How to Encrypt Your Emails in 2026: Keep Your Correspondence Safe
If you're using a generic email provider, chances are what you send is vulnerable. Follow this guide on how to encrypt email to fix that.
Almost everything you do online is monitored — companies, governments and criminals all want access to your data. Although a good VPN can solve many security concerns, encryption is another great privacy tool. In this article, we’ll go through how to encrypt email, so you can keep your messages private.
Key Takeaways:
- Encryption is the best way to protect a message from spying and data breaches.
- You should use the S/MIME or PGP protocols to encrypt emails.
- Many services have first-party encryption tools.
- Third-party tools like Mailvelope are useful when the service doesn’t support encryption.
Any decent service will have the normal website security measures, such as transport layer security (TLS), which proves the website is legitimate and encrypts the message while it’s in transit. However, though unlikely, it is still possible for a determined criminal or the email service itself to read the data while it’s stored on the servers.
As long as an email service uses a trustworthy encryption protocol — which most secure web browsers and desktop email clients do — you should be safe to use it to protect most of your messages. However, if you’re sending more sensitive information, you should use end-to-end email encryption for the extra protection.
How to Encrypt Email: What You Need to Know
To make encryption as easy as possible, most providers have some tools to help you. Plus, even if it doesn’t come with its own method, you can always use third-party apps. Although you can encrypt most services, the specific email platforms that we’ll be looking at in this article are:
What Is Email Encryption?
Email encryption is simply using encryption to obscure the content of your emails. As emails aren’t exactly the most secure way to send information, they often act as a major attack vector for hacking and fraud. Luckily, most modern email providers will use an SSL/TLS layer to protect the data while it’s in transit, which limits how vulnerable you are to certain attacks — even if you’re on public WiFi.
However, if you’re serious about privacy — for example, if you are sending business emails with sensitive information — you should consider protecting your emails with end-to-end encryption. That way you can hide the content from everyone but your intended recipients.
How Does Email Encryption Work?
Generally, email encryption works by taking the plain text of your email and scrambling it with a string of characters known as a key. You need to have the right key to read the text, otherwise it just appears to be nonsense.
There are two main types of encryption. With symmetric encryption, you can use a private key for both encryption and decryption. With asymmetric encryption, things get a bit more complicated, where you can use both a private key and a public key. Each way has different benefits, and both work well as long as the keys are kept safe.
However, encryption can get quite complex, and the specifics of how it works varies between provider and protocol. If you’re interested, you should read our full guide to email security to find out more.
Why Is Email Encryption Important?
Email encryption is important for protecting your emails from cybercriminals. However, TLS encryption can only protect the data while it’s in transit. Because it’s decrypted when it reaches the email server, there’s potential for a third-party to access your email through a data breach or court subpoena.
This inherent lack of security is one of the most critical aspects of modern email that users must navigate when choosing between traditional and privacy-focused providers.
Although this is incredibly unlikely, some information is too sensitive to take that risk. In this case, you should use end-to-end encryption. This means that your data is obscured even while the email server handles it, so only the intended recipient can read it.
Types of Email Encryption: S/MIME vs PGP/MIME
Although it isn’t necessary to know exactly how your email encryption works, understanding the differences between the most common protocols can be useful. Most email platforms and third-party encryption software will use one of two protocols: S/MIME or PGP/MIME.
Secure/Multipurpose Internet Mail Extensions (S/MIME) is the encryption protocol preferred by businesses with their own mail servers. Alongside encrypting your messages, you can also sign emails with the S/MIME certificate. The recipient can then check this with the certificate authority (CA) that gave them the certificate to make sure the sender is legitimate.
On the other hand, Pretty Good Privacy/Multipurpose Internet Mail Extensions (PGP/MIME — often just called PGP) is more commonly used for encrypting personal emails. As it only uses the recipient’s public and private encryption keys, you won’t need to rely on a CA, but you also can’t use the CA to prove that the sender is legitimate.
In our experience, OpenPGP is the most common form of encryption, but they are both equal in terms of security.
How to Send an Encrypted Email: Gmail, Outlook, iCloud
Gmail, Outlook and iCloud Mail — three of the biggest email services — all provide some kind of email protection. You can use this to keep the contents and attachments of your messages safe, as long as you consider the limitations of each method.
How to Encrypt Email With Gmail
Although Gmail does support TLS, only Google Workspace Enterprise accounts get access to S/MIME encryption. This doesn’t stop you from using a third-party encryption tool like Mailvelope, but there isn’t any official support for personal accounts.
However, Gmail does have a “confidential mode,” which will add an expiry date to the email and give it password protection. This isn’t end-to-end encryption, but you can use it to send protected messages to any email address, and it works on both Android and iOS devices.
- Compose an Email
In your email client or app, go to “compose” to write an email.
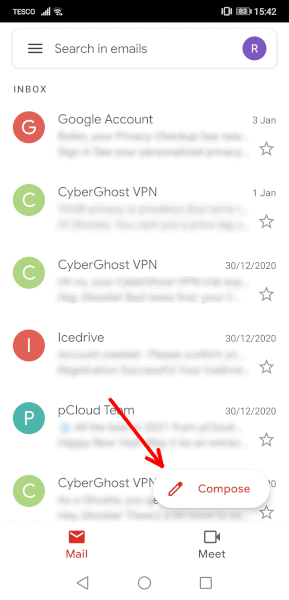 In Gmail, go into the “compose” page.
In Gmail, go into the “compose” page. - Tap the Three Dots
In the email, tap the three dots in the top-right corner.
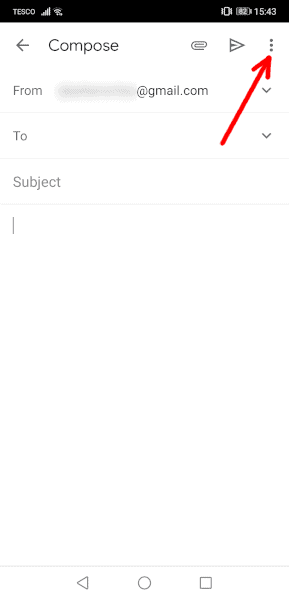 Open the dropdown menu by tapping the three vertical dots.
Open the dropdown menu by tapping the three vertical dots. - Select “Confidential Mode”
In the dropdown menu, select “confidential mode.”
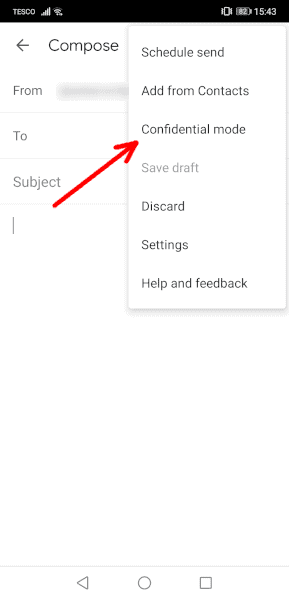 Choose “confidential mode” to add an expiry date and a password.
Choose “confidential mode” to add an expiry date and a password. - Check the Settings and Tap “Save”
Set your expiry date and password settings and tap “save” to set the email as confidential.
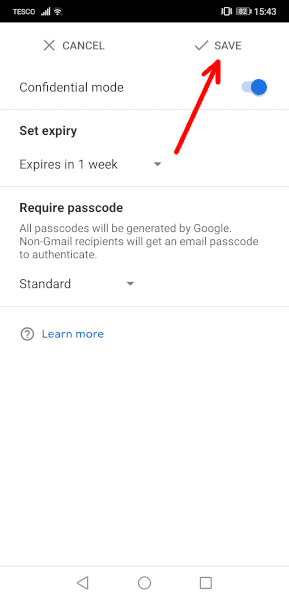 Configure the security settings and press “save.”
Configure the security settings and press “save.”
If you want to use PGP encryption to protect your emails on your personal Gmail account, follow our steps below for using third-party encryption software.
How to Encrypt Email in Outlook
Outlook supports TLS encryption for free, but all paid Microsoft 365 plans — and the free trial — come with the option to use the enhanced Outlook email encryption option using the S/MIME protocol. To begin, you’ll need to have the Outlook desktop app for Windows and a digital ID from a qualified certificate authority, such as IdenTrust or Actalis.
- Open the “Trust Center”
First, you’re going to need to open the “trust center.” You can find this by clicking “file” in the top-left corner and then selecting “options” to bring up the “Outlook options” window.
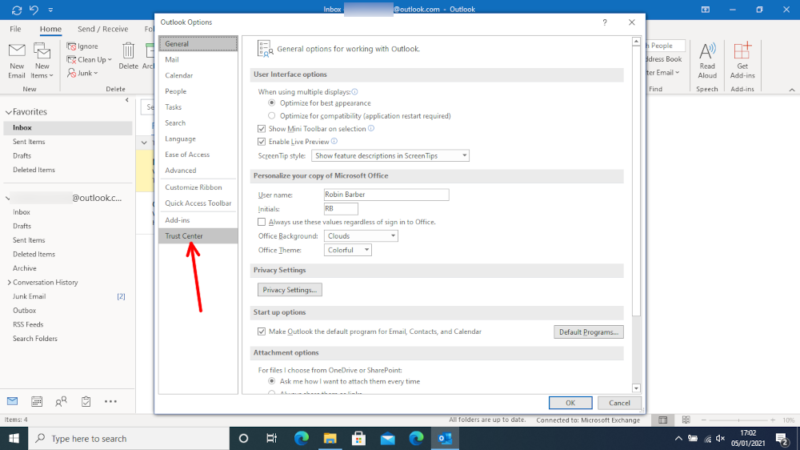 Go through “file” and “options,” then open the “trust center.”
Go through “file” and “options,” then open the “trust center.” - Go Into the “Trust Center Settings”
Click on “trust center settings” to open the trust center window.
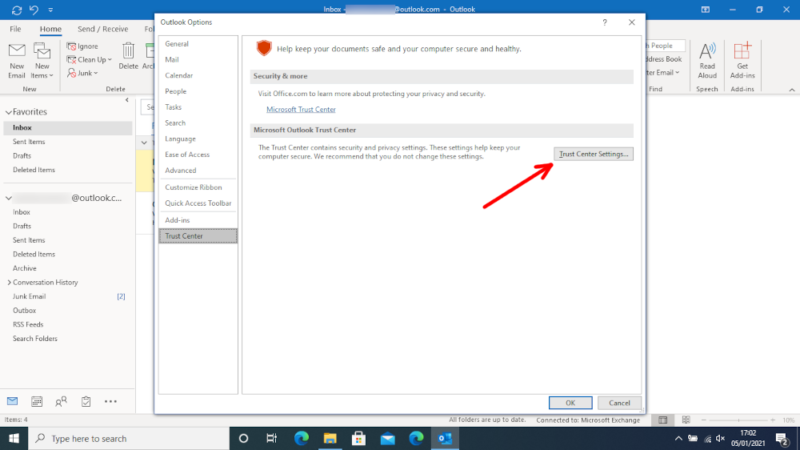 Open the “trust center settings” window.
Open the “trust center settings” window. - Click on the “Email Security” Tab
In the new window, go into the “email security” tab.
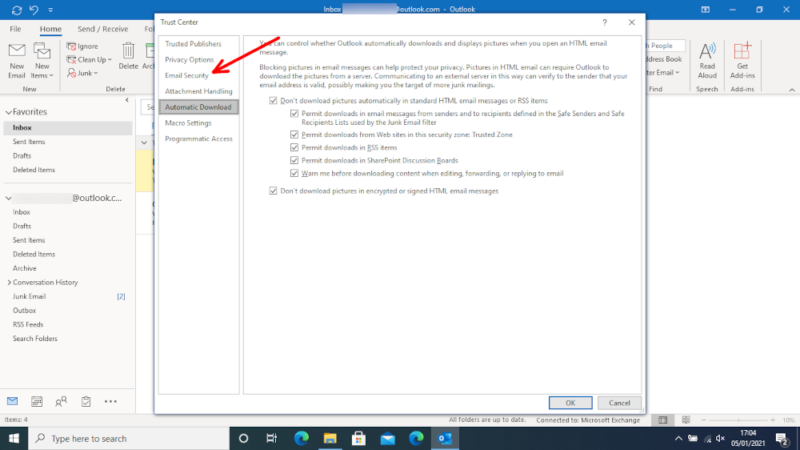 Find the “email security” tab.
Find the “email security” tab. - Import a Digital ID
Choose “import/export” under the “digital ID” section and follow the on-screen instructions to add your certificate.
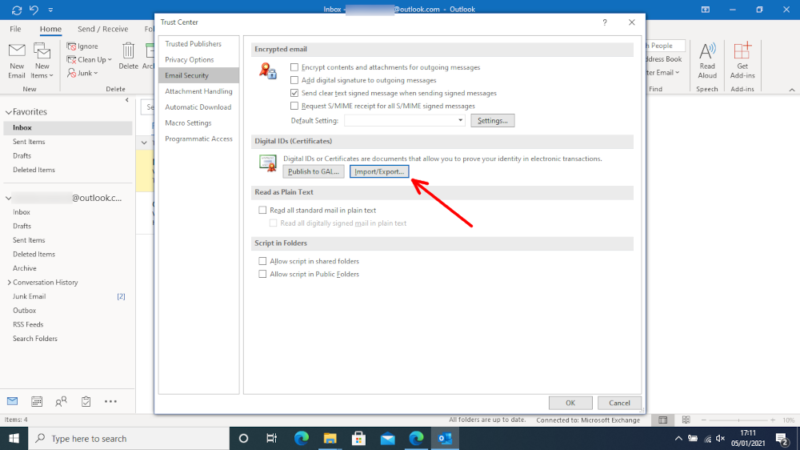 Add your S/MIME certificate to Outlook.
Add your S/MIME certificate to Outlook. - Open the “Settings” Window
Once you’ve imported your certificates, click the “settings” button under the “encrypted email” heading.
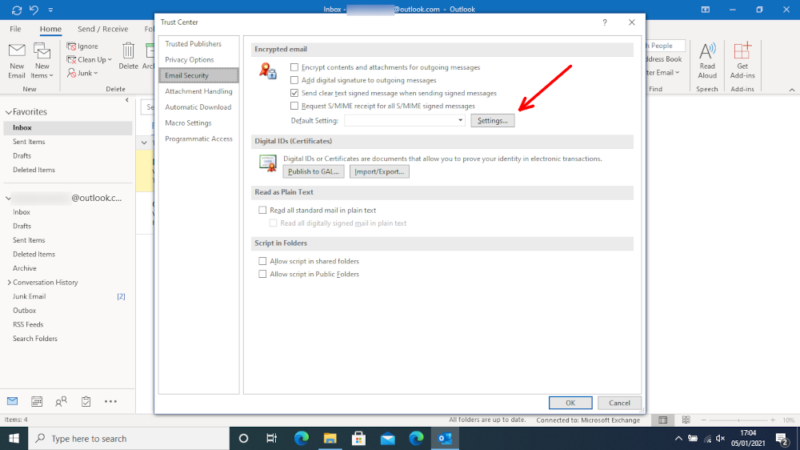 Open the encryption “settings” window.
Open the encryption “settings” window. - Check That It’s Using S/MIME
It should automatically grab your certificate, but it’s best to check that it’s correct before continuing.
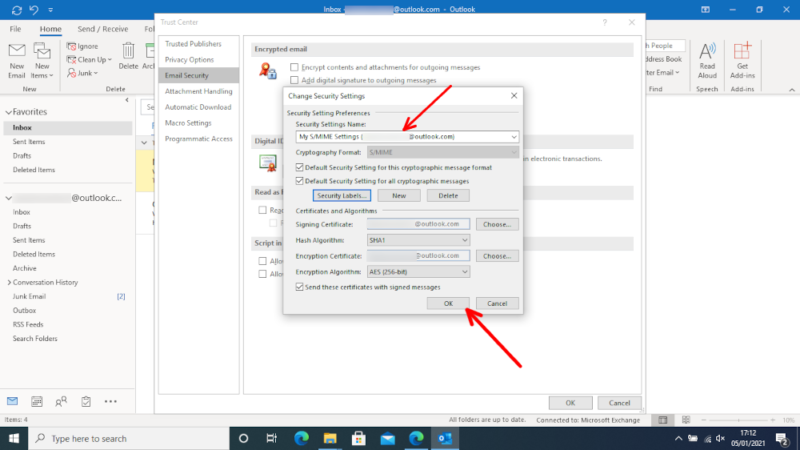 Check that your S/MIME settings are correct.
Check that your S/MIME settings are correct. - Check the Boxes in “Encrypted Email”
Make sure you check all the boxes under the “encrypted email” heading so that your emails are encrypted and digitally signed.
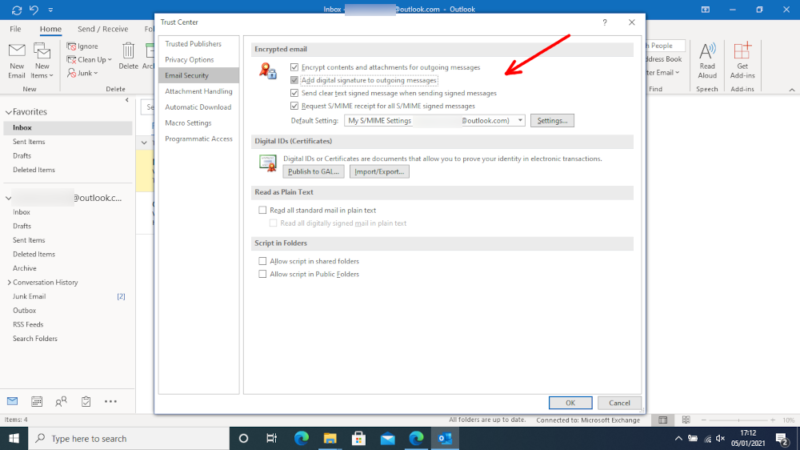 Check the boxes so that Outlook encrypts your emails and adds your digital signature.
Check the boxes so that Outlook encrypts your emails and adds your digital signature. - Check That Your Message Is Encrypted
Now, when you start to compose an email, you can go into “options” and click the “encrypt” button with the lock icon to check that you’re using S/MIME encryption.
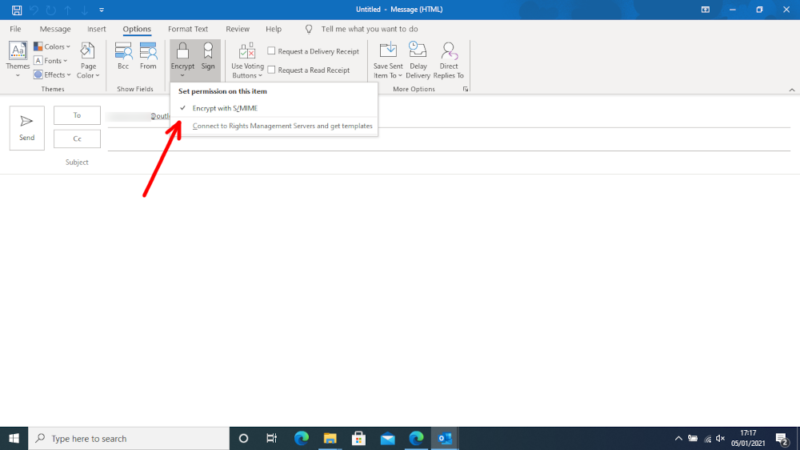 When you go to write a message, look for the lock icon.
When you go to write a message, look for the lock icon.
How to Encrypt Email With iCloud Mail
Part of Apple’s improved security included encryption for iCloud (though not for files), which also lets you send encrypted email messages through the iOS Mail app. Before you begin, you’ll need to install S/MIME certificates or connect your device to a Microsoft Exchange server.
- Go Into Your iCloud Account Through “Settings”
On your iPhone, go into “settings,” find your iCloud account and click “account.”
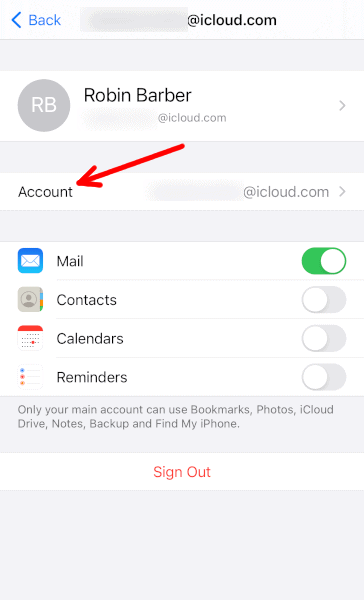 Open the settings for your iCloud account.
Open the settings for your iCloud account. - Select “Mail” for Email Options
In your account settings, find and select “Mail.”
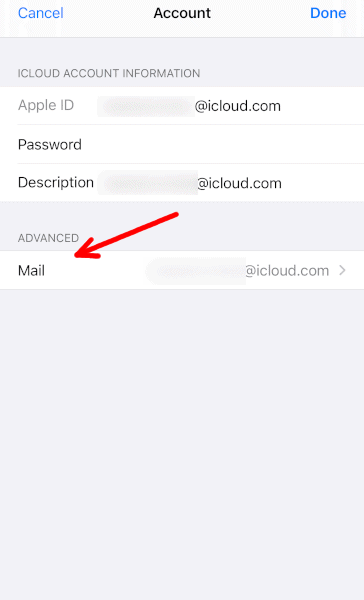 Go into your iCloud Mail settings.
Go into your iCloud Mail settings. - Click on the “Advanced” Settings
The encryption options are in the “advanced” section of the mail settings.
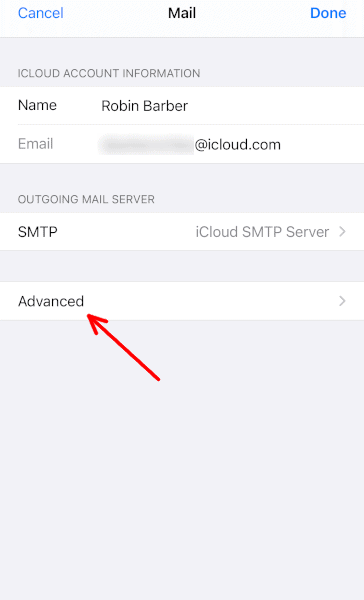 Choose the “advanced” mail settings.
Choose the “advanced” mail settings. - Turn on S/MIME Encryption
At the bottom of the “advanced” settings is a heading labeled “S/MIME.” Turn these settings on.
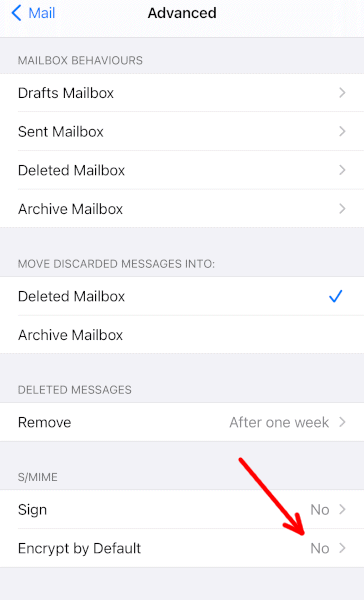 Turn encryption on and check that your S/MIME settings are correct.
Turn encryption on and check that your S/MIME settings are correct. - Check That Your Emails are Encrypted
You should now see a blue lock icon while sending emails. If you see a red lock icon, then you cannot send an encrypted message to that email address — often due to a missing certificate.
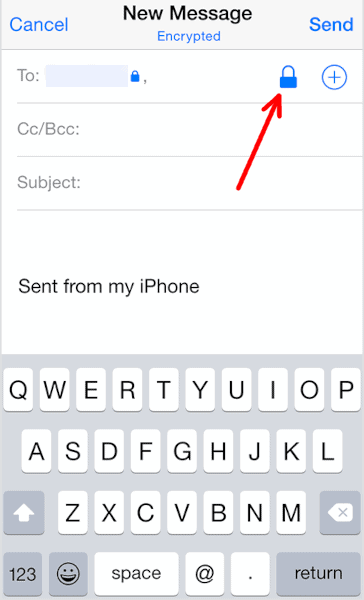 Check that the blue lock icon appears when writing a message.
Check that the blue lock icon appears when writing a message.
Third-Party Email Encryption Software
When it comes to tools that protect your privacy, there are always plenty of options. Mailvelope, GNU Privacy Guard and GPGTools are all free tools that you can use to send and receive encrypted emails within your browser or email client.
That applies even if it doesn’t have any first-party encryption tools, like Yahoo Mail. As we mentioned above, you can also use third-party apps for personal emails in Gmail.
How to Encrypt Yahoo Mail
Many email services — including Yahoo Mail — lack any options for end-to-end encryption. Luckily, Mailvelope supports most web-based email providers, so you can protect any message with PGP encryption.
- Find the Mailvelope Extension
You can find the Mailvelope extension by searching the web stores for Chrome, Firefox or Edge, or you can click the “download Mailvelope” button at Mailvelope.com. Once you’ve found the extension, click “install.”
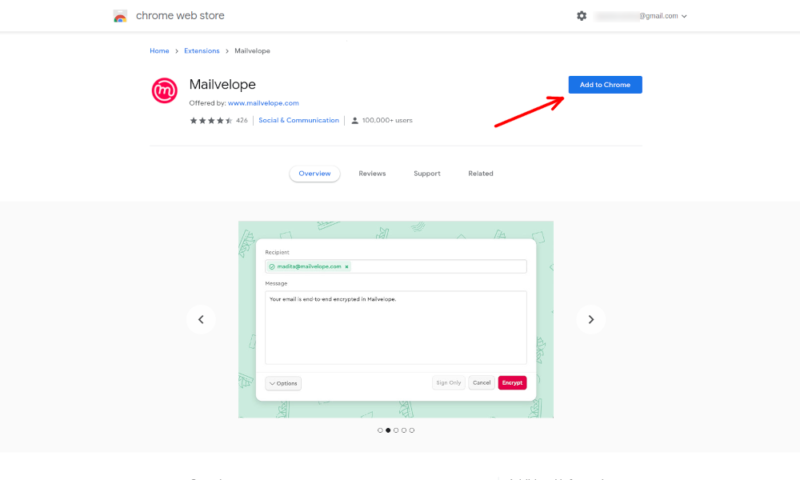 Install the Mailvelope extension from the Chrome web store.
Install the Mailvelope extension from the Chrome web store. - Click “Lets Start”
Once you’ve installed the extension, open it up from its icon in the top-right corner and click “let’s start.”
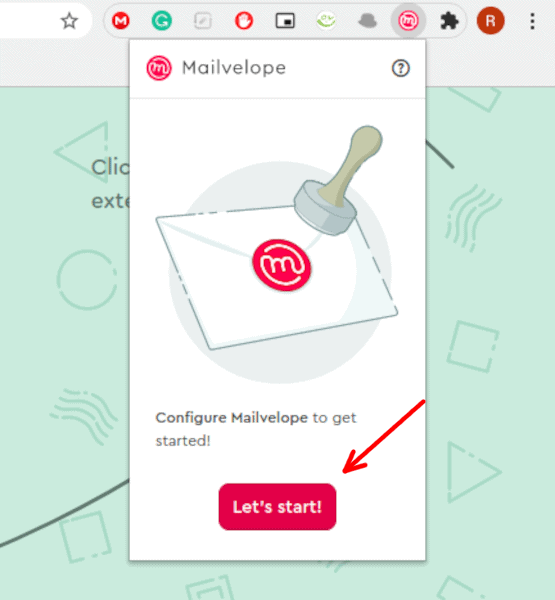 Open the extension and click “let’s start” to begin.
Open the extension and click “let’s start” to begin. - Select “Generate Key” in the Setup Page
On the webpage Mailvelope takes you to, choose “generate key” to create your public and private keys or “import key” if you’ve already made them on another device.
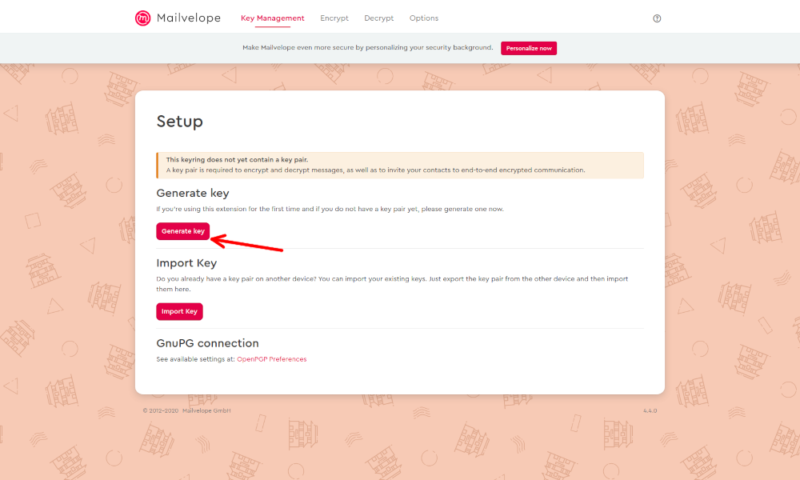 Choose to generate a key with Mailvelope.
Choose to generate a key with Mailvelope. - Generate a Key
To generate a key, enter your full name, email address and password, then click “generate.”
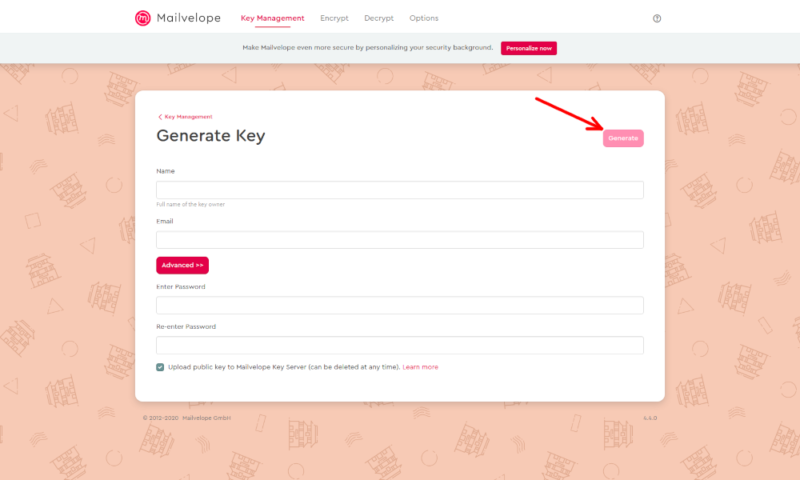 Enter the required information and generate your private and public keys.
Enter the required information and generate your private and public keys. - Select the Mailvelope Icon
When composing an email, click the Mailvelope icon in the top-right corner of the screen.
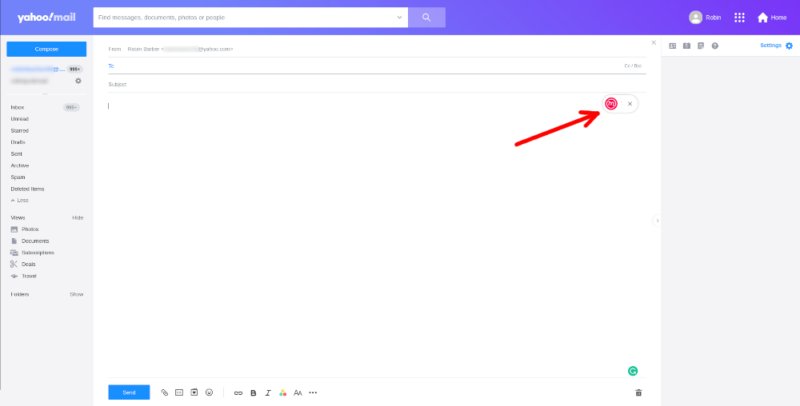 Before you begin writing your email, click the Mailvelope icon.
Before you begin writing your email, click the Mailvelope icon. - Write Your Email with Mailvelope
In the new window that Mailvelope creates, enter your message you want to send and click “encrypt.” You can also choose to add a digital signature without encrypting the message.
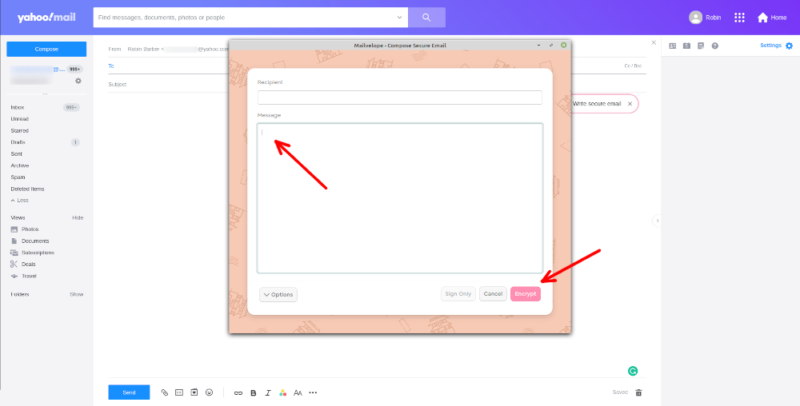 Enter your message into the Mailvelope window.
Enter your message into the Mailvelope window. - The Recipient Enters the Password
To read the email, recipients will have to enter the password you set up earlier.
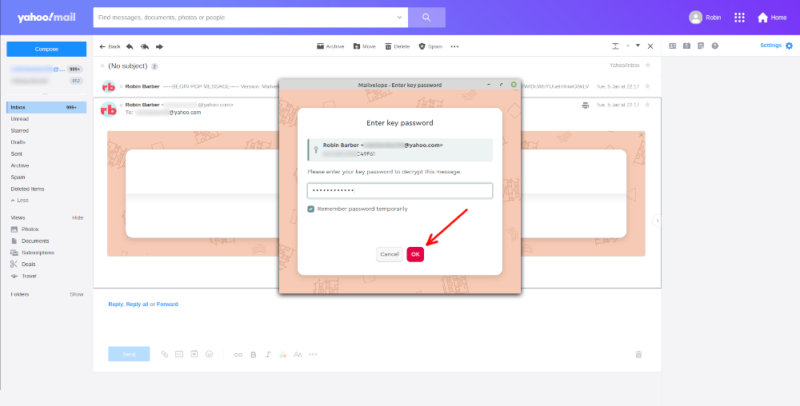 For recipients to read the email, they must first enter the password.
For recipients to read the email, they must first enter the password.
If you select the Mailvelope icon in Gmail in step five, it’ll redirect you to the Mailvelope webpage, and a prompt will appear asking you to sign in with Google. After you sign in you’ll be taken back to Gmail, where you can continue to follow these steps.
Encrypted Email Options
Being able to encrypt your messages with the more well-known email providers is great, but it’s often a lot easier if you just start with a secure email platform. Although these are often harder to use, lack features and have limited free plans, there are a few good options that we can recommend.
Our favorite secure email service is ProtonMail. The free plan isn’t limited too heavily, it’s easy to use and — as an open-source project — you can check out the code to look for security flaws yourself. However, if looking through thousands of lines of code isn’t your thing, you can just read our full ProtonMail review instead.
If you’re willing to give up some ease of use for the best security and privacy, Tutanota may be a better service for you. Overall, Tutanota and ProtonMail are relatively well-matched, so if the unique features and extra email security interest you, check out our full Tutanota review.
Unlike most other secure email services, Mailfence is more of a general-use provider. It comes with some extra communications and planning features, and it allows you to send unencrypted emails. This means that while it isn’t the best for sending encrypted emails, it has extra flexibility to do other tasks. You can learn about these features and more in our full Mailfence review.
Final Thoughts: Email Encryption
Whether you prefer to use web-based services, email clients on your desktop or apps on your Android or iOS device, there are ways to help protect your privacy.
Expiry dates and password protection are fine as extra protection for your emails, but end-to-end email encryption with S/MIME or PGP is the best way to keep your data safe, especially for businesses. Just be sure to keep your private key hidden, as your recipient will only need your public key.
However, if you want to stay safe online, you shouldn’t stop at encryption. You should also use a secure VPN, a strong antivirus and a reliable password manager to keep ISPs off your data, malware off your devices and criminals out of your accounts.
Have you tried to encrypt your emails? Did you use S/MIME or PGP? Let us know your thoughts in the comments section below, and check out our guide on how to encrypt text messages, too. Thanks for reading.
FAQ
Although your options for free encryption software are limited, there are a few services available. You can get a free email account with providers dedicated to security or a third-party extension to send encrypted email messages through a service with no first-party tools.
Unless you’re a business client, the only encryption Gmail uses is TLS. This is good enough for most personal emails, but if you want more protection, you’ll have to use either the “confidential mode” to add a password and expiry date, or a third-party end-to-end encryption program.
Yahoo Mail does use the TLS protocol to encrypt your messages, but this won’t protect anything from a compromised email server, data breaches or any other serious security vulnerabilities. Although these are rare, if you’re dealing with sensitive information, you should use a third-party app to encrypt your messages before you send them.

