Hola VPN Review: Is My Connection Secure in 2026?
In trying to establish a peer-to-peer VPN, Hola has built a worse version of a conventional service while infringing on user privacy in the process. Read our investigative Hola VPN review to learn why you should steer clear of this VPN.
Hola is a dangerous virtual private network that asks you to trade away your privacy in exchange for a lackluster service. We found weak encryption and almost no features while testing Hola VPN for this review. Do yourself a favor and check our list of the best VPNs for alternatives. If Hola’s free version entices you, our best free VPN article lists better options.
When you first arrive at the Hola VPN website, it looks like any other virtual private network. You’ll find grand claims about freeing the internet, boasts about speed, and promises that you can use it absolutely free. In truth, Hola is a failed experiment at best and an active privacy threat at worst. Our in-depth Hola VPN review will take you to the bottom of the rabbit hole.
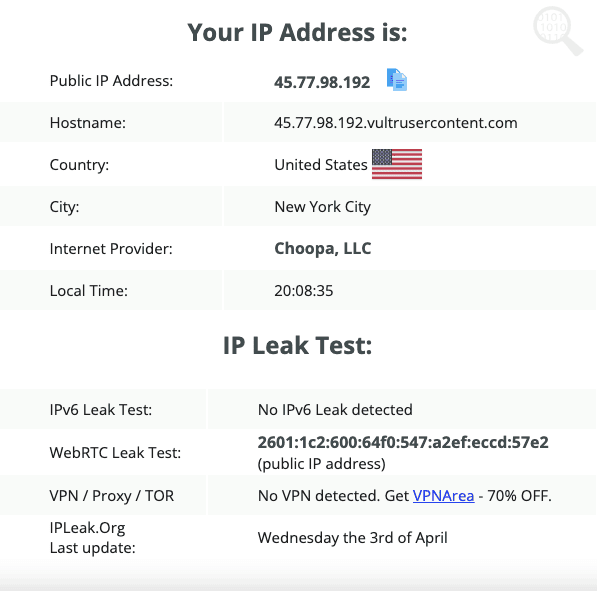
By using Hola’s free plan on Windows or macOS, you agree to donate your IP address to its network. Any other user, free or paid, can browse the internet using your identity as a mask. That leaves you open to prosecution for someone else’s actions, and it may also let other Hola users execute malware on your computer.
To top it off, other users aren’t the only ones who get access to your IP address. Your IP address also gets lended out to Bright Data, a subsidiary company of Hola. Bright Data sells residential IP addresses to companies that use them for market research. Investigations suggest that clients’ actions on Bright Data proxies are not meaningfully policed. Keep reading for the full details we’ve uncovered about Hola VPN.
Protect Your Privacy. Get Our Free VPN Guide Now!
- Comprehend the essential role a VPN plays in safeguarding your digital life
- Gain a deep understanding of how VPNs function under the hood
- Develop the ability to distinguish fact from fiction in VPN promotions
-
05/07/2024 Facts checked
We’ve rewritten this article with a more thorough review that addresses concerns with Hola’s service.
What Is Hola VPN & Who Is It For?
Hola is a peer-to-peer VPN, where every IP you’re using belongs to another user on the network. Most VPNs sell you access to a private network of servers you can use to change your IP address, but not Hola. It has a server network, but it’s not clear how much traffic it actually receives. Most of its IPs come from a different source: other users.
If you know anything about security, you’re probably already worried. If a stranger can use your IP address, what’s to stop them from committing crimes and pinning them on you? Hola claims there’s no risk, because user IPs can access sites only on an allowed list. Even if that’s true, the determination of which sites are safe is entirely up to the Hola team.
Whoever controls the allowlist could accidentally let slip a domain associated with drugs or illegal pornography, or fail to allow a perfectly innocuous site that you need. Even worse, the allowlist can’t police what people do on legitimate sites. What if another Hola user posts hate speech on Facebook or emails a death threat to a politician using your IP address?
Hola’s alleged purpose is to help users change their IP addresses so they can access websites in other countries. However, it operates a subsidiary company called Bright Data (formerly Luminati) that sells corporations access to your IP address. It’s not a stretch to say these clients are Hola’s real target audience.
Hola VPN Pros & Cons
Pros:
- Free version with full network
- Unblock streaming services
- Often quite fast
Cons:
- Very few features
- Sells your computer as a bot
- Unaddressed malware exploits
- Lets strangers use your IP address
- Browser extension constantly disconnects
Hola VPN Alternatives
- 1
- : PayPal, Credit card, Google Pay, JCB, UnionPay, Bitcoin, Ethereum, X-Coin
- : 10
- :
- :
- :
- :
Average speedDownload Speed288 MbpsUpload Speed48 MbpsLatency7 ms - 2
- : PayPal, Credit card, Google Pay, Amazon Pay
- : Unlimited
- :
- :
- :
- :
- 3
- : PayPal, Credit card, Bitcoin, UnionPay, iDeal, Sofort, Giropay, Pixpay, Sepa Direct Debit
- : 14
- :
- :
- :
- :
Average speedDownload Speed244 MbpsUpload Speed41 MbpsLatency6 ms - 4
- : PayPal, Credit card, bitcoin, Amazon Pay
- : 7
- :
- :
- :
- :
Average speed - 5
- : PayPal, Credit card
- : 10
- :
- :
- :
- :
Features: What Can Hola VPN Do? (50/100)
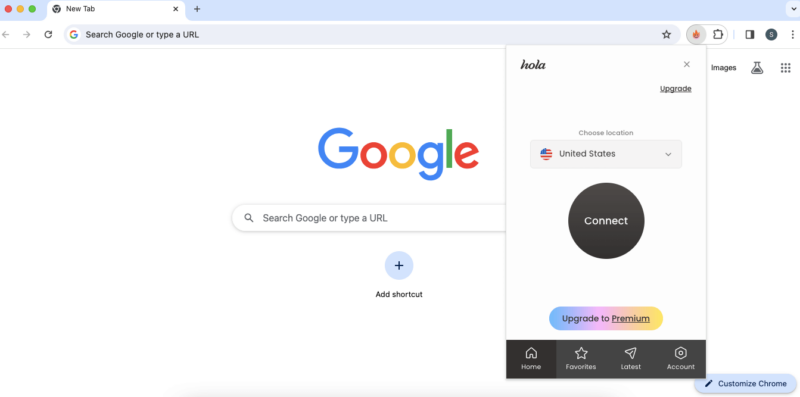
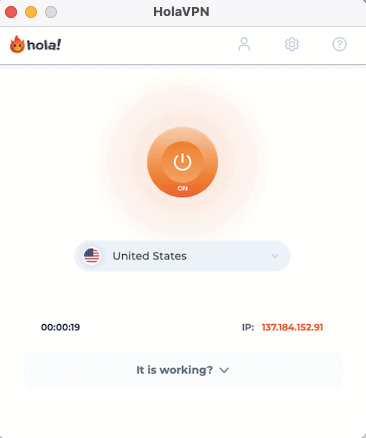
Both the Hola VPN browser extension and its desktop apps are relatively bare of features. There’s a server list with a search bar. In addition, when you’re connected, a button lights up and a prompt appears for you to send yes-or-no feedback to Hola. That’s all there is. The macOS app is notably minimalist.
Hola’s browser extension is different enough from its desktop apps that we’ll consider the pair as two separate pieces of software. If you’re using Hola for free, the Windows and Android apps allow Bright Data to use your computer as a residential IP. The browser extension apparently does not.
The Windows version is slightly more interesting. You can set Hola to connect automatically upon opening. It also comes with a VPN kill switch, which closes internet-capable apps if your VPN connection drops — even more important than usual when unvetted peer devices might be involved.
We’re not against a VPN that focuses on doing its job over adding unnecessary frills. NordVPN controls its feature releases carefully and it’s our favorite VPN, as you can read in our NordVPN review. However, there’s a difference between no-nonsense service and having absolutely nothing going on. Hola outright fails to justify the risk of using its service.
Hands-on Testing: How User-Friendly Is Hola VPN (70/100)
You might think Hola would have a hard time designing an unfriendly interface given how little you can actually do with it, but it still managed to throw some roadblocks in our path. The connect/disconnect button felt sticky and unresponsive on all platforms, and we had to wrestle with the browser extension to use the “favorites” feature.
Hola VPN Pricing: How Much Does Hola VPN Cost? (60/100)
Hola is free to use, but you’ll face draconian limitations and invasions of privacy. A premium plan lets you use it without limits, but Hola charges ridiculous prices, asking far more per month than many wildly superior VPNs.
Currently, it’s charging $14.99 for one month and $7.69 per month for a year. That annual price is just a little less than you’d pay for a year of NordVPN and Surfshark combined, two VPNs that blow Hola out of the water. Check out our Surfshark vs NordVPN article to learn just how good they are. Hola’s three-year plan is a little more reasonable, at $2.99 per month.
Pricing Plan Breakdown
Hola has only one paid pricing tier, which you can get in three durations. Premium removes time limits from the app, increases the simultaneous connection limit to 10, and, most importantly, means you’re no longer sharing your IP with Bright Data.
The most affordable way to pay for Hola is the three-year plan, which costs $107.55 ($2.99 per month). We couldn’t find any indication that you’ll be shunted onto a more expensive plan after those three years elapse. Payment methods include credit and debit cards, PayPal, Google Pay, Alipay, GiroPay, Sofort and iDEAL.
| Subscription: | Cost |
|---|---|
| 1 month | $14.99 |
| 1 year | $7.69 per month ($92.28 total) |
| 3 years | $2.99 per month ($107.64 total) |
Hola VPN Free Plan & Money-Back Guarantee
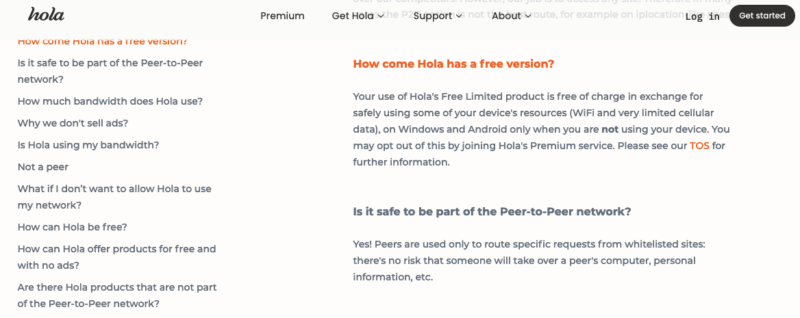
Hola’s free plan is its best-known offering and also its most risky. Using the Android app or Windows client without paying means that other users can browse with your IP address, though only on an approved list of sites, according to Hola. It also means Bright Data can sell your computer processing power for its clients to use as a residential IP address.
Free users get access to the entire server network with no data limits. Instead, Hola’s free plan limits how much time you can spend using the app before being temporarily cut off. The Hola FAQs are annoyingly vague about the time limits. In outside reports, we’ve seen everything from 30 minutes per hour to getting cut off for one minute after each hour of use.
In our actual tests, the cutoff points felt almost entirely random. Sometimes we had to wait one minute and sometimes five. At times, we used the VPN for an hour uninterrupted, only to then be cut off twice in a 10-minute period. There was very little rhyme or reason.
You can get a full refund within 14 days of purchase, but only if you have not used Hola Premium at all, which seems to completely defeat the purpose. iOS users must request their refund through Apple, not Hola.
Speed: How Fast Is Hola VPN? (80/100)
Hola VPN is extremely fast, but that’s not necessarily good news. There are two reasons a VPN can be fast. Either it has a balanced, well-maintained infrastructure, like we cover in our ExpressVPN review, or it’s not doing one or more critical aspects of its job.
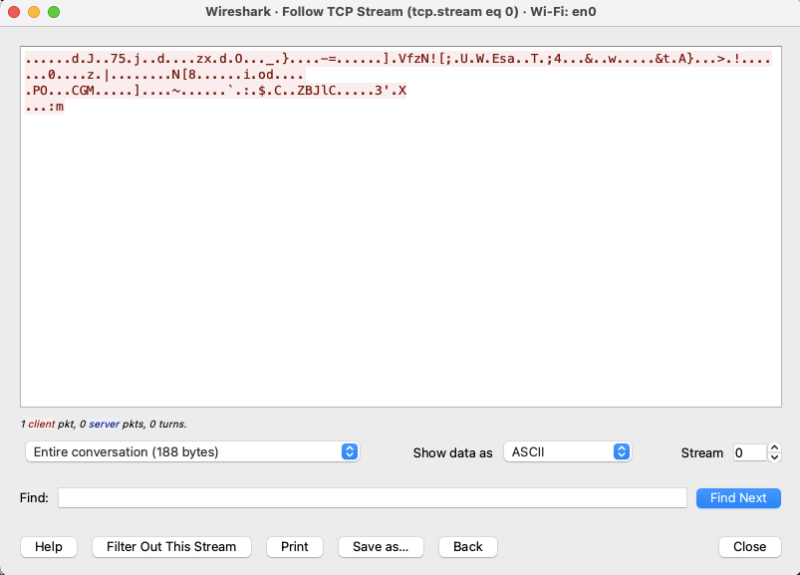
We know that one of Hola’s VPN protocols (PPTP/L2TP) is manifestly unsafe, so we’re inclined to think it’s fast because it’s cutting corners — and maybe entire sides. Our tests also showed massive slowdowns on certain runs, which could suggest that when Hola does encrypt your connection, speeds drop sharply. We explain our reasoning behind this claim below.
Hola VPN Speed Test Results
We used speedtest.net to check six different Hola locations against our unprotected speed three times and then found the average. The macOS and Chrome apps did not let us change our protocol manually, so these tests used a mixture of IKEv2 and PPTP/L2TP. As you can see in the tables below, the results were unconventional.
Security: Is Hola VPN Safe? (40/100)
No, Hola VPN is not safe. Until now, we’ve focused on how Hola falls short of its promises to users. Starting in this section, we’ll unpack a few of the ways in which Hola VPN is actively unsafe.
In 2015, a group of independent activists launched a website called Adios, Hola! to bring the risks of Hola to the public’s attention. Among other claims, they warned of an exploit that meant hackers could use the Hola network to execute programs on unsuspecting victims’ computers.
It’s already a bad sign when independent researchers have to go public about a vulnerability. Most experts prefer to let the company know in private first so it has a chance to fix the problem. Resorting to publishing an independent website suggests Hola refused to take action on a flaw that could feed malware directly onto its users’ devices.
According to the site, it gets worse. Hola released a fix in May 2015, but it didn’t actually close the vulnerability — just the method that the Adios, Hola! website used to demonstrate the exploit. It appears that Hola was more concerned about its public image than it was about ensuring it closed all potentially devastating loopholes.
Hola VPN Security Features
The only security feature you can actually interact with is the kill switch on the Windows desktop app. However, it takes a long time to work and is weaker than it should be — instead of cutting off your internet connection, it only closes the apps you specify. There are no malware blockers, ad blockers or obfuscation of any kind.
Privacy: Is Hola VPN Private? (10/100)
No, Hola VPN is not private. Hola’s privacy problems can be summed up in two words: Bright Data. This subsidiary company, originally known as Luminati, is a massive part of how Hola operates. The very first answer on Hola’s FAQ page reads: “Hola works by sharing the contributed resources of its users for the benefit of all and for business use by Bright Data.”
Bright Data sells commercial proxies that businesses can use for corporate intelligence. Businesses have always spied on each other to gain a competitive edge, but if they try to check on each other’s websites — say, to research stocks or prices at scale — they’re often blocked. Businesses pay good money for individual IPs and home networks that can slip the net.
You’ve probably guessed it by now, but the IP addresses Bright Data sells as proxies are the same ones that free Hola users “contribute.” It’s one of the clearest cases we’ve ever seen of “if the product is free, you’re the product.”
We want to note that Luminati/Bright Data didn’t invent the concept of selling residential IPs. Plenty of people sell their processing power on purpose. The difference is that those people are being paid, whereas Hola’s free users are only being compensated with restricted access to a mediocre VPN.

you’re the product this landing page is advertising.
Hola VPN Lawsuit
Bright Data selling your computing resources and not giving you a cut is bad enough, but a lawsuit filed in 2021 alleges that the rot goes even deeper. Apparently still ongoing, the lawsuit by former Luminati CTO Colin Shribman — Hola co-founder Derry Shribman’s brother — charges Luminati/Bright Data with using its network as a whole herd of Trojan horses.
Colin’s lawsuit states the following:
“Once a week, it is Luminati’s practice to use a Trojan horse that was planted in users’ computers…to transfer, save and process data on its servers… This information includes tracking the programs installed on users’ computers and the IP addresses they connect to.”
The filing goes on to claim that Luminati employed the botnet of Hola users’ computers to steal copyright-protected software from competitors and to commit click fraud that artificially boosted banner ad revenue. It also claims that one of Luminati’s clients was the Israeli surveillance firm NSO, which Luminati admitted was true.
As Hola defenders, Luminati and Bright Data will undoubtedly say that Colin Shribman’s allegations stem from bitterness over his own brother forcing him out of leadership. Even so, the Cloudwards team strongly recommends taking the charges seriously. Nothing in the filing strikes us as implausible, and Colin was well positioned to know the truth.
Privacy Policy: Does Hola VPN Keep Logs?
If the Colin Shribman lawsuit is true, then Bright Data absolutely keeps logs — and retains them even after users have quit the Hola network. We don’t have to take Colin’s word for it on this one, as Hola’s own privacy policy makes the problems clear enough.
Even the shadiest VPN services usually pay lip service to a “strict no-logging policy,” but Hola doesn’t even try. From the first lines of the Hola VPN privacy policy, we see a gobsmacking amount of information being collected and retained after creating a Hola VPN account.
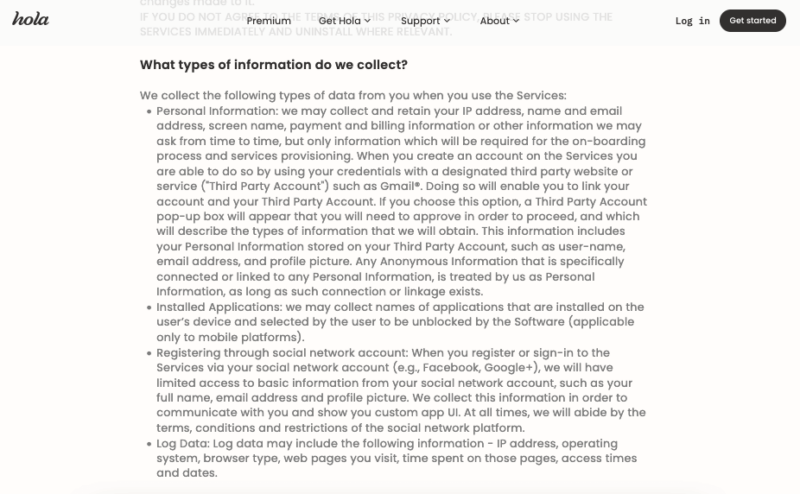
Collecting personal information for account setup is standard VPN practice, though our Mullvad review details one service that’s managed to cut it out. What is not standard practice is collecting “names of applications that are installed on the user’s device” or gathering “basic information from your social network account.”
For the record, there is no reason for your VPN to ever have access to your social media profile pictures. Nor does any reputable VPN reserve the right to log “IP address, operating system, browser type, web pages you visit, time spent on those pages.” The policy also does not promise that Hola won’t sell these logs, but it does claim it won’t sell your personal data.
Independent Audits
Hola VPN has not undergone any independent audits of its privacy policy. However, given the egregious liberties outlined in that policy, passing an audit wouldn’t make much difference.
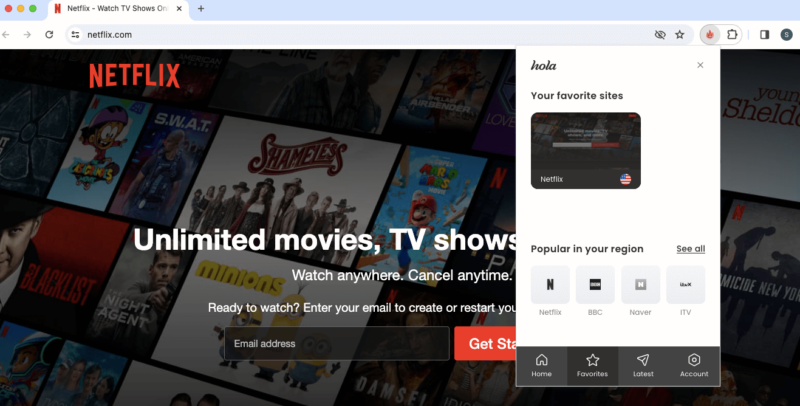
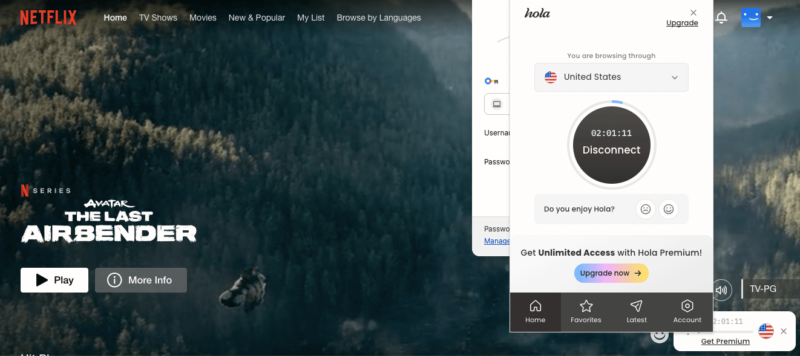
Streaming Performance: How Well Does Hola VPN Unblock Streaming Services? (70/100)
Hola is capable of getting around streaming blocks. We tested it on several different streaming sites in multiple locations and generally got through on the first try. However, we hesitate to call it a good streaming VPN given its inconsistent speeds. Our list of the best VPNs for streaming has some better choices.
| Streaming App: | Status |
|---|---|
Can Hola VPN Unblock Netflix?
Hola VPN unblocked Netflix on the first try with a U.S. server. We jumped around to IP addresses in several countries and got through the firewall every time. Even so, Hola won’t make our list of the best VPNs for Netflix anytime soon thanks to speed drops in several countries. Instead of Hola, choose a Netflix VPN that can handle 4K video in any location.
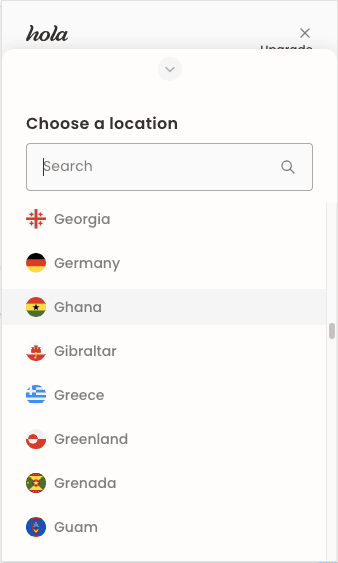
Server Locations: Where Are Hola VPN’s Servers? (60/100)
Hola’s server network is an enigma. Since it appears to use peer IP addresses for masking, not for actual rerouting, it could theoretically have server locations in every country where it has users, which it claims is every country on Earth. However, we don’t know the locations of its actual data centers or even how many of them there are.
As such, take its server list with a grain of salt, or perhaps the whole shaker. We’re especially suspicious of the Holy See location — can the Roman Catholic Church really not afford a better VPN subscription?
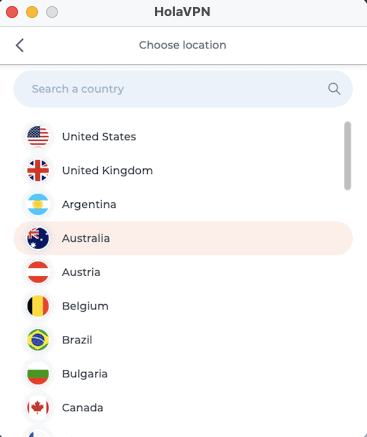
However, the desktop app on macOS has a significantly smaller server selection, so we’ve shared that information in the table below. It’s not clear what sets these servers apart, but since the macOS app is apparently not part of the P2P network, it may provide a clue as to where Hola’s actual data centers are.
Global Distribution of VPN Servers
| Region: | Countries | Locations |
|---|---|---|
| North America | 3 | 3 |
| South America | 4 | 4 |
| Europe | 25 | 25 |
| Asia | 5 | 5 |
| Africa | 0 | 0 |
| Oceania | 2 | 2 |
| Middle East | 2 | 2 |
You can see right away that this is a much less impressive list, but the truth is often more disappointing than the marketing. Africa is entirely ignored,and the showing in Asia is underwhelming. All told, there are servers in just 41 countries, a huge step down from big networks like the one listed in our CyberGhost review.
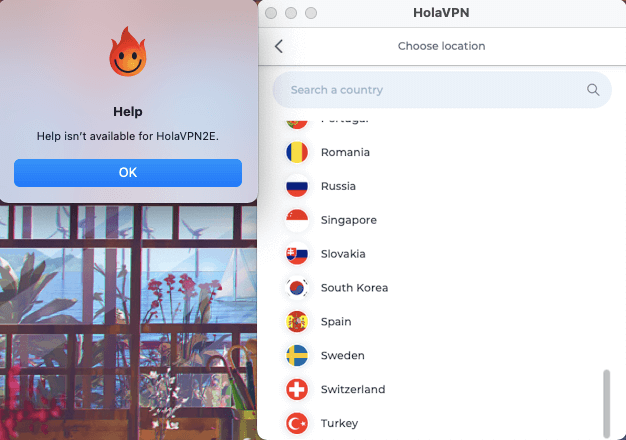
Customer Support: How Good Is Hola VPN’s Support? (40/100)
Hola’s website has a knowledgebase for self-help, but it’s limited and poorly written. Clicking the link to any setup guide automatically downloads the Hola installer before taking you to any kind of documentation. The setup guides themselves elide crucial steps, especially for manual setups.
Email Support Speed & Quality
There is no user forum and no live chat support, so we tried submitting an email ticket instead. We asked about where the data centers are physically located, since Hola isn’t forthcoming with that information.
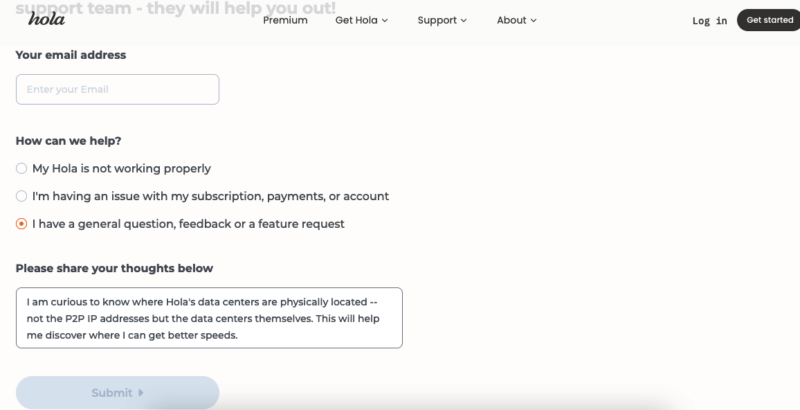
Hola VPN premium users get an answer.
After submitting the ticket, we were redirected to a page that informed us that only premium users could receive personalized help. It’s hard to know exactly what this means, but our guess is that free users will simply not receive a reply.
Hola VPN vs Other VPN Services
It’s easy to compare Hola to other VPN services, because pretty much any choice is better than Hola. Perhaps the most favorable thing we can say about it is that its violations are fairly open, unlike certain services — Ivacy and PureVPN being chief among them — that try to conceal their anti-consumer tactics.
We’d much rather spend time guiding you to a better VPN choice. Our ExpressVPN vs NordVPN matchup article helps you choose between two fast, reliable services, while our Surfshark review discusses an affordable alternative.
If you’re looking for a free VPN, Proton VPN is still the best choice, in spite of some recent missteps. Learn more in our Proton VPN review.
Finally, we highly recommend a more secure VPN with stronger protocols. Check out our full guide on the best Hola VPN alternatives for a complete list of better options.
The Verdict: Is Hola VPN a Good VPN Service?
No, Hola VPN is not a good VPN service. The more we look at Hola, the more obvious it becomes that its apparently bold central idea was never going to work. An actual peer-to-peer VPN would open way too many security holes, but in pulling back from that, Hola has become nothing more than a bad VPN service. That’s assuming it’s acting in good faith at all.
With this point, it should be clear that we strongly discourage using Hola VPN in any form. In spite of its decent speeds, this is not a service designed for your protection or enjoyment. Its purpose is to harvest your resources and sell them to its real customers, and it’ll do whatever it takes to convince you to join that scheme.
Have you ever used Hola? Did we convince you not to go through with downloading it? If so, which VPN will you be using instead? Let us know in the comments. Thank you for reading!
FAQ: Hola VPN
No, we don’t recommend trusting Hola VPN. Despite some minimal measures like restricting peer-to-peer connections to an allowed list of sites, it still leaves massive holes in both security and privacy.
If you use Hola for free on Windows or Android, any other user on the network may be assigned your IP address. You could be held responsible for what they do with it. You also agree to let Bright Data sell your home network as a residential proxy.
It is not, and we recommend that you avoid Hola VPN. Aside from the serious privacy violations, its security can’t be trusted, and its time limit system is frustrating and opaque. Choose Proton VPN, TunnelBear or Privado VPN for free service.
It’s not clear. In our tests, a request to wait or upgrade interrupted our usage every 30 minutes or so. Wait times lasted anywhere from one minute to 30.