely.
1. Turn Off Auto-Connect
Switching off auto-connect on your laptop or phone prevents your device from accidentally connecting to fake or unsecured WiFi networks. This reduces the chance of you unknowingly connecting to a rogue or compromised WiFi hotspot.
2. Verify the WiFi Network
If you visit an establishment that offers free WiFi, check for the correct hotspot name with the staff or on displayed signage. Where possible, use only free WiFi hotspots that require a password, as this adds a layer of access control. Note that password-protected WiFi is only slightly more secure, especially if the password is on display.
3. Visit Only Secure Web Pages
Secure web pages are encrypted, so even if a hacker has infiltrated the network connection, they cannot read the data sent between your browser and the website. Use only sites with URLs that start with “HTTPS” (the “S” stands for “secure”) and look for the padlock icon in your address bar.
4. Don’t Share Sensitive Information
Avoid sending data like personal identifiers (e.g., your name and address), credit card details or account logins if you’re not on a secure connection. Hackers use these details to build a profile for gaining access to your accounts or committing identity theft.
5. Use a VPN
A virtual private network, or VPN, encrypts your connection even if you use unsecured WiFi networks. A hacker may be able to intercept your connection, but your data will appear indecipherable, as they won’t have the decryption key to access it. The hacker will likely then dump the data rather than try to decrypt it manually.
There are plenty of VPNs available that are great for boosting your public WiFi security. NordVPN is our top recommendation, but you can also take a look at our Surfshark review or ExpressVPN review to see if they’re a better fit for your needs.
6. Switch Off Sharing Settings on Your Device
Make sure you switch off file sharing when using open WiFi networks, as hackers can access your device through shared files, then easily plant infected software or steal personal information. The method for switching off sharing settings differs depending on your device and operating system.
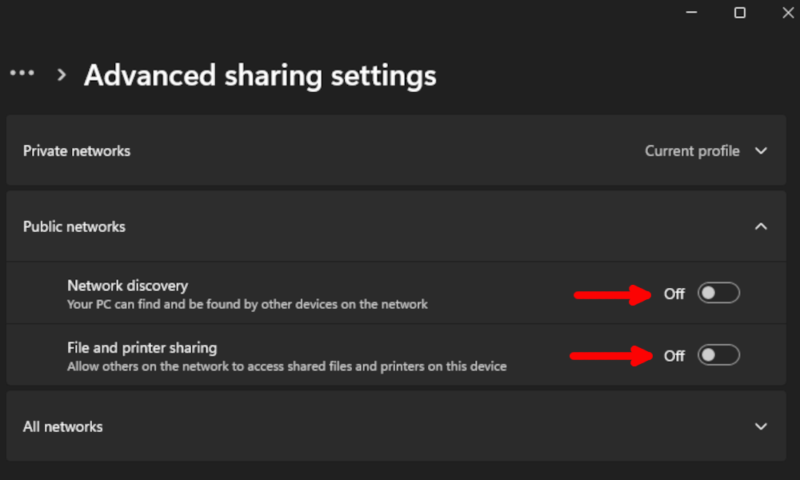
You may be asked whether a network is “public” or “private” when you join it — selecting “public” automatically switches off file sharing.
7. “Forget” the Network Once Disconnected
When your device “forgets” the WiFi hotspot after you disconnect, it won’t automatically reconnect the next time you encounter the same network. This protects you if a previously safe network is compromised or if a hacker sets up an unsecured network with the same name.
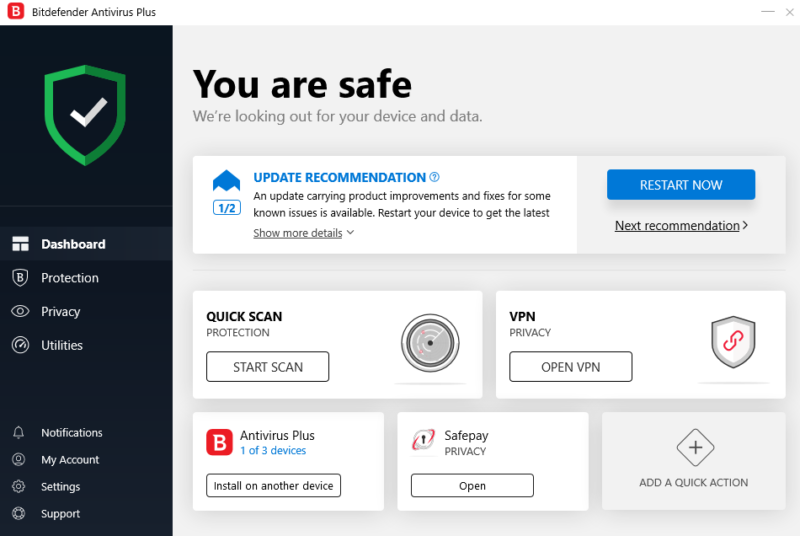
8. Use Antivirus Software
High-quality antivirus software boosts your online security by alerting you to and blocking malware, trojans or other viruses attempting to attack your device. We recommend Bitdefender, as it consistently achieves excellent results in malware testing. You can learn more in our full Bitdefender review.
9. Secure Your Online Accounts
Make sure your online accounts use strong, unique passwords and have two-factor authentication active. These security measures help protect your login credentials for other accounts, just in case one set is compromised by an unsecured public hotspot.
If you find it tricky to remember login details, we suggest getting a password manager. We like 1Password, an affordable, user-friendly app with two-factor authentication, broad platform compatibility and unlimited password storage. Take a look at our 1Password review for more details.
Final Thoughts: Why Is It Not Safe to Connect to Public WiFi Networks?
Public WiFi networks lack the security necessary to keep malicious actors from tampering with the exchange of information. Even so, it’s almost inevitable that you’ll end up using a public network at some point. After reading this guide, you now know to expect internet security issues on public WiFi and can take the proper precautions to safeguard your data.
Do you regularly connect to public networks? Which precautions do you take when using unsecured WiFi? Are there steps you take that we haven’t mentioned here? Let us know in the comments, and thank you for reading.
FAQ: Public WiFi Risks
Not all public WiFi networks are unsafe, but many are vulnerable to malicious third-party interference, as they lack encryption.
No, you shouldn’t use public WiFi for banking, as your sensitive data may be intercepted and stolen by someone who has infiltrated the network.
Don’t send personal information, make any financial transactions (like purchases or checking your bank account) or leave your device unattended while you’re connected to a public WiFi network.
The problems with free WiFi include hacking, data breaches, harvesting, a lack of encryption to protect traffic and slow speeds due to routing many user connections at once.


