What is Phishing? More Than Just Your Spam Folder
Cybercrime is an evolving problem. Even as consumers learn about online scams and schemes that run amok in the dark corners of the internet, new ones are being developed.
One such crime is phishing. In this guide, we’re going to cover what phishing is, the different types to look for and the steps you can take to protect yourself. Like learning the unsafe streets in a major city, the ability to identify cybercrime takes time.
Thankfully, there are tools to guide your path along the way. We’re going to start by showing you the telltale signs of phishing, so you know what to look for. That won’t always keep you safe, though. Even after learning the unsafe streets, you’ll want to carry Mace, and, even after learning the signs of phishing, you’ll want a secondary form of protection.
What Is Phishing? More Than Just Your Spam Folder

Phishing is a cybercrime that attempts to steal sensitive user data with bait. An attacker phishes for anyone that can fall for the bait, just as you’d attach a worm to the end of a fishing hook.
The majority of phishing schemes live in your email inbox as random emails asking you to verify your identity or fork over credentials. There are other phishing scams, though. Attackers phish through voice calls, text messages and social media, as well.
In most cases, phishing asks you to click on a malicious URL that looks like a legitimate login. Institutions impersonated are typically banks, credit card agencies and PayPal. Instead of sending your data to one of those companies, though, you send it to the attacker.
Some scams pull double duty, stealing your login credentials and installing malware on your machine. Since baiting a user into accepting a malicious scheme is the definition of “phishing,” that would still fit under the umbrella term.
Phishing is rampant, which makes it dangerous. Mock websites are indistinguishable from real ones and hackers are finding ways to get past increasingly sophisticated spam filters. Before we talk about how to protect yourself, though, let’s look at the kinds of phishing happening today.
Types of Phishing

There are many different types of phishing. Since the term is so broad, there’s crosstalk between it and other areas of cybercrime. We’re going to cover the major methods of phishing you’re likely to encounter, whether at home or work.
Bulk (Deceptive) Phishing
Large-scale phishing is the most common scheme you’ll see. It goes by a few names, but we’re calling it “bulk” phishing for this guide. As the name implies, bulk phishing casts the widest net possible to get data from any poor soul that falls for it.
If you’ve looked in your spam folder, you’ve seen an example of bulk phishing. Attackers gain access to email lists traditionally used by marketers to send out phony emails, usually posing as a credit card agency.
There are ridiculous examples, such as an African prince who thinks you should inherit his fortune (we’re speaking from experience on this one), but you need to look out for the crafty emails that make it past your client’s spam filter.
One often-used scheme features PayPal. You’ll receive an email stating that something is either wrong or needs to be verified on your account and, of course, you’ll need to login to fix it. Clicking on the link in the email redirects you to a PayPal lookalike that collects your credentials.
More sophisticated redirects will take you to a phony PayPal login, then redirect you to the real PayPal as if nothing happened. In that case, it’s easy to assume nothing is out of order while an attacker makes do with your personal information.
Thankfully, it’s easy to protect yourself against bulk phishing. The first step is to disregard what’s in your spam folder, especially if an email asks for personal information. Even if you’re expecting an email and your client accidentally flags it, it’s best to ask whoever sent it to send another.
For emails that make it past your spam filter, vigilance should prevail. Before entering personal information, double check your address bar to ensure that the website you’re on is what you expect and not a redirect. If you get a notice from PayPal, for example, you can resolve that issue by logging in to your account in a separate window instead of using the link.
Double check the email address that sent the message, too. Attackers will sometimes replace an “o” with a “0,” for instance. Your email client’s spam filter should catch this, but it’s good to make sure.
A recent example from phishtank.com is “http://pypalsecutirysummary.com/”
You don’t need to go through this process for all your emails. Just make sure that you do your due diligence before you click a link or enter personal information. As long as you do so, you shouldn’t be caught in a bulk phishing scheme.
Spear Phishing
Spear phishing is bulk phishing with a personal touch. The sender will use available information to appear legitimate. The most common disguise in this category is a bank, where the attack can send your name, address and more.
The same rules as bulk phishing apply. Make sure you’re vigilant against spelling errors, bogus emails and strange redirects. In practice, it’s more difficult than it seems to take the extra step, especially when an email is using your personal data, but it’s paramount.
Individuals are unlikely to be the main target of spear phishing, unless you have a particularly enticing set of credentials. In many cases, spear phishing targets businesses, either to gain access to business assets or personal ones.
In 2016, more than 1,800 Google accounts were compromised as part of a spear phishing attack carried out by TG-4127. The group got emails linked to the Hillary Clinton presidential campaign and used them as a basis for attack.
TG-4127 exploited the Gmail login which the Hillary for America team was using. Attackers sent an email requesting that users update their account information with a bitly link. The link redirected to a URL that started with “accoounts.google.com.” That isn’t a typo, but the attackers would like if you thought so.
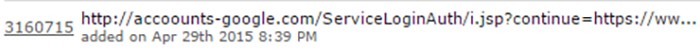
When a worker clicked on the bitly link, their email address was sent to TG-4127’s spoof page, automatically filling in the top field. If the connection was successful, the other half of the equation, the password, was sent once the worker entered it.
Whaling (Executive Phishing)
Whaling is spear phishing targeted at the C-suite. Usually, the attackers look for the highest positions in a company, especially those who may not participate in phishing exercises, and use a bait email to steal their login credentials.
Executives also have the most information available about them online. Attackers can easily gather personal data to craft an email that looks like it comes from a credit card or insurance agency, for example.
Once the login data has been skimmed, it’s used to wire business funds to the attacker.
Whaling is exclusively targeted at high-ranking business executives. Attackers can use smaller spear phishing campaigns to infiltrate the company on the ground floor and work their way up.
Clone Phishing
Clone phishing takes an email that has previously been delivered and copies its content, replacing any legitimate links with malicious ones. The email is then sent to recipients of the original email using a spoofed account. Basically, the attacker clones a legitimate email.
Clone phishing can only happen if the attacker has access to the account that’s sending the email. Attackers will infect a computer with malware that they then move from one machine to another by using an email address that appears legitimate.
The goal of most clone phishing is to infect the destination computers with a virus, malware that spreads to a branching network of machines. As the links go out, more users are infected, who then send out more infected links.
In the end, the computers are used as part of a botnet or to harvest data from sources, such as a webcam, for exploitation (read our guide on how to secure your webcam).
Pharming
Pharming is a new-ish form of phishing. Instead of using bait to lure in a victim, the attacker abuses the destination that a user is trying to go to. Attackers use DNS cache poisoning to redirect users trying to access a legitimate website to a malicious one.
Whenever you type in a URL, your request is sent to a DNS server which translates the alphabetical URL into an IP address. The request is sent to the server corresponding with that IP address and your content is fetched.
Pharming preys on this system. A new IP address, one that directs to a malicious website, is introduced into the DNS cache. For phishing, the site you intended to go to and the malicious one should look identical.
Hackers use this attack, also known as DNS spoofing, for distribution of malware, too. Due diligence may not be enough to protect you from pharming, as the attack doesn’t rely on you clicking on a sketchy link. Even as a vigilant internet user, you could fall victim with your intuition alone.
How to Protect Against Phishing
In many cases, common sense will protect against phishing. Unfortunately, the ones running the scam are adapting to a learning audience. New schemes, such as pharming, are scary, especially with how close a website or URL can look to the original.
You’ll need to use the most secure antivirus software that has phishing protection in real-time to fully protect yourself. Instead of guarding against a malicious email, the antivirus will look at the destination and warn you if there are issues.
Bitdefender Total Security, for example, includes protections for fraud, phishing and theft. It will scan websites you visit automatically and display a warning if you land on a malicious one. Phishing protection is just one of the reasons Bitdefender is our top pick for the best antivirus software, as you can read in our Bitdefender review.
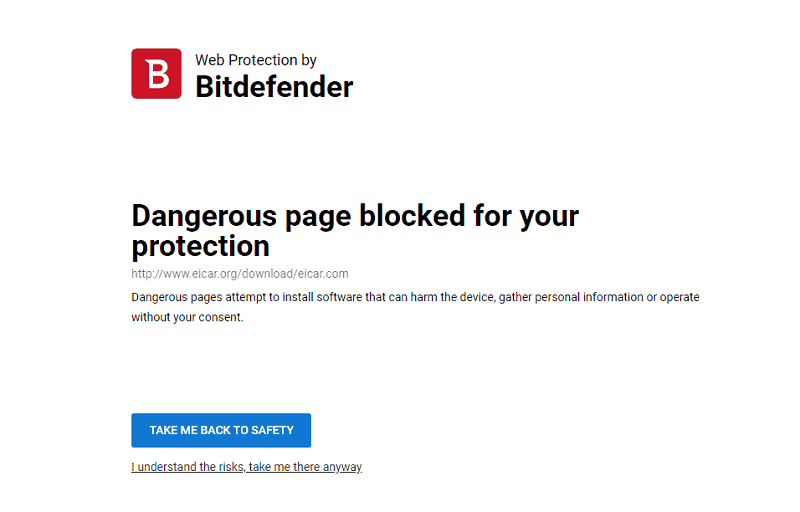
Protection for the URL adds security. Pharming scams that redirect a legitimate request won’t be an issue for Bitdefender, or any other antivirus with phishing protection, to handle.
Phishing protection isn’t as common as ransomware protection among antivirus software (see our ransomware statistics piece for reasons of why you’d need that, though). There are options besides Bitdefender, though. Webroot, for instance, has some of the best phishing protection in the industry, which you can find out more about in our Webroot SecureAnywhere review.
AVG also provides phishing protection. It monitors your browser and email, so there are two layers of analysis. You can learn more about it and why we think it’s the best free offering on the market in our AVG review.
Incogni can also help protect you against phishing. It sends data removal requests to over 420 major data brokers and checks up with the company to ensure everything has been deleted. Criminals can use your data profile to send convincing emails. Incogni makes it harder to build a profile of your data, which means their emails will be less likely to trick you.
Real-time phishing protection and common sense will get you past most schemes. There are thousands of new phishing URLs pouring into the internet every day, though, so you should routinely check who is receiving your personal information before entering it.
Businesses are a prime target for phishing attacks, with employees, common sense won’t always work. Because of that, it’s a good idea to run phishing tests through employee emails and use a strong antivirus.
Final Thoughts
Phishing is so common that most people familiar with it assume they have it covered. Hackers are crafty devils, though, and new schemes, such as pharming and typosquatting, make the future of this cybercrime look dangerous.
A strong antivirus will protect you against existing or developing phishing schemes. Bitdefender is our first pick, but you can find other options by reading our antivirus reviews. Have you run across any phishing scams? Let us know what you did to protect yourself in the comments below.
As always, thanks for reading.


