What is Torrenting? Everything You Need to Know in 2026
Mostly known as a way to download copyrighted material, torrenting has always been front and center in the internet piracy debate. So what is torrenting, really? Keep reading to learn everything you need to know about the infamous file-sharing protocol.
Chances are that when you think of torrenting, the first thing that comes to mind is pirated content such as music, movies or TV shows. While this is certainly a big use-case for the technology, it’s far from the whole story. So what is torrenting, who is it for, and — perhaps most importantly — how does it work?
Key Takeaways:
- Torrenting refers to downloading files over BitTorrent, which is a decentralized peer-to-peer file-sharing protocol.
- The majority of BitTorrent traffic involves copyright infringement, but there are many legitimate uses and benefits to using the protocol outside of “illegal” content.
- There are some risks to torrenting, but you are extremely unlikely to be criminally prosecuted for it. In order to protect yourself from your ISP or copyright holders, make sure to use a VPN to protect yourself.
In order to answer what torrenting is, we’ll have to flesh out some other concepts as well, as there’s no way to understand what torrenting means on a technical level without first going through a bit of a crash-course on some basic terminology.
If you don’t care about the nitty-gritty technical details, check out our guide on how to start torrenting or our qBittorrent vs uTorrent comparison and best torrent sites instead.
-
12/01/2022 Facts checked
Rewritten to include a more in-depth explanation of BitTorrent and P2P, as well as instructions for how to begin downloading torrents.
What Is Torrenting and How Does Torrenting Work?
Torrenting is a unique method of sharing files that relies on peer-to-peer networks. In this section, we will explain the basics of torrenting and the terms you need to know to understand how it works.
What Does Torrenting Mean?
Torrenting refers to the process of downloading files using BitTorrent, which is a decentralized peer-to-peer file sharing protocol. In order to understand what torrenting is, and particularly how it works, it’s necessary to have a working definition of peer-to-peer (or P2P for short) file-sharing.
What Is Peer-to-Peer (P2P) File-Sharing?
Peer-to-peer networks operate in a decentralized way, meaning that instead of connecting to a single centralized server, users form an interconnected web of “peers.” Depending on what the network is used for, tasks or data are spread across the peers, with each one acting as both a consumer and a supplier.
A good way to understand the concept of a peer-to-peer network is to contrast it with the traditional server-client model. With a server-client model, the user (aka the client) acts only as a consumer, connecting to a single or limited number of servers that supply resources or files.
Although BitTorrent is by far the most famous P2P protocol, it’s far from the only one out there. In fact, early versions of the internet were inherently designed as peer-to-peer systems, with concepts like firewalls only emerging in the late 1980s.
Only in the mid 1990s, with the commercialization of the internet, do we see the shift to the server-client model that’s so prevalent today.
Early file-sharing networks like Napster were also based on peer-to-peer networks, but with significant differences to the now dominant BitTorrent. Using Napster as an example, users would make folders directly available to the network, with any downloader connecting directly to the source and downloading it in its entirety from there.
What Is the BitTorrent Protocol?
Today, BitTorrent dominates the P2P landscape. This is largely due to some key innovations of the protocol, namely swarms and trackers.
What Are Swarms, Peers, Seeders and Leechers?
Instead of directly downloading the entirety of a file from a single source within the network, BitTorrent breaks the file into multiple little pieces and spreads the pieces out to “peers.” Every peer who has a piece of the file on their device is a member of the “swarm.”
Each swarm member simultaneously uploads and downloads pieces of the file, effectively exchanging them with one another. Once a peer has acquired the entirety of the file, they stop being a consumer and become known as a “seeder.”
A torrent that has no seeders (meaning no one with the entirety of the file) in its swarm is generally considered dead. It’s still possible (but not guaranteed) that the remaining peers can reconstruct the file, but only if they have all the pieces of it shared between them.
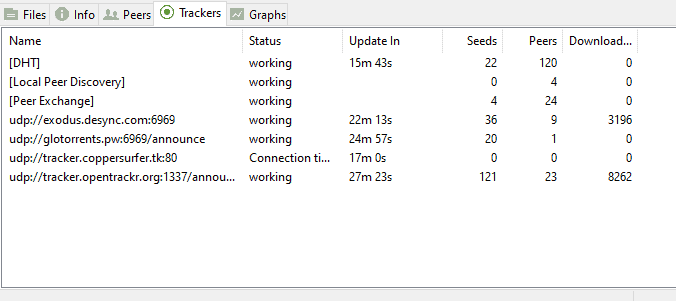
What Are Trackers?
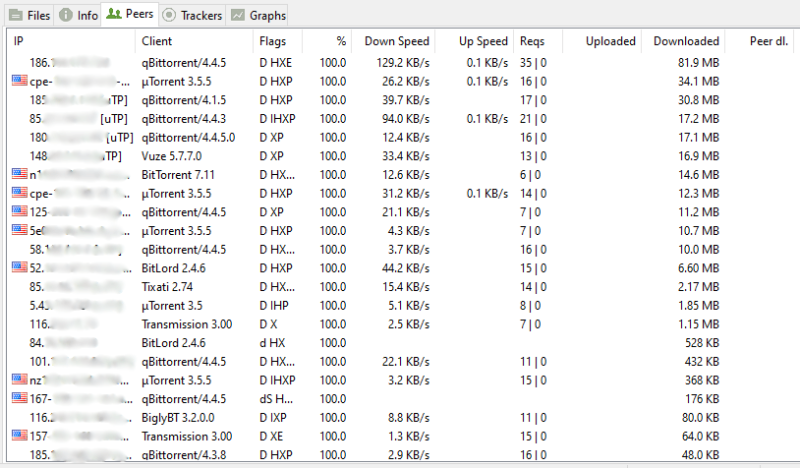
You can think of trackers as the phone-books of BitTorrent. When a peer downloads a torrent file (or accesses a magnet link, more on this later), part of that file is the URL needed to connect to the tracker (or multiple trackers). A torrent client then takes that URL and sends a message to the tracker, which provides a list of other peers.
Once two peers are connected, they will use the remaining content in the torrent file (namely a hash that represents the file contents) to identify and exchange the pieces of the file that they are missing. This is significant, as it means the information detailing the actual contents of the files is not located within the tracker, but rather within the torrent file itself.
The first time a peer connects to another peer, it receives a piece of the file “free of charge,” since it doesn’t have any pieces of the file to exchange. This will usually be the rarest piece of the file.
Once a peer has acquired multiple pieces of a file, they can maintain multiple transfer sessions simultaneously, exchanging pieces with multiple other peers at the same time. This is why most torrents start downloading at low speeds, but get faster as more pieces are acquired.
What Are Torrent Files & Magnet Links?
Now that we have a basic understanding of what’s happening under the hood, it’s time to look at what the actual user sees.
As we mentioned earlier, all the information you need to access the shared data is located within a torrent file. These are created by the original distributor of the data, who then becomes the original seeder when they upload the file to a hosting site such as The Pirate Bay.
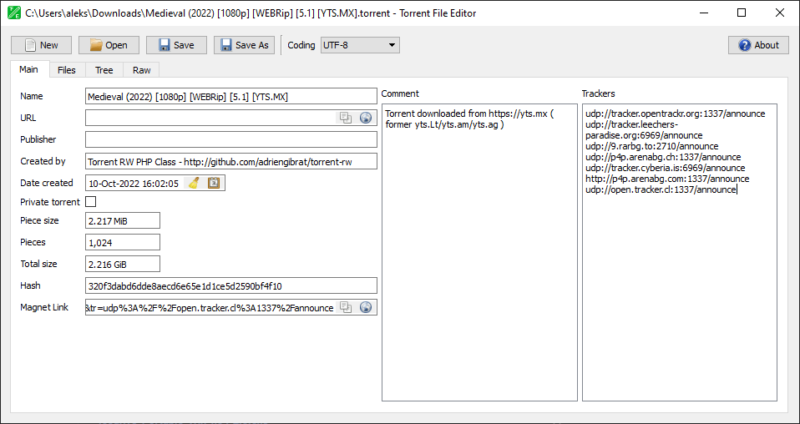
To make things a bit more complicated, torrent files have largely been replaced with a new format called “magnet links.”
Magnet links contain the same information that torrent files do, namely the tracker URL, hashes of the file pieces and the number of pieces. However, instead of being delivered in a file that your torrent client has to open, magnet links open the torrent client and deliver the information directly, much like how regular web links and web browsers function.
Private Trackers vs Public Trackers
As we covered earlier, a torrent tracker is the place where your torrent client goes in order to find a list of peers for any given torrent. These trackers come in two broad categories: private and public.

Public trackers are available on torrenting websites like The Pirate Bay or eztv, and have no restrictions or requirements for becoming a peer and downloading the content.
Private trackers, on the other hand, usually require a login to access, and often necessitate users to spend a certain amount of time seeding files. They do this in order to maintain a certain ratio of uploads to downloads.
Because of this, private trackers are generally faster, since they’re less impacted by people who are intentionally uploading less than they’re downloading (which is known as a “leecher”).
What Are BitTorrent Clients?
You’ve gotten your hands on a torrent file or magnet link, but now what? In order to read the information stored there, as well as actually carry out the download, you need to use a torrent client.
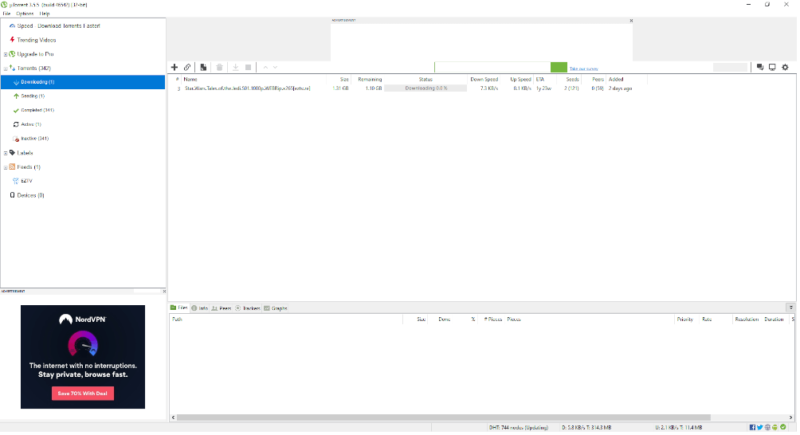
The torrent client serves as the final link in the chain, as it does the actual heavy lifting of connecting to the tracker using the torrent file or magnet link, and handles the exchanges of pieces with other torrent users. This is also where you have the most control and options as a user, as there’s plenty of great torrent clients, such as qBitTorrent, Deluge and uTorrent.
What Are the Benefits of BitTorrent and P2P File-Sharing?
As we touched on at the beginning of the article, BitTorrent has gained something of an unfair reputation in the general public’s eye. While it’s true that the vast majority of BitTorrent traffic involves some form of copyrighted content, the remaining traffic — though only a small percentage — represents the legitimate benefits to distributing data using BitTorrent.
Since BitTorrent (and P2P file-sharing in general) relies on a large network of individual peers all handling a small part of the traffic, it can be an incredibly cost-efficient way to distribute files to a large number of people.
With the server-client model, the cost of distribution involves up-front costs and quickly sky-rockets as the number of users increases. With the peer-to-peer model (and especially BitTorrent), the opposite is true. The more users downloading your file, the faster the download is for everyone, and setup and maintenance costs are virtually non-existent.
Even large companies sometimes make use of BitTorrent when distributing large amounts of data to a huge number of customers. For example, online games like MMORPGS (for example World of Warcraft) often utilize the protocol in their downloaders to lessen server-load and costs.
What Are the Risks of Torrenting?
While there are plenty of completely legal torrents, if you’re torrenting copyrighted material, you are most likely breaking the law by engaging in copyright infringement. That said, the intensity and frequency of enforcement will vary significantly depending on where you live, and there can be other consequences outside of criminal prosecution.
In terms of criminal prosecution, this has so far been limited to major distributors and website hosts, such as the founders of the infamous Pirate Bay. We looked, and we couldn’t find a single example of someone going to jail or being prosecuted by the state for simply downloading torrented files.
That said, in certain jurisdictions, particularly in the U.S., there is a possibility of direct legal action by the copyright holder. This is by no means common, as there are generally less than 5,000 copyright infringement lawsuits filed yearly across the entire U.S., and the vast majority of these are unrelated to torrenting.
Internet Service Provider Woes
A far more common consequence of torrenting is that you’ll annoy your Internet Service Provider (ISP for short). ISPs don’t necessarily care that you’re committing copyright infringement — it’s the copyright holders who care — but your ISP does care that you’re taking up a far greater portion of your bandwidth when you’re torrenting compared to most other internet traffic.
For this reason, internet service providers will sometimes send emails to customers that they suspect (or know) are torrenting and downloading copyrighted material.
This can even extend to your network being throttled, either in general or specifically for P2P traffic. However, if you use one of the best VPN services for torrenting, your ISP won’t have any idea what you’re doing, and so can’t throttle your network or tattle to the copyright holder.
Torrenting Security
Another potential risk of torrenting is downloading fraudulent or malicious files containing some kind of malware.
The best defense against this is to use well-established torrent sites and trackers, most of which include some sort of rating or reputation system. These let you pick torrent files that have been verified by other users or come from people with proven track records.
However, sometimes there are no good options, and the only torrent you can find comes from a suspicious source. In these cases, we’d first recommend reconsidering, but if you’re determined to proceed, at least install any of the best antivirus software to scan the contents of the torrent file itself and the final product before you open anything.
Finally, the last potential security risk that you might face downloading torrent files is the other users. Whenever you download files over BitTorrent, you’ll be able to see the IP addresses of all the peers you’re connected to, and they can see yours. Although you’re unlikely to get doxxed by a random torrent user, it’s still a risk, and one that’s easy to avoid by using a VPN.
How Do I Download Torrents?
Downloading torrents is a surprisingly simple process, but it requires a small amount of set up before you can get started. First, you’ll need to install a torrent client, and then find a torrent site that hosts the type of torrents that you want to download. With a bit of extra work, you can even automate your torrent downloads.
Before you start downloading torrents, make sure you check out our guides on how to torrent with a VPN to avoid many of the potential consequences torrenting poses.
Furthermore, make sure that you’re using a reputable and popular torrent client, such as qBitTorrent, uTorrent or Deluge (among others), and that you only download torrents or use magnet links from legit sites with ratings and reputation scores.
How Do I Stream Torrents?
If you don’t like the idea of filling up your computer with large video files, you can instead choose to stream those torrents through services like Stremio (with the Torrentio addon installed). Besides saving space on your device, this approach also spares you from having to wait for the download to finish before you can start watching.
Final Thoughts: Torrenting Meaning
With the rise of easily accessible streaming services, torrenting has faded from the public consciousness somewhat, and you might even have wondered “are torrents still a thing?” Hopefully this article has shown you that torrenting is alive and well, and given you a more thorough understanding of what the technology is and how it’s used.
If you’d like to enhance your security while downloading torrents, we’ve created a guide on I2P vs Tor.
What do you think of our explanation of what torrenting is and how it works? Do you use torrents yourself and is torrenting still a thing in your social circle, or do you prefer the ease of use and access that comes with official streaming platforms? If you’re a torrent user, do you use a VPN to protect yourself? Let us know in the comments below and, as always, thank you for reading.
FAQ
Torrenting can be used to download and distribute any type of file. This includes copyrighted material such as music, movies and TV shows, but also free or public content, and content from companies looking to reduce server costs.
Torrenting means downloading files over a peer-to-peer communication protocol known as BitTorrent. Torrenting is not inherently illegal, as you can use it to distribute and download content that’s free or not protected by copyright. Learn more in our ‘is torrenting illegal‘ guide.
The most likely scenario is that your ISP is the one that notices that you’re torrenting copyrighted material. In most cases, this will result in a stern warning by email telling you to stop, and getting caught repeatedly may result in your connection being throttled. In extreme cases, your ISP might notify the copyright holder(s), who can in turn choose to sue in civil court.
We’re not lawyers, but it’s extremely unlikely — bordering on unheard of — to go to jail simply for downloading torrents. With the exception of major server hosts and distributors, as far as we could find, there are no examples of people going to jail for activities related to torrenting.


