How to Encrypt Cloud Storage in 2026: Secure Your Stored Files With Encryption
If you are worried about the privacy of your cloud data, you’ll want to make sure that it is encrypted. In this article we will explain how to encrypt cloud storage using zero-knowledge cloud service providers and third-party encryption software.
Cloud storage is a great way to store your information and share files with others. However, if you are worried about the privacy and security of your data, it is best to make sure that it is protected by zero-knowledge encryption. This guide on how to encrypt cloud storage data will help you make your cloud storage safe.
While some cloud storage services have this utility in-built, like with Sync.com, some do not have it at all and others might own your encryption key. If the cloud service provider holds your encryption key, it could potentially access your data and share it with advertisers or government authorities. Keep reading to learn how to encrypt your cloud storage, plus the best providers for the task.
-
11/30/2022 Facts checked
Updated this guide to include information about Boxcryptor’s asset acquisition by Dropbox.
-
04/05/2023 Facts checked
Updated to replace Boxcryptor with Cryptomator and NordLocker after Boxcryptor assets were acquired by Dropbox.
What Are the Two Ways to Encrypt Cloud Storage?
There are several ways to encrypt cloud storage. The first way is to simply use a cloud service with zero-knowledge cloud file encryption. The only thing you ended to do to secure your files with one of these services is to upload your files. It’s simple enough that anyone could do it with no previous cloud storage experience.
However, if you have your heart set on an unencrypted service, you can encrypt files before uploading to cloud using encryption software. This kind of software encrypts your files while they’re on your device.
10,000+ Trust Our Free Cloud Storage Tips. Join Today!

- Demystify cloud storage terminology and key concepts in plain language
- Discover easy-to-implement techniques to securely backup and sync your data across devices
- Learn money-saving strategies to optimize your cloud storage costs and usage
Some of them can integrate with cloud services to automatically upload your files to the cloud, while others provide their own cloud storage. Others still provide no cloud functionality at all and simply encrypt your files, requiring you to manually upload your files to the cloud.
What Are the Best Zero-Knowledge Cloud Storage Services?
There are a variety of cloud storage providers with built-in zero-knowledge encryption for cloud storage. This is the easiest way to ensure the privacy of your data on the cloud. The following are five of our best picks for cloud file encryption.
1. Sync.com
Based on its security, features and ease of use, Sync.com tops our list of the best cloud storage services. Its one downfall is that it’s not the fastest cloud storage option.
It comes with a 5GB free plan. You can also choose one of their paid plans to increase the available storage space from 2TB up to unlimited. Overall, it can be a great fit for your encrypted cloud storage needs. You can check our full Sync.com review for more details.
- 5GB
- 2TB
More plans
- 6TB
- per user, per month, billed annually
- 1TB
- Priced per user (3 users minimum)
- Unlimited GB
- Minimum 100 users, custom requirements, account manager, training options
2. pCloud
pCloud is another great service that gives Sync.com a run for its money in our head-to-head Sync.com vs pCloud comparison. It gives you up to 10GB of free cloud storage and has convenient monthly, annual and one-time payment plans for more storage.
However, pCloud requires an additional payment of $4.17 a month (billed annually) for its zero-knowledge encryption service, pCloud Crypto. It also requires you to put your files in its designated crypto folder for encryption. If you don’t mind this slight difference in cost, you can read our full pCloud review.
- 10GB
- 500GB
- 2TB
More plans
- 10TB
- + FREE Encryption
- 2TB
- + FREE Encryption
- 10TB
- Price per user (minimum 3)
- 1TB
- Price per user (minimum 3)
- 2TB
- Encryption for pCloud Drive
3. Internxt
Internxt is an affordable, open-source cloud storage provider with built-in zero-knowledge encryption. It supports password protection and expiry dates for shared links, making it a solid choice for privacy-conscious users on a budget. Speeds have improved massively since 2023, with average uploads now clocking in at around 8 minutes for our test files.
The service also offers scheduled backups with flexible upload intervals. However, it does struggle with large files and zip archives, and our stress tests revealed some sync instability during heavy workloads. If you want an affordable encrypted storage option for everyday files, you can read our full Internxt review.
- 1GB
- Post-quantum encryption Zero-knowledge encryption Two-factor authentication Backup your computer Password-protected file sharing Encrypted VPN Antivirus
- 1TB
- Everything in Essential plus; Cleaner Invite, share & collaborate File versioning (coming soon) Cleaner
- 3TB
More plans
- Everything in Premium plus CLI & WebDav support NAS & Rclone support Meet Mail (coming soon)
- 5TB
- Annual Price is per user
- 1TB
- Annual Price is per user
- 2TB
4. Proton Drive
Proton Drive is a privacy-focused option from the makers of Proton Mail, offering end-to-end encryption under Swiss jurisdiction. It passed our 1 million file stress test without issues and showed stable, fast transfers averaging around 25MB/s. Our sync tests confirmed real-time collaboration works smoothly with its integrated Proton Docs editor.
The service offers password protection and expiry dates for shared links. However, the free plan limits version history to just 10 versions or 7 days. Proton Drive is a solid option if you want a secure Google Drive alternative. Check out our full Proton Drive review.
- 5GB
- 200GB
- 500GB
More plans
- 2TB
- 3TB
- per user
- 1TB
- per user, minimum of 2 users
- 1TB
- 1TB
5. Icedrive
While a relatively new cloud storage service with fewer features than its competitors, Icedrive is a great budget option with a stunning user interface. It gives you 1TB of cloud storage with client-side encryption for as low as $4.92 a month.
Unfortunately, Icedrive still lacks a lot of collaboration options that you’ll find with other providers. However, if you are looking for a secure, value-driven cloud storage provider, you can read our full Icedrive review.
- 10GB
- 1TB
- 3TB
More plans
- 5TB
- 2TB
- Additional 1TB storage for users who purchased the Lifetime Plan
- 1TB
- Additional 5TB storage for users who purchased the Lifetime Plan
- 5TB
Add-on Zero-Knowledge Cloud Storage Encryption Software
Depending on the service, your cloud storage provider may not have in-built zero-knowledge encryption. Additionally, if you have an unencrypted backup of your files lying around, you might want to encrypt it before uploading it to a cloud storage or online backup service. A dedicated cloud storage encryption software can help you out in either of these cases.
There are a handful of free encryption services to choose from, but be sure to use a trustworthy encryption service. Below, we will talk about cloud storage encryption using Cryptomator and NordLocker.
How Do You Use Cryptomator to Encrypt Your Files?
Cryptomator is a free, open-source solution for encrypting cloud storage files. This donation-based service is easy to use, allowing you to create virtual drives and store files within them. (Read our Cryptomator review for more specifics.)
Unlike the other encryption services, Cryptomator uses transparent encryption, whereby you can see the hierarchy of how your files are encrypted.
If you sign up with Cryptomator, you might be asked for a donation and you can easily choose the amount to donate to keep this solution running. However, if you choose not to donate, Cryptomator is not too pushy about it. Here’s how you can use Cryptomator to encrypt your cloud information.
- Download and Install Cryptomator
Download the Cryptomator software from its official website. Once download is complete, open the installer file to install the program on your computer.
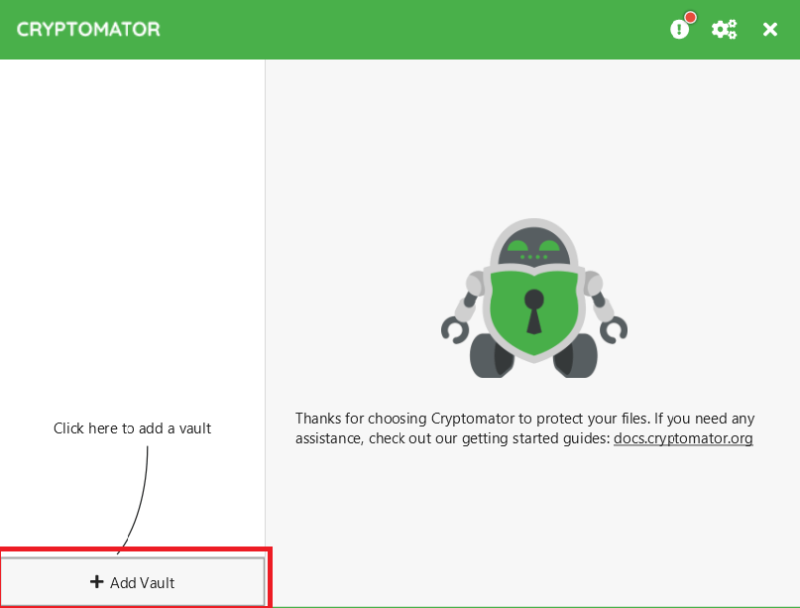
- Launch Cryptomator and Create the Vault
You can launch Cryptomator from the shortcut created on the desktop or the Windows “start” menu. Once launched, you can click on the “+” symbol to create a new vault.
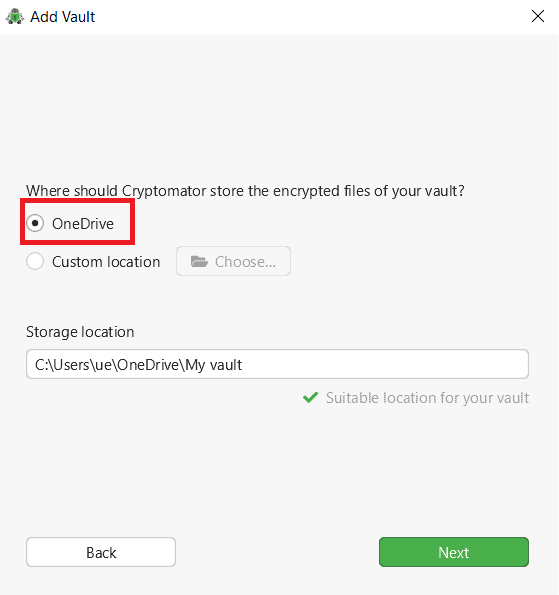
- Name the Vault and Choose the Storage Location
You can choose a name for the vault, the storage location and a password. Choose OneDrive as the storage location (or the other cloud storage service that does not have built-in encryption) to encrypt your data.
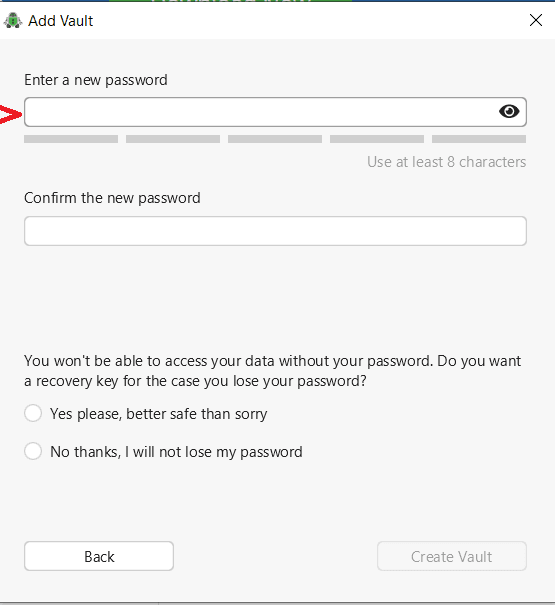
- Set Password
Now you can choose a password. Make sure to keep your password safe. You can also use a secure password manager.
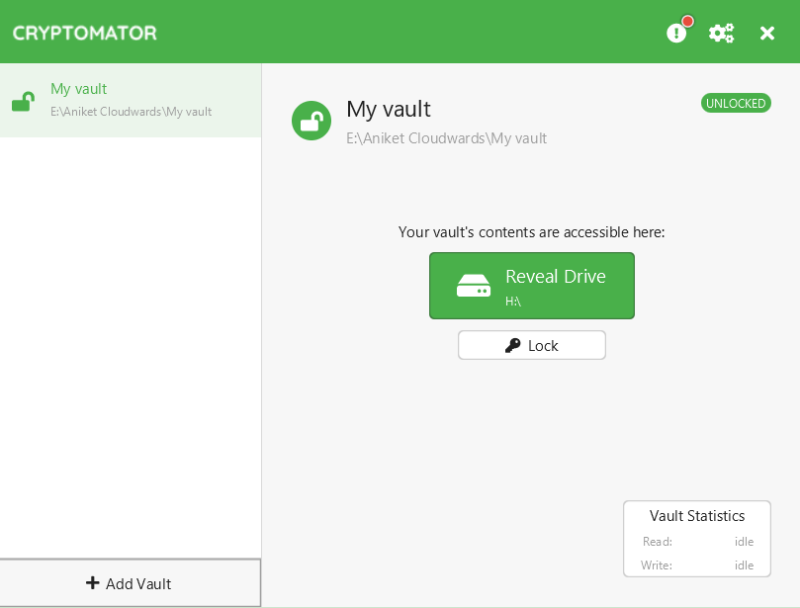
- Launch the Vault
To view the encrypted files in your vault, you can unlock the vault using the password set in the previous step. Your vault will open in Windows Explorer. When you are done viewing the files, you can lock the vault again to keep your files protected. Once locked, no one else can decrypt your files, not even the cloud service provider.
How Do You Encrypt Files Before Uploading to Cloud Using NordLocker?
NordLocker is another easy-to-use tool for securing files stored on the cloud. While NordLocker has its own cloud storage service, it can also be used to encrypt data on your preferred cloud service such as OneDrive. Read our NordLocker review for more info. Here’s how to encrypt files before uploading to cloud.
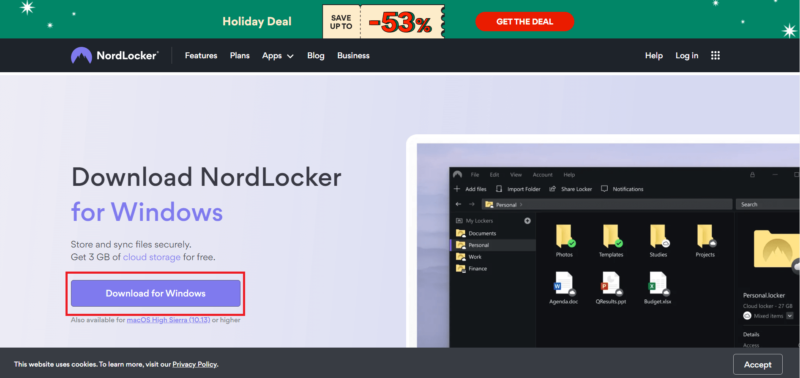
- Download and Install NordLocker
You can download the software from the NordLocker official website. Once downloaded, you can install the software on your device by following a few easy steps.
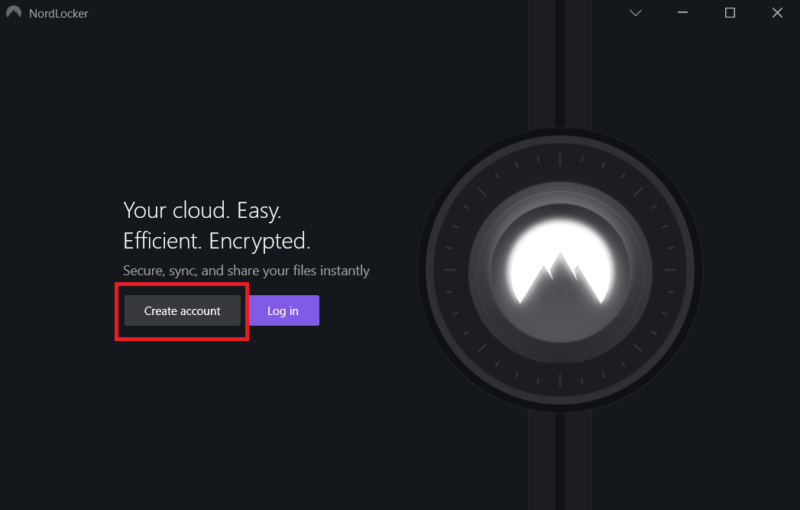
- Create NordLocker Account
Once NordLocker is successfully installed on your PC, it will launch automatically. You can also launch it from the desktop shortcut or the Windows “start” menu. You’ll then be prompted to create an account.
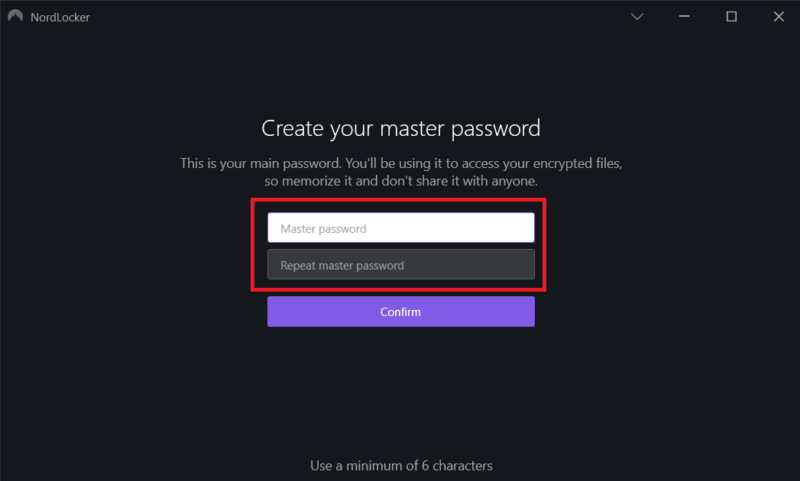
- Create the Master Password and Save the Recovery Key
Once the account is created, you can choose a password. You will also be provided with a recovery key. Make sure to keep your password and the private key somewhere safe or use a reliable password manager. If you lose your password and the key, no one can help you recover the data.
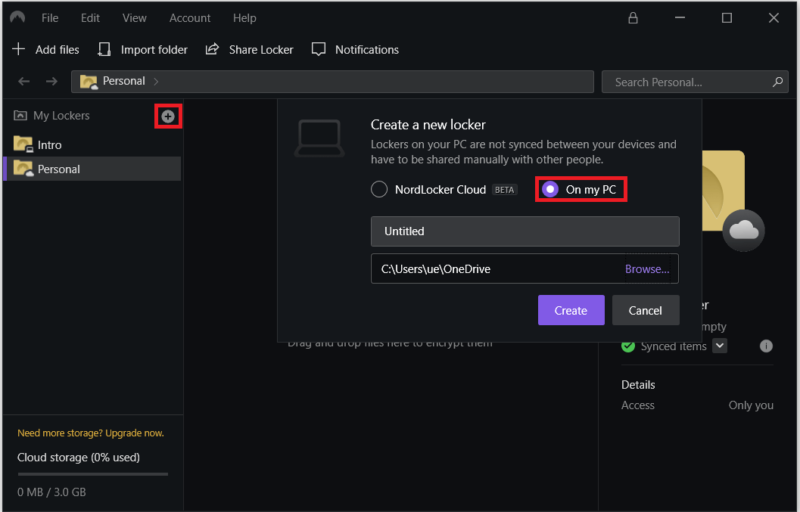
- Add a New Locker and Use OneDrive as the Storage Location
Now, you can add a new locker by clicking on the “+” symbol that appears on the left side next to “my lockers.” Choose OneDrive (or your preferred cloud storage provider) as the storage location to encrypt the files within the service.
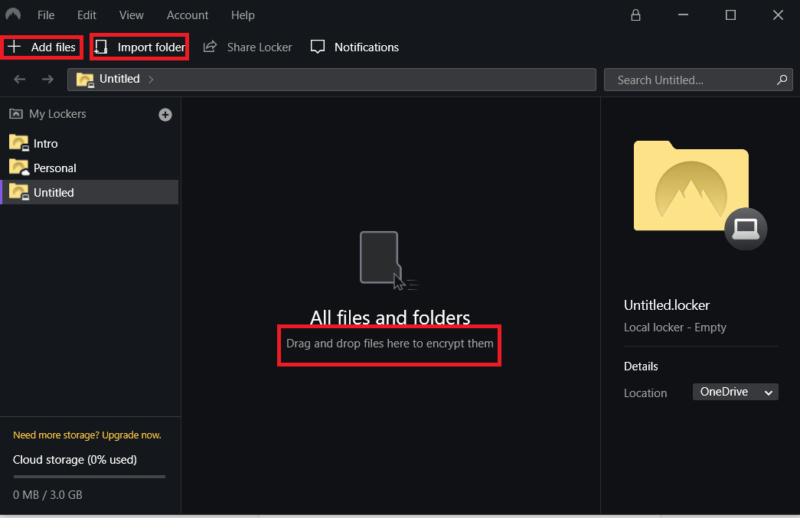
- Encrypt the Files
Once the locker is created, you can drag and drop the files here or add the files and import a folder. The files stored will automatically get encrypted. You will need your password to view the files and no one else can decrypt them.
Why Should You Encrypt Your Cloud Storage?
Your data on the cloud is susceptible to risks such as data leaks, spyware and possibly surveillance from your own government. If your cloud storage provider holds your encryption keys, it can technically access your data. Providers such as Google (Google Drive) and Microsoft (OneDrive) even monitor your data for any illegal content.
However, if you encrypt your files yourself, you’re the only one that holds your encryption keys. This means that only you will be able to access your data. This also goes for zero-knowledge cloud services, whose applications encrypt your data while it’s still on your device, and unencrypted files never reach their servers.
Zero-Knowledge Cloud Storage Services vs Third-Party Encryption
A zero-knowledge cloud storage provider encrypts everything you store without requiring any extra work on your part. It’s certainly the easier way to encrypt files, but it’s not without its faults. For example, it’s usually slower than regular cloud storage.
Zero-knowledge encryption also makes it difficult for providers to include relatively simple features, like file previews, and collaboration is usually out of the question, barring rare examples like Sync.com and Woelkli.
Third-party encryption, on the other hand, allows you to encrypt files before you upload them to the cloud. While this is a great solution to possible data leaks, it’s not the most practical method as it adds an extra step to the process. However, it does take out the trust factor, since you know for sure that your files are getting encrypted.
Final Thoughts
If you are not worried about the privacy of your data, storage services without zero-knowledge encryption that offer fast block-level syncing and easy file sharing might suit you more. However, if you store sensitive data on the cloud, you should make sure that the data is secure.
You can use zero-knowledge cloud storage providers such as Sync.com and Icedrive. However, if you prefer using other providers such as Dropbox, Google Drive and OneDrive, you can look at third-party encryption software such as Cryptomator to secure your data on the cloud. Here’s also our list of the best TrueCrypt alternatives, in case you’re looking for a free, open-source encryption software.
Have you encrypted the information on your cloud storage? Which of the two methods did you use? Let us know in the comments. Thanks for reading.
FAQ
You can either use a zero-knowledge cloud service to secure your data automatically, or use an encryption software to encrypt the files yourself.
If you store sensitive data on the cloud or you’re worried about the privacy of your data, you might want to encrypt your files before storing them on the cloud.
You can easily encrypt your cloud storage using encryption software such as Cryptomator. For this, you will have to download and install the service’s software on your desktop.
Yes, using encryption software such as Cryptomator or NordLocker, you can select OneDrive as the vault/locker location, which will encrypt your files on OneDrive.






![Video thumbnail for the video: I Tested Proton Drive to See If It's as Private as It Claims [2024 REVIEW]](https://img.youtube.com/vi/XWmsFdm-VLg/maxresdefault.jpg)
![Video thumbnail for the video: Ultimate Icedrive Review [2024 Pros and Cons Revealed]](https://img.youtube.com/vi/iVGsDxYVV-Y/maxresdefault.jpg)
