Sync.com vs Dropbox in 2026: Which Cloud Storage Provider Wins?
Sync.com and Dropbox compete for your cloud storage subscription dollars. They share some strong similarities; however, the differences between the two services are noticeable in the areas of privacy, affordability and collaboration. We take a look at the two services in our Sync.com vs Dropbox article.
Key Takeaways: Dropbox vs Sync.com
- The main difference between Sync.com and Dropbox is private encryption. Every Sync.com account has zero-knowledge encryption. Dropbox accounts don’t get this.
- Sync.com and Dropbox have excellent file-sharing and syncing features, and both support selective sync through their respective desktop apps.
- Sync.com and Dropbox support integrations with MS Office. Dropbox also connects with Google Workspace.
Sync.com and Dropbox are two of the more prominent names in cloud storage and are among the best cloud storage services available. Each offers excellent cloud features, particularly with regard to file sharing and syncing. However, the differences between the two are significant. We compare them in this Sync.com vs Dropbox article to help you decide.
Consumers choosing between Sync.com and Dropbox will get either private and secure cloud storage or a highly collaborative platform with plenty of external integrations. However, the similarities and differences between the two go deeper. Let’s explore.
- 1
- :
- :
- :
- :
- 2
- :
- :
- :
- :
-
06/24/2022
Updated Sync.com’s plans and pricing.
-
08/09/2023 Facts checked
This article was rewritten with a new format to include updated comparisons, including plans and pricing.
-
09/12/2023 Facts checked
Updated to reflect Dropbox Advanced changing from unlimited to 5TB of storage per user.
-
04/04/2025 Facts checked
This article was updated to reflect the newest changes to Sync.com’s plans and features.
-
07/03/2025 Facts checked
We updated this article to expand on each provider’s collaboration and security features.
-
10/01/2025 Facts checked
We expanded our coverage of each service’s privacy, interface and collaboration features.
-
12/19/2025 Facts checked
This article was updated with more information about Sync.com’s security features and Dropbox’s collaboration features.
How Did We Rate Dropbox vs Sync.com
As a review site, we’ve spent countless hours with more than 100 cloud storage reviews, including Sync.com and Dropbox. As you’ll see in our Sync.com review and our Dropbox review, we rigorously tested each service. Areas we examined include security, privacy, speed and sharing, giving us a thorough understanding to conduct this comparison.
Sync.com vs Dropbox: Similarities & Differences
Sync.com and Dropbox are two of the most popular cloud services, and for good reason. Both are excellent file-sharing and syncing options, and each has a desktop application that supports selective sync. However, the differences between the two are noticeable. Sync.com has zero-knowledge encryption, while Dropbox collects data on how you use its product.
10,000+ Trust Our Free Cloud Storage Tips. Join Today!

- Demystify cloud storage terminology and key concepts in plain language
- Discover easy-to-implement techniques to securely backup and sync your data across devices
- Learn money-saving strategies to optimize your cloud storage costs and usage
| Features | ||
|---|---|---|
| 200GB$2.65 / month(All Plans) 30-days money-back guarantee | 2TB – 5TB$9.99 / month(All Plans) | |
| Review | Review | |
| Sync Folder | ||
| Block-Level Sync | ||
| Selective Sync | ||
| Bandwidth management | ||
| Sync Any Folder | ||
| File Link Sharing | ||
| Link Passwords | ||
| Link Expiry Dates | ||
| Folder Sharing | ||
| Folder Permissions | ||
| Link Download Limits | ||
| Upload Links | ||
| File Previews | ||
| Edit Files | ||
| In-App Collaboration | ||
| Office Online | ||
| Google Docs | ||
| Notes App | ||
| Media Playback | ||
| Mobile Apps | ||
| Deleted File Retention | ||
| Versioning | ||
| WebDAV | ||
| At-Rest Encryption | ||
| In-Transit Encryption | ||
| Encryption Protocol | AES 256-bit | AES 256-bit |
| Client-Side Encryption | ||
| Two-Factor Authentication | ||
| Server Location | EU | US |
| 24/7 Support | ||
| Live Chat Support | ||
| Telephone Support | ||
| Email Support | ||
| User Forum | ||
| Knowledgebase | ||
| Free Plan |
What Are the Similarities Between Sync.com and Dropbox?
On the surface, it may seem like Sync.com and Dropbox don’t share many similarities. However, both handle file sharing and syncing in much the same way and use similar security protocols.
Sharing
File sharing is one of Sync.com’s best features. You’ll see a blue “share” button whenever you hover over a folder or file. If you want to share a folder, you can share it as a link or invite collaborators. Advanced sharing features, like inviting collaborators, let you use email addresses to share the folder. However, the recipient will need a Sync.com account to access it.
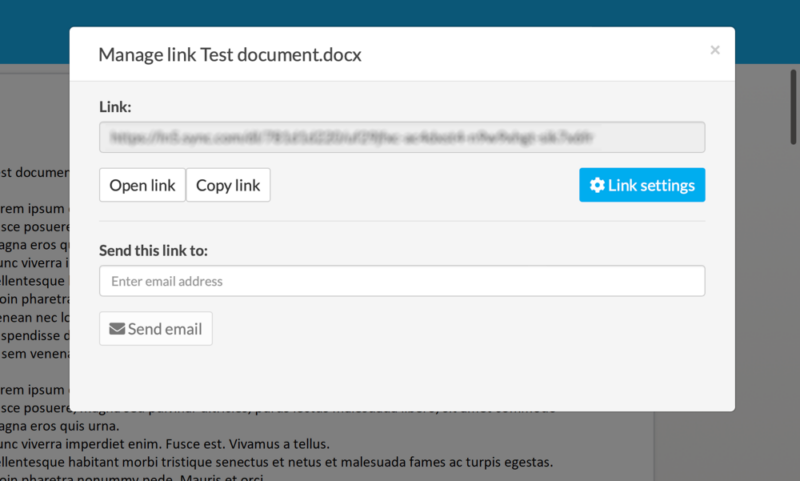
If you create a link, you can securely share files or folders with anyone, as Sync.com encrypts the link address. For files, creating a link is the only sharing option. However, with a free account, you can add up to three password-protected links for an extra layer of security. Other settings, specifically creating a shared folder, require the paid version.
Sync.com also allows users to create password-protected public upload links that enable external collaborators to submit files directly to specified folders without requiring an account, enhancing secure data collection from clients or partners.
Dropbox sharing works well and is a strong part of its service. You can share a folder directly by adding email addresses or creating a link to share as needed. Additionally, you can make the folder view-only or allow editing. Dropbox does not allow additional settings for folder sharing when using an email address.
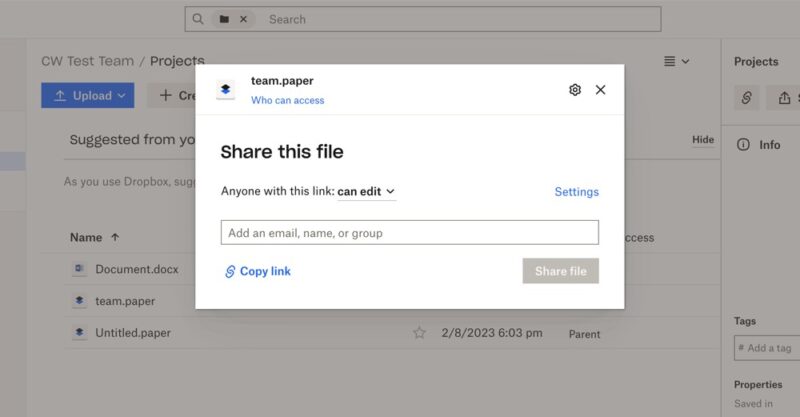
If you create a link to share a folder, you can choose between a link for editing or one for viewing. You’ll also see additional options to set passwords or disable downloads. However, these options are available only with a Professional plan or better. Sharing files with a link offers the same options.
Dropbox also has a special feature called Dropbox Transfer that lets you send files to recipients without them needing to have a Dropbox account. Recipients receive a link to download the files, with transfer limits ranging from 100MB on free accounts to up to 250GB on Business Plus plans.
For international teams, Dropbox Transfer handles large file requests from global partners more efficiently than Sync.com, with dedicated bandwidth allocation for Asia-Pacific regions that reduces upload latencies by approximately 40% during cross-continental transfers.
Dropbox Professional and Business plans also include document-watermarking capabilities, allowing you to add custom watermarks to shared PDFs to protect sensitive information and discourage unauthorized distribution.
Dropbox implements granular transfer quota management for business accounts as well, allowing administrators to allocate different bandwidth limits to various departments or project teams based on their specific collaboration needs and external sharing requirements.
Both Sync.com and Dropbox offer file request functionality, allowing you to create links where others can upload files to your account without needing their own subscription, though Sync.com restricts this feature to paid plans.
Both providers also support LAN sync functionality, which accelerates file transfers between computers on the same local network by bypassing cloud servers, significantly improving syncing speeds in office environments.
Syncing
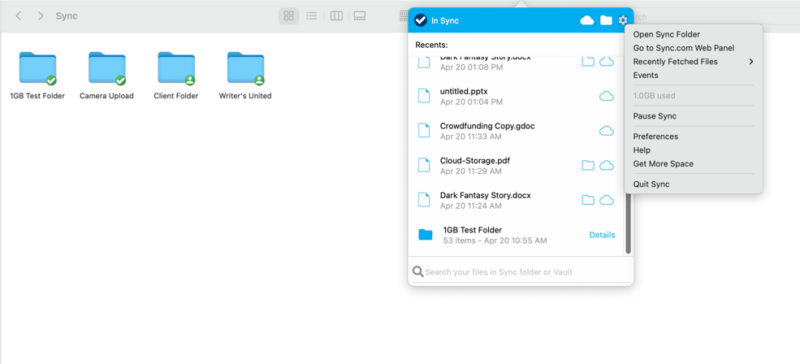
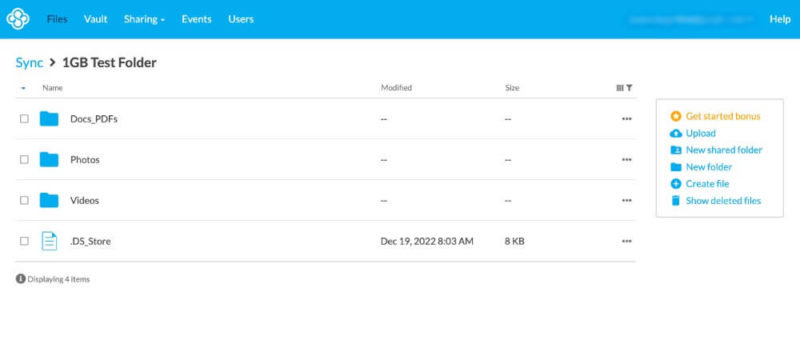
Sync.com has flexible file-syncing features that include selective sync. Selective sync lets you determine what you want to sync with your account. The main folder is called “sync,” and everything you upload falls in this folder.
To access syncing options, you’ll need to download the desktop app. From the “advanced” tab on Mac, you’ll see all the folders currently synced with your account. You can deselect as needed, which helps free up disk space.
Sync.com also offers a unique “sync vault” feature that allows you to store files in the cloud without syncing them to all your devices, providing an effective way to back up files without consuming local storage space.
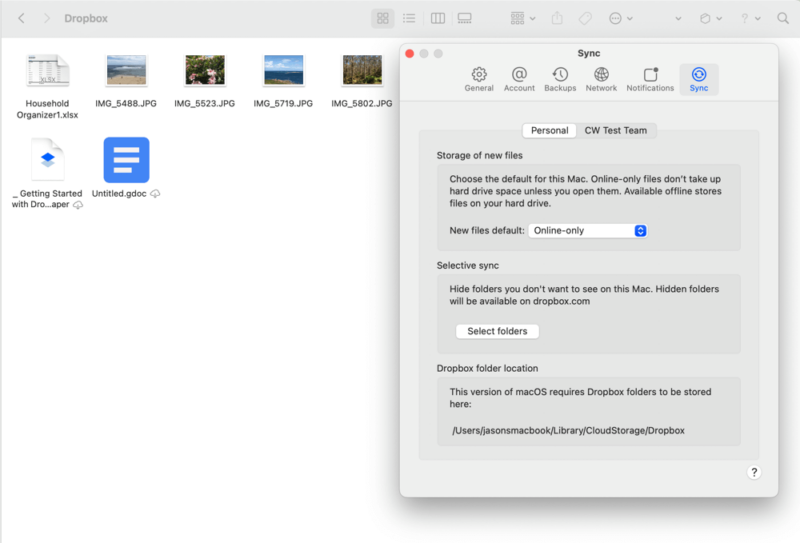
Dropbox has excellent file-syncing features as well, as it supports selective sync and lets you designate whether you want to keep a folder offline or in the cloud. The desktop app shows sync options under the “sync” tab in the settings. You can choose whether you want new files to automatically be online only.
Dropbox utilizes block-level sync technology, which transfers only the modified portions of files rather than the entire file, significantly improving sync speeds for large files with small changes. This differential sync calculates and transmits mathematical differences between file versions rather than changed blocks, reducing bandwidth usage by up to 98% for minor text edits in large files.
While Dropbox’s block-level sync technology works universally across file types, it’s particularly beneficial for Microsoft Office users, as it can reduce sync times for large PowerPoint presentations or Excel spreadsheets by up to 90% compared to Sync.com’s file-level approach.
The “smart sync” feature on Dropbox allows you to see and access all your files in your file explorer without storing them locally on your device, helping you save valuable disk space while maintaining access to your complete cloud library. Smart sync also lets you choose which folders to sync with your account.
Dropbox has recently expanded beyond traditional sync with its dedicated backup feature, which can automatically protect designated folders outside the main Dropbox directory. This feature functions more like a traditional backup service while maintaining the familiar Dropbox interface.
Dropbox also has a “continuous backup” option that creates redundant local archives of critical folders on external drives parallel to cloud storage. Sync.com, on the other hand, treats local storage strictly as a sync destination rather than a comprehensive backup destination.
Both services offer bandwidth management options, allowing you to control how much of your internet connection is used for uploading and downloading files, though Dropbox’s implementation provides more granular control for users with limited internet connections.
During peak usage periods, Dropbox implements automatic bandwidth throttling that can temporarily reduce download speeds for free users, while Sync.com maintains consistent bandwidth allocation regardless of server load, prioritizing stable performance over maximizing concurrent connections.
Desktop Apps
Sync.com’s desktop app is an extension of your account on the web as a virtual drive. It creates a folder on your computer, and everything you designate to sync will have a green check mark next to it. All others will feature a gray icon. Any files you add or work you do with offline access won’t sync with your account.
Note that relocating the primary Sync.com folder on your device can trigger a complete verification of all stored files that can take several hours for large accounts.
Sync.com has now fully launched its CloudFiles feature, which allows users to select files and folders for exclusive storage in the cloud while keeping them visible and accessible on their computer. This helps save local storage space while maintaining access to all your files, similar to Dropbox’s smart sync functionality.
CloudFiles includes advanced file placeholder technology that maintains folder structure integrity even when files are stored exclusively in the cloud, preventing broken file paths when sharing with collaborators. We have a guide that looks at how to use Sync CloudFiles.
upload or download directly from your computer.
Dropbox’s desktop app works in much the same way. It creates a folder showing the items you synced to your Dropbox account. When you choose not to sync a folder, it will not appear on your computer’s sync folder. Folders you designate for online-only access won’t take up additional storage space on your computer.
Unlike Sync.com, Dropbox maintains internal pointers that allow near-instantaneous folder moves on desktop without verification scans. In addition, Dropbox’s Business plans include clipboard history synchronization across all connected devices, enabling seamless copy/paste operations between Windows, Mac and mobile interfaces.
While Dropbox offers native Linux client support across various distributions, including Ubuntu, Fedora and Debian, Sync.com users on Linux systems must rely on web access, as the company has yet to develop a dedicated Linux application. Dropbox even made it onto our list of the best cloud storage for Linux.
work with the folders and files in your account.
Mobile Apps
Both Sync.com and Dropbox offer mobile apps with automatic camera upload features, allowing you to automatically back up photos and videos from your smartphone to your cloud storage.
Both services’ mobile apps support offline editing with conflict resolution protocols, but Sync.com’s implementation preserves all conflicting versions as separate files, whereas Dropbox attempts to merge changes automatically when possible.
Dropbox’s mobile app includes a built-in document scanner with optical character recognition (OCR) that converts images to searchable PDFs, whereas Sync.com requires users to scan documents using third-party applications before uploading.
Dropbox also implements adaptive compression that dynamically adjusts file quality based on network conditions, achieving compression ratios of up to 8:1 for image previews on cellular networks, compared to Sync.com’s static 2:1 compression regardless of connection type.
Dropbox offers instant video streaming through its iOS and Android apps as well, making it convenient to view video content on the go without needing to download large files first.
Security
Security is a strong aspect of Sync.com. It uses AES 256-bit encryption to protect your data while at rest on its servers. Additionally, Sync.com has TLS/SSL encryption protocols to protect data in transit.
The service has also achieved SOC 2 Type 1 compliance certification, further validating its security practices and controls. This certification is particularly important for businesses that need to ensure their cloud storage provider meets strict security standards.
Dropbox adheres to ISO 27001, FedRAMP moderate authorization for government contracts and SOC 1, 2 and 3 compliance, and it uses the same security protocols to protect your data on its servers and while in transit.
Dropbox and Sync.com both support two-factor authentication (2FA). This adds another layer of protection to the login process, which helps keep accounts safe if your login credentials are compromised.
Sync.com has expanded its security capabilities with enforcement policies that allow administrators to require each user to implement 2FA, per group or company-wide, enhancing security governance for business accounts.
In addition, Sync.com employs user action throttling that automatically detects and temporarily restricts abnormal file operations, such as mass deletions or rapid successive uploads from unfamiliar IP addresses, providing protection against compromised credentials that standard two-factor authentication might miss.
Plus, while both services offer password recovery options, Sync.com’s approach is more security-focused, requiring you to set up password hints or recovery in advance, as the zero-knowledge encryption prevents it from resetting your password directly.
These security features protect against common cyberattacks such as brute force or man-in-the-middle attacks. For example, a brute-force attack happens when cyber criminals use trial and error to guess your login credentials.
Sync.com also implements encrypted local cache management that regularly purges temporary file data from device memory after viewing sensitive documents, preventing forensic recovery of classified information even if physical access to the device is compromised.
With Dropbox, on the other hand, business users on team plans can take advantage of single sign-on (SSO) integration, which streamlines the authentication process while maintaining security. Team members can use their existing enterprise authentication credentials to access their Dropbox accounts, reducing password fatigue and simplifying account management for IT administrators.
Both services offer HIPAA compliance for business accounts, though Sync.com includes this feature in more affordable tiers, making it more accessible for healthcare organizations and professionals handling sensitive patient information.
For enhanced security, both services also offer remote device wipe functionality on their business plans, allowing administrators to remotely remove synced files from lost or stolen devices to prevent data breaches.
User Interface
Sync.com keeps its user interface to a minimum, which makes it uncluttered, if not basic. You can find information about your files — like version history — within the menu that populates when you select one. Although you can’t right-click on an item to pull up a menu, Sync.com doesn’t get in your way while you work with your data.
Dropbox’s user interface takes a similar approach, although it populates more on the screen, making it less user-friendly than Sync.com. Ironically, the main “home” tab in the left-hand panel does not show you your main folders and files. Instead, it shows suggestions based on your use of Dropbox and any recent activity. The “all files” tab takes you to your data.
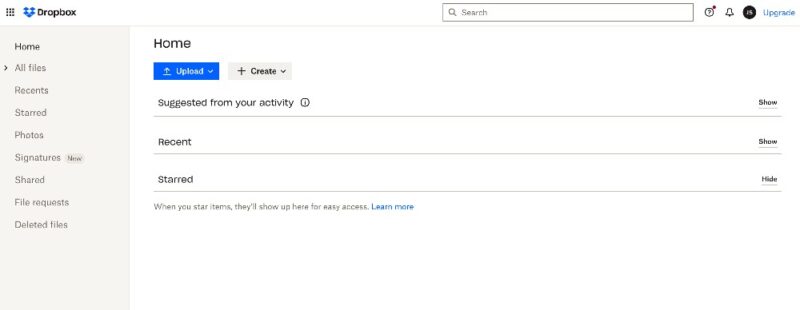
thing you see on the homepage is not your data.
If you need to access a menu for a file or folder, you can right-click on it to pull up the same menu you’d see if you selected the checkbox. A sidebar on the right contains additional information about the selected item, such as recent activity or the last time it was modified.
What Are the Key Differences Between Sync.com and Dropbox?
Privacy is an area where Sync.com and Dropbox differ significantly. Additionally, collaboration and integrations are two areas where each cloud service differs.
Privacy
Sync.com and Dropbox could not be more different regarding how they handle privacy. Unlike Dropbox, Sync.com is zero-knowledge and uses end-to-end encryption for the entire account, meaning you control the encryption keys needed to decrypt your account.
Sync.com applies this encryption to free plans as well, so every account has client-side encryption. With client-side encryption, all files are encrypted before they leave your device, ensuring your data is protected from the moment it’s uploaded to Sync.com’s servers.
This zero-knowledge architecture ensures that only you have access to your encryption keys. This makes it impossible for the company or third parties to access your data, even if requested by government authorities.
Users don’t have to worry about how Sync.com uses their data. In our experience studying privacy policies, there’s nothing that raises a red flag. Sync.com collects only the data it needs to keep your account working.
Dropbox’s privacy policy takes the opposite approach, as it is up front about the data it collects and how it uses it. Dropbox does monitor how you use its service. Additionally, Dropbox does not have zero-knowledge encryption, so someone other than you could potentially access the data you store.
With the provider’s recent purchase of Boxcrytor, however, private encryption is coming to Dropbox business accounts. While this represents a significant improvement in Dropbox’s security offerings, it remains limited to business plans and is not yet available for individual accounts, unlike Sync.com’s universal zero-knowledge approach.
Data residency is another important consideration, with Sync.com storing all data in Canada, while Dropbox uses U.S.-based servers, which may impact users with specific regulatory or compliance requirements.
However, Dropbox also maintains storage servers for eligible users in the United Kingdom, European Union, Japan and Australia, giving it a wider global footprint than Sync.com’s Canadian servers.
While both services offer robust security measures, Sync.com goes a step further with explicit GDPR compliance certification, providing European users with additional legal protection for their stored data.
Last, Sync.com has begun implementing post-quantum cryptographic algorithms in its encryption infrastructure to future-proof against quantum computing threats. Dropbox, on the other hand, has simply published research papers on the topic, with no concrete implementation.
Collaboration
Dropbox users have access to many tools and advanced features that support a collaborative environment. In addition to the ease of sharing, as covered previously, Dropbox has several built-in apps.
Dropbox Paper is a prime example. This web-based word processor allows you to invite others with a Dropbox account to collaborate in real time on a document. Dropbox Paper supports simultaneous editing by up to 20 users with color-coded cursor tracking, allowing large teams to collaborate on complex documents while maintaining complete visibility of who’s making which changes in real time.
Dropbox allows up to 100 simultaneous editors on a single document through Dropbox Paper. It also offers full-text search that indexes the content within documents, images (through OCR) and even video transcripts.
Dropbox Sign lets you send documents with a request for a digital signature or digitally sign documents yourself, making it an excellent tool for professionals who regularly need to handle contracts or agreements. Dropbox Invoice — in alpha testing as of writing — enables you to create and send invoices, which is perfect for freelancers.
In late 2025, Dropbox fully launched Dash, its context-aware AI assistant that connects to all work apps. Dash functions as both an AI assistant and a universal search engine, allowing users to find content across connected applications, get AI-powered answers about their work and organize content with “stacks” — living workspaces that make sharing and collaboration easier.
The self-serve version of Dash allows teams to set up the app without IT involvement, bringing enterprise-grade AI search and content management to businesses of all sizes.
Dropbox has begun integrating Dash’s AI capabilities directly into the core Dropbox experience. This allows existing customers to benefit from smarter search, intelligent organization, time-saving summaries and contextual answers from documents and media stored in Dropbox, without switching to a separate app.
Sync.com, on the other hand, caps real-time collaborative sessions at 15 users per document, potentially limiting large team editing capabilities. In addition, its zero-knowledge encryption architecture limits search capabilities to filename and metadata only.
While Sync.com does support file previews, its system struggles with certain specialized file formats, including AutoCAD drawings, HEIC images and video files over 500MB, requiring users to download these files locally to view their contents.
Sync.com has fewer tools or features in general that support collaboration. However, under the “sharing” dropdown from the menu on your account, you’ll see an option called “team shares.”
Team shares let you invite other Sync.com users to work on the documents in a folder. You won’t be able to collaborate in real time within the Sync.com app; however, changes you make to the folder’s contents will sync between everyone invited.
Team share environments include granular activity reporting that tracks not just access events but also viewing duration metrics. For example, team members typically spend 35% more time reviewing shared documents when access permissions require authentication versus anonymous links.
Sync.com has also enhanced its team collaboration features with group-level share folder management, allowing administrators to assign centralized folder access by user groups rather than individually, which streamlines permission management for larger teams.
For enhanced governance, Sync.com’s business plans include time-limited administrator privileges that can grant temporary elevated access for specific management tasks, automatically reverting permissions after a predefined period without requiring manual intervention.
One significant advantage of Sync.com is that it has absolutely no file size limits for uploads, making it ideal for transferring extremely large files. In contrast, Dropbox has more generous limits than many competitors but still caps file sizes based on your plan.
Sync.com now offers role-based access controls (RBACs) for business accounts, enabling administrators to configure user permissions by group. This provides more granular control over who can access specific resources within an organization’s cloud storage environment.
Sync.com also offers virtual data room functionality with comprehensive audit logs that track document access, view duration and download activity. This makes it particularly valuable for legal firms handling sensitive client documentation or businesses engaged in due diligence processes.
Integrations
As a highly secure service, Sync.com gets a lot of credit for supporting connections to MS Office 365. You can open Microsoft file types — such as Word or Excel — within your Sync.com account. Sync.com will establish a connection to Microsoft Office Online, where you can work on and edit your document. Once finished, Sync.com saves your changes.
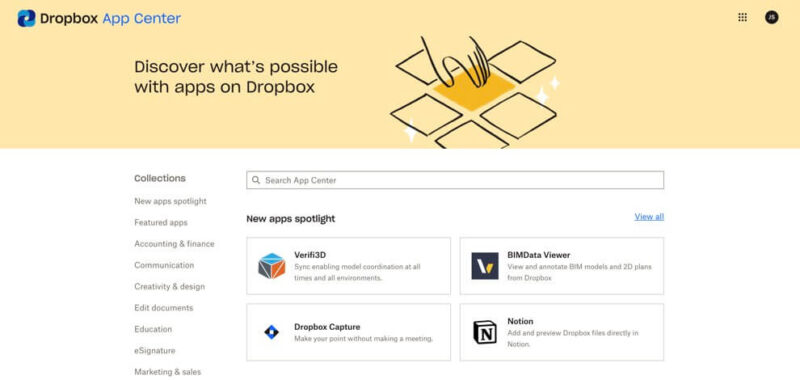
Dropbox supports connections to MS Office and Google Workspace, allowing you to create Google Docs or Microsoft PowerPoint files from your account as if you were using Google Drive (check out our Google Drive review). Additionally, Dropbox has an app center that supports integrations with many popular third-party apps, like Adobe Acrobat DC, Canva and Zoom.
Dropbox also offers comprehensive REST API access for developers to build custom integrations and workflow automations, while Sync.com provides limited API capabilities primarily focused on business account management rather than content manipulation.
Dropbox also recently introduced a Model Context Protocol (MCP) server that allows users to securely search all their content directly within MCP-compatible apps like Claude, Cursor and Goose. This enables users to access and leverage their Dropbox content without switching applications, enhancing workflow efficiency.
Versioning
Sync.com has generous file versions, making it one of the best cloud storage services for versioning. It does not limit how many versions of a file you have, only the number of days Sync.com keeps versions. A free plan gets 30 days; paid plans get either 180 days or 365 days. If you need file recovery, free accounts have 30 days, while paid accounts get a full year.
In addition, Sync.com’s “account rewind” feature includes specialized ransomware detection algorithms that can identify suspicious mass encryption or file modification patterns, allowing administrators to automatically roll back to a pre-attack state without manual file selection. This feature provides comprehensive protection against ransomware attacks and mass deletion.
Note that the rewind feature allows administrators to restore folders to previous states within the retention window but cannot selectively restore individual files within a folder while preserving newer versions of other files in the same location, requiring careful planning before initiating.
Dropbox also has generous file versioning tied to your account, but it is lacking compared to Sync.com. Instead of limiting the number of versions, it just limits how long it keeps them.
When simultaneous edits create version conflicts, Dropbox employs automatic merging algorithms for compatible file types and maintains both versions for others, whereas Sync.com always preserves both versions separately, requiring manual comparison and resolution by users.
Dropbox Basic, Plus and Family get 30 days. Standard, Professional and Dropbox One have 180 days of file versions, while Advanced and Enterprise get a full year. Additionally, paid plans can purchase the extended file history add-on, giving any plan 365 days of versioning.
Pricing
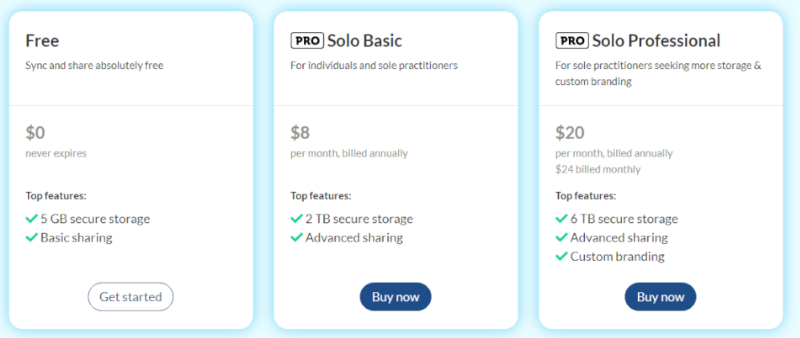
Sync.com has affordable paid plans for individuals. The Solo Basic plan, available only as an annual subscription, has 2TB of storage for $57.60. The Solo Professional has 6TB for $140 annually or $20 monthly. New users get 5GB of free storage, and all Sync.com new plan upgrades have a 30-day money-back guarantee.
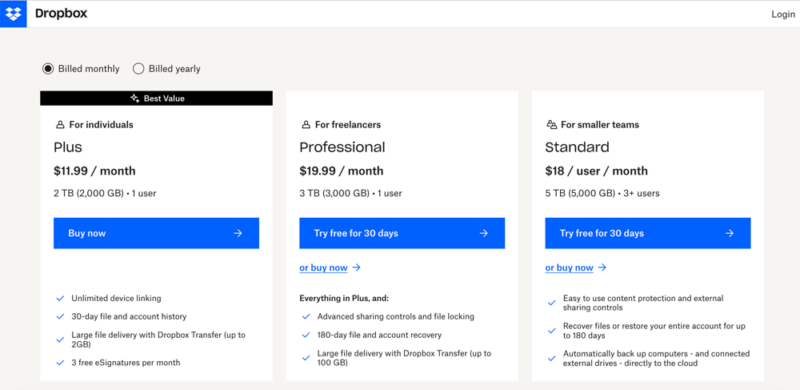
Dropbox has two individual plans if you need more storage than the 2GB of free storage. The Plus plan has 2TB of storage for $119.88 annually or $11.99 monthly. The Professional plan has of storage for per year or monthly.
Sync.com and Dropbox have plans for businesses. Sync for Teams has three plans, starting with 1TB of storage at $72 per user per month for three or more users. Dropbox has several team plans, with a few additional business plans on a different page.
Dropbox business plans start with the Standard plan. It has 5TB of storage for a minimum of three users at $18 per user per month. The Advanced plan has 15TB for $30 per user per month, with a minimum of three licenses.
Which Is Better: Sync.com vs Dropbox?
Sync.com is better than Dropbox overall. It continues to grow its market presence, now serving more than 2.7 million teams globally — indicating strong adoption of its privacy-focused cloud storage solution.
Although Dropbox is the better choice overall for collaboration and productivity, Sync.com has far better protections for user privacy and cheaper pricing.
Sync.com has just enough flexibility in its service while offering private encryption for everything contained in an account. Integration with MS Office helps keep it competitive with cloud storage services focused on collaboration and productivity. Additionally, Sync.com’s file versioning is very generous, even on its free plan.
On the other hand, Dropbox has better collaboration and productivity tools. It has connections to MS Office 365 and Google Workspace, comes with several homegrown apps and has an app center with additional external connections.
We Recommend Sync.com if You Want…
- Private encryption: Sync.com has zero-knowledge encryption that protects accounts from unauthorized access.
- More control with file versioning: Free accounts with Sync.com get 30 days of file versioning. Paid accounts get 180 or 365 days.
- Affordable storage and better value: Sync.com’s paid plans, including Sync for Teams, are affordable. Additionally, the Teams Unlimited plan has unlimited storage space.
We Recommend Dropbox if You Want…
- Business cloud storage: Dropbox’s business plans are geared toward freelancers or teams, with plenty of storage, though with no unlimited options.
- Third-party integrations: With integrations including MS Office, Google Workspace, Zoom and Adobe, Dropbox supports a team’s preferred productivity tools.
- More features and built-in apps: Dropbox has several homegrown collaboration apps, such as Dropbox Transfer, Paper and Sign.
If You Want to Consider Other Services, Check Out…
pCloud is an excellent cloud storage solution with strong security and sharing. Subscribing to pCloud Crypto unlocks the encryption folder located in an account. Anything stored in this folder has zero-knowledge, client-side encryption. We cover more in our pCloud review.
MEGA is another service that, like Sync.com, offers zero-knowledge encryption for the entire account, even free ones. It has a robust 20GB free version, which is a good amount of cloud storage to do more than just give it a try. To learn more, check out our MEGA review and Sync.com vs MEGA guide.
Box gears most of its plans for businesses and supports connections to Google and Microsoft. It’s a very secure cloud service with built-in apps like Box Notes. Read our Box review to see all the details.
Egnyte is one of the most customizable business cloud storage solutions. Businesses have a wide range of settings to choose from. It rates highly as one of the best business cloud storage options. Our Egnyte review goes into more depth.
- 1
- :
- : 150 GB
- :
- :
- :
- :
- 2
- :
- : 100 GB
- :
- :
- :
- :
- 3
- :
- :
- :
- :
- 4
- :
- :
- :
- :
- 5
- :
- :
- :
- :
The Verdict: Why We Think Sync.com Wins Overall
Sync.com edges out Dropbox with its stringent private encryption and connections to Microsoft apps. Its file sharing and versioning are excellent features. It’s also more affordable and offers better value for money in terms of storage space, making it the better service for most users.
However, Dropbox is the clear choice for collaboration and productivity and would suit business users better. We also have a Sync.com vs OneDrive comparison if you’re interested in comparing additonal services.
Have you used Sync.com or Dropbox? Did we leave out a great cloud feature? What other cloud storage providers would you recommend? Let us know in the comments section below. Thanks for taking the time to read our article.
FAQ: Dropbox vs Sync.com Comparison
With zero-knowledge encryption and a privacy policy that protects its consumers, Sync.com is more secure than Dropbox. However, Dropbox recently purchased Boxcryptor with the intent to bring private encryption to its business plans.
Dropbox is a solid option for businesses that want to maximize collaboration and productivity. Sync.com offers excellent privacy and zero-knowledge encryption for every account, even free ones.
OneDrive competes with Dropbox for cloud storage that enhances collaboration and productivity. It integrates seamlessly with other Microsoft products, such as Word and Excel.


