What Is Ransomware? 2026 Guide on Types, Variants, Protection Tips & More
With the rate of ransomware attacks rising across the globe, it is vital for every consumer and organization to understand what it is, how it works and the best ways to avoid becoming a victim. Read our “what is ransomware?” guide for these insights and more.
According to Cybersecurity Ventures, ransomware resulted in global financial costs of $20 billion in 2021. 2 This figure is expected to grow to $42 billion in 2024 and $265 billion by 2031, indicating that ransomware will remain an online security threat for years. In this guide, we will answer the question, “What is ransomware?” and equip you with the knowledge to protect yourself or your organization.
We’ll start by providing a thorough definition of ransomware and delving into the mechanisms behind it. Then, we’ll offer tips on how to respond to ransomware threats and what to do when you fall victim to ransomware. We will also provide a list of ransomware infection types and examples of variants — essential information for foiling ransomware attacks.
To learn more about how to protect yourself from ransomware, check out our roundup of the best antivirus software and our list of ransomware protection tips.
-
03/11/2024 Facts checked
Rewritten to include more detailed tips.
-
08/16/2024
Updated the article to add custom graphics.
What Is Ransomware in Cybersecurity?
Ransomware is a type of malware designed to withhold access to a victim’s computer files through encryption with the intent of coercing the victim to pay a ransom. Ransomware operators often spread the malware throughout a network, making it impossible to perform any operations within an entire organization.
In the past, ransomware attacks simply blocked access to the victim’s files, so victims were able to minimize the consequences of attacks through regular or continuous data backups. However, ransomware perpetrators have begun employing more effective methods of soliciting ransoms, even when the victims have data backups.
These new methods include double-extortion and triple-extortion attacks. In a double-extortion ransomware attack, the attacker threatens to expose the victim’s data online. Triple-extortion attacks include a third layer of coercion, which usually involves threatening to destabilize the victim’s infrastructure by overwhelming it with internet traffic in a DDoS attack.
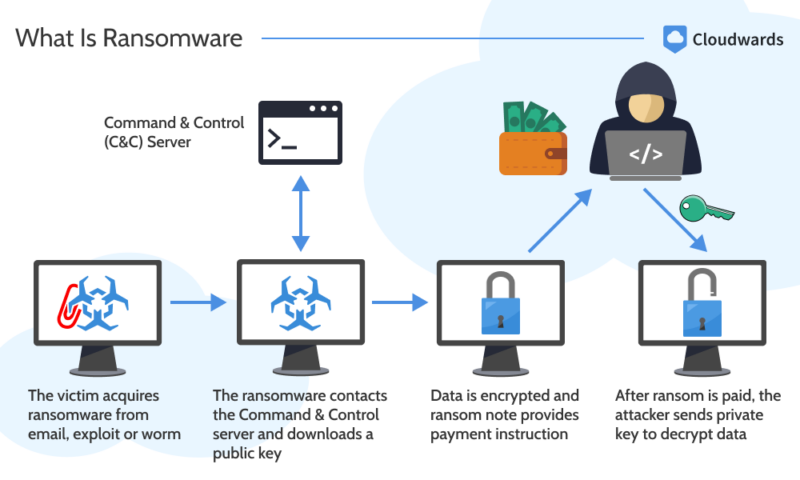
How Do Ransomware Attacks Work?
To help you understand how ransomware works, we’ll explain how it spreads and how the complex nature of the attacks makes them difficult to prevent.
How & Why Does Ransomware Spread?
Ransomware typically employs asymmetric encryption. This is a type of encryption that consists of a pair of keys known as a public key (encryption key) and a private key (decryption key). Using a uniquely generated public key, the attacker encrypts the victim’s files. A unique private key is also generated to decrypt the files. However, the victim only receives it after paying the ransom.
Cybercriminals distribute ransomware through various means. One way is through phishing attacks, whereby attackers co-opt reputable identities to trick each victim into opening an email containing a malicious attachment.
Attackers also spread malware through online advertisements. By compromising legitimate ad networks to serve malicious advertisements, criminals redirect users to websites that are infected with ransomware or infect their computers directly with the ransomware payload. Some mobile ransomware is optimized to attack phones and tablets.
Cybercriminals can also use ready-made exploit toolkits to target software vulnerabilities in a system or code. When a user visits a malicious website, these exploit kits are designed to scan their system for vulnerabilities and launch the ransomware payload against any weaknesses that come up.
Why Aren’t More Ransomware Attackers Caught?
It’s difficult to apprehend ransomware attackers for many reasons. Most ransomware attacks happen on an international scale, which means that U.S. law enforcement agencies must work with the law enforcement agencies of other nations, complicating the investigation process. Our cybersecurity statistics article illustrates how quickly ransomware has grown.
There’s also been a rise in the complexity of malicious software itself, broadening the range of threats that can manifest in a single attack. The significant number of ransomware attackers dispersed across various nations also makes it difficult for law enforcement agencies to trace attacks and bring the perpetrators to justice.
What Is RaaS?
RaaS is an acronym for Ransomware as a Service. RaaS enables ransomware operators to minimize risks by distributing their creations to third parties instead of using them directly. The buyers coordinate the ransomware campaigns, while the operators receive a commission for the wares sold.
These ransomware vendors are indirectly responsible for a large portion of ransomware operations. To generate revenue, RaaS operators offer buyers access to their creations through various models, including monthly subscriptions, affiliate programs, one-time license fees and pure profit sharing.
Should I Pay the Ransom?
Experts have opposing views on how ransomware victims should respond to a ransom demand. While some advise that ransom payments should never be made, others caution that there are gray areas.
“It’s an enormous mistake to think that paying ransomware demands will solve anything. The initial payment is only for the start of things,” said Etay Maor — an adjunct professor at Boston College in cybersecurity — in an email to Forbes. 2
To Maor, paying ransom demands is inadvisable because it doesn’t guarantee that cybercriminals will release the victims’ data, and it encourages repeat attacks. “The bad actors now know that your system is insecure and that you will pay a ransom,” he said. 2
On the other hand, some experts suggest that paying the ransom is the most reasonable step in some cases. For Matthew Baker, a practice group chair for privacy and cybersecurity at Baker Botts in San Francisco, time-sensitive company data held at ransom may necessitate payment to ensure continuous access to essential services.
According to Baker, “There may be scenarios where payment is necessary or advisable. Organizations — usually critical infrastructure — providing essential services may not have time to restore operations or services, and the impacts may necessitate payment.” 2
Since restoring data from backup files takes time, paying quickly may be the only way to keep businesses online. Baker also states that targets should pay the ransom when bad actors have access to sensitive proprietary information, which can be detrimental if released.
Ransomware Infection Types
Ransomware infection types vary according to the extent to which they affect the victim’s computer.
Locker Ransomware
Locker ransomware restricts access to all computer functionality besides the mouse and keyboard (so victims can send their ransom payments). Cybercriminals infiltrate the target’s computer by using social engineering to trick them into downloading malware. To pressure the target into paying the ransom, the hackers may display a countdown clock on the user’s screen.
Crypto Ransomware
Also called encrypting ransomware, this type locks the user’s computer by encrypting important files. The attacker then demands a ransom payment in exchange for the decryption key. Crypto ransomware can infect the target’s computer through various means, including malicious websites, phishing emails and advertising. Ryuk is a prominent example of crypto ransomware.
Leakware/Doxware
Leakware ransomware attacks go a step beyond encrypting the target’s computer files. They threaten to leak the encrypted files to the public if the ransom isn’t paid within a specific period. Like crypto ransomware, leakware takes away the encryption key and only provides it if the user pays the ransom.
Scareware
Scareware tricks the user into believing that their computer has been infected with malware when it actually hasn’t been. The user sees a pop-up stating that their computer has been infected and that they should pay a fee or purchase antivirus software to fix the problem. Following any of these steps gives the cybercriminal access to your data for real.
Ransomware Variant Examples
Ransomware variants show different distribution methods and types of ransom notes.
WannaCry
WannaCry ransomware first circulated in a May 2017 cyberattack that targeted about 5 million vulnerable devices across 150 countries. The ransomware spread through a vulnerability in the Windows SMB protocol and propagated itself across various organizations, including FedEx, Honda, Boeing, Nissan and Renault.
Locky
Locky first emerged in 2016 and was deployed via phishing emails that tricked the user into opening malicious attachments. The attachments contain gibberish and include a phrase like “enable macro if data encoding is incorrect.” If the user enables the macro, executable code embedded within the document installs malware on the system.
SimpleLocker
SimpleLocker was a ransomware designed to infiltrate Android devices through infected applications contained in seemingly harmless software packages. By scanning the user’s SD card, the ransomware could encrypt images, documents and videos. Cyberattackers demanded ransom payments in exchange for the decryption password for those files.
Ransomware Protection Tips
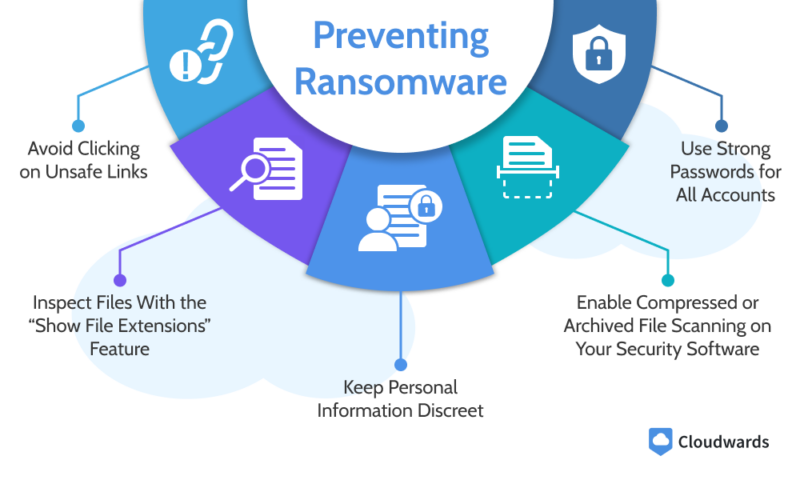
Ransomware attacks may be difficult to solve, but they’re easy to avert by being more security conscious when using the internet. Here’s a list of steps to ensure optimum security.
Avoid Clicking on Unsafe Links
Links contained in unknown websites or spam emails can automatically download malware on your computer if opened. Beware of links from unfamiliar websites. Extra security measures include using antivirus software to scan attachments, using updated software and visiting only secure websites with HTTPS encryption and a padlock icon in the address bar.
Inspect Files With the “Show File Extensions” Feature
Malicious actors often trick users into opening a file containing malicious code by giving it a name such as “cool-cat.avi.exe” to make it look like a harmless file. The Windows-native “show file extensions” feature can protect you from such scams by indicating what types of files are being opened and detecting harmful files.
To enable this feature, you can search for “show file extensions” in the Windows search bar. Click on “show file extensions” in the File Explorer and toggle on the “show file extensions” button.
Keep Personal Information Discreet
Fraudsters have to gain access to your personal information before they can send you personalized phishing emails, which may contain ransomware. While they can get this information through data breaches, they can also scour the social media pages and online accounts of their target.
Keep personal information such as your email address, name, address, phone number and financial records away from public online spaces. You can prevent unauthorized access when you have to send this information over public WiFi by using a VPN — we recommend picking one from our list of the best VPNs.
Enable Compressed or Archived File Scanning on Your Security Software
Malicious actors can bypass spam filters by compressing or archiving malware attached to an email. As a result, an unsuspecting user may open the file thinking it’s harmless. When dealing with compressed or archived email files, configure your security software to scan such files for malware.
Use Strong Passwords for All Accounts
Weak passwords increase the risk of brute force attacks that can give nefarious individuals easy access to your computer files. If criminals guess or steal your credentials, they can deploy malicious code directly into the system. Use strong, unique passwords for all your online accounts to minimize this risk.
Password managers make it easy to generate strong passwords for each account without having to remember them yourself. See our list of the best password managers to get started.
Ransomware Data at a Glance
The tables below provide a rundown of the trends observed by Trellix’s ransomware incident response experts. Median dwell time refers to the amount of time ransomware resides on an infected system before being detected.
Ransomware Attacks: Median Dwell Time (in Days)
| Ransomware (Maximum) | Ransomware (Median) | All Threats (Median) |
|---|---|---|
| 547.49 days | 72.5 days | 56 days |
The median dwell time for ransomware attacks is 72.5 days, compared to 56 days for all threats. Dwell time denotes the period that ransomware remains undetected on a compromised system before the infiltration is caught and mitigated. Lower dwell times indicate that the efficiency of ransomware eradication efforts is improving faster than hackers can counter it.
According to Mandiant, the global median dwell time is on a slump, with the rate of reduction going from over a year in 2011 to just 24 days in 2020. This reduction has been linked to enhanced ransomware detection and response methods, though other watchers point to the diversification of extortion tactics as a negative factor that’s shortening dwell times.
Most Popular Attack Days
| Monday | Thursday | Friday |
|---|---|---|
| Most likely midnight to noon | Most likely midnight to noon | Most likely midnight to noon |
The days in the table represent when the ransomware first activates, not when the cyberattackers initially plant it on the system.
How to Respond to Ransomware Infections
Several steps can be taken to mitigate an active ransomware infection. We’ve gathered nine of them below.
Determine the Scope of the Attack
The first step to curbing ransomware is to determine how far it has spread within the network. With this information, you can take prompt action to quarantine the infected devices and enhance the security of your infrastructure.
Avoid Restarting the Affected Devices
Ransomware perpetrators sometimes program ransomware to damage the device’s operating system or delete the encrypted file when it notices an attempt to restart the device. Also, restarting your device can make it difficult to investigate the attack because vital clues are preserved in the computer’s memory — which can be erased during a restart.
Quarantine the Affected Systems
Malicious actors deploy ransomware as soon as they identify software vulnerabilities within a segment of an infrastructure. This allows the ransomware to propagate itself through the rest of the network. To prevent this, isolate infected systems from the network immediately after you notice the ransomware infection.
Notify All Employees
Cyberattackers can easily send copies of the same phishing email to multiple employees within an organization. Whenever one of your employees falls victim to a malicious email, send a quick notification to warn all other employees about the message. This can prevent a disastrous spread of ransomware within your organization’s system network.
Secure Your Backups
Cybercriminals are aware that organizations often have data backups, and they sometimes locate these backups to encrypt or delete them after the initial ransomware attack. To keep your data backups beyond the reach of cyberattackers, store copies of your data using offline tools secured with passwords.
We also recommend using an online backup service with built-in ransomware protection tools. See our list of the best online backup with ransomware protection for specific suggestions.
Turn Off All Maintenance Tasks
After a ransomware attack occurs, security experts often conduct forensic investigations on the affected systems to determine the origin of the attack. They may inspect network traffic, systems logs, ransom notes and user accounts. Some system maintenance tasks, such as software updates and system reboots, can interfere with these investigations, so it’s best to disable them.
Determine the Ransomware Strain
Identifying the ransomware strain on your system improves your chances of retrieving your files without paying the ransom. You can use an online ransomware strain identification tool, such as Emsisoft Decrypter, ID Ransomware or the No More Ransom Project. You’ll have to upload a ransomware note or a sample of the encrypted data so the tool can detect the strain.
Inform the Authorities
Following a ransomware attack, law enforcement agencies can help you decrypt your files when all your own attempts have failed. The authorities also need to document ransomware attacks to investigate the crime and educate the public about future risks.
Additionally, some regulatory laws such as HIPAA require organizations in certain industries or regions to report data breaches, including ransomware attacks. Check with your organization’s legal department to see what is required for compliance.
Decide Whether to Pay
While most cybersecurity experts do not recommend paying the ransom because it doesn’t guarantee you’ll regain access to your encrypted data, it can be the most reasonable step when dealing with critical data or direct threats to your brand image. Consult with cybersecurity experts and law enforcement agencies before you make a decision.
Final Thoughts
Whether you’re a consumer or business with data on the internet, it’s imperative to understand what ransomware is, how to prevent a ransomware attack and what to do when one occurs. To recap, use an antivirus to scan links or attachments before opening them, safeguard your personal information and use strong passwords for all your online accounts.
If your computer system gets infected with ransomware, inform your employees, identify the ransomware strain, avoid restarting your device and notify the authorities.
We hope you were able to learn more about these tips from our guide. Did you find them helpful? Have you ever experienced a ransomware attack? Let us know in the comments section below, and as always, thanks for reading.
FAQ: What Is Ransomware?
Ransomware is a type of malware that cybercriminals deploy to compel victims to pay a ransom in exchange for access to their data. Using asymmetrical encryption, the criminals encrypt the victim’s data with a public key and generate a private key, which the victim may use to decrypt their data after paying the ransom.
Ransomware is distributed through various channels, but mainly through phishing, malicious advertisements and stolen passwords.
Yes. It can be difficult, but ransomware can be mitigated by taking appropriate measures, such as isolating the affected systems, securing data backups, disabling all maintenance tasks and notifying all employees to prevent further spread of the malware.
WannaCry ransomware is a type of ransomware deployed on Windows computers that encrypts data and demands ransom payments in Bitcoin.
Sources:


