What Is WireGuard? VPN Protocol Tunnel Guide for 2026
WireGuard is a novel VPN protocol that promises high speeds without compromising security. What is WireGuard, though? Join us as we seek to answer this question and discover everything there is to know about this VPN protocol.
WireGuard is an innovative VPN protocol that boasts strong performance and security paired with greater simplicity than other popular protocols. Like all other VPN protocols, WireGuard creates an encrypted tunnel for transferring data over the internet, ensuring user privacy and protecting sensitive data from prying eyes.
Initially designed as an alternative to OpenVPN, the WireGuard protocol represents new VPN technology, and it was designed with performance, simplicity and ease of implementation in mind. Since its launch in 2015, WireGuard has become one of the dominant VPN protocols, offered by most top-tier VPNs.
-
04/12/2024 Facts checked
Updated to reflect new developments in WireGuard, including its inclusion in the Windows kernel and support on other devices.
What Is the WireGuard VPN Protocol?
WireGuard is a modern VPN protocol designed with a focus on minimalism. It’s an open-source protocol based on a very slim codebase and modern encryption protocols, and it integrates directly into the Windows, Android and Linux kernels. It is so impressively lightweight that Linus Torvalds — the creator of Linux — called it a “work of art.”
Because it uses fewer lines of code, it has a smaller attack surface, making it less susceptible to cyberattacks. This also leads to reduced overhead and improved performance, and its kernel integration means it works better with the operating system’s network functionality than other VPN protocols.
Protect Your Privacy. Get Our Free VPN Guide Now!
- Comprehend the essential role a VPN plays in safeguarding your digital life
- Gain a deep understanding of how VPNs function under the hood
- Develop the ability to distinguish fact from fiction in VPN promotions
How Does the WireGuard Tunnel Work & What Is It Used for?
WireGuard was created as a way to replace older protocols using legacy encryption methods such as IKEv2 and OpenVPN. According to the WireGuard white paper, its creators intentionally avoided academic perfection, instead creating a lightweight yet imperfect protocol that solves the issues stemming from that imperfection with practical engineering.
How the WireGuard Protocol Works
At its core, WireGuard operates using the following mechanisms:
1. Cryptokey Routing
Whereas most VPN implementations make a distinction between user and server, WireGuard regards them both as peers. Instead of relying on traditional IP addresses for routing, WireGuard associates each peer with a unique public key and its related private key.
2. Kernel-Level Implementation
WireGuard operates at the kernel level on Windows and Linux, meaning it is integrated directly into the operating systems’ cores. Because it communicates directly with the Windows or Linux kernel, WireGuard offers a more efficient and streamlined approach to establishing a secure connection than traditional user space-reliant VPN protocols.
3. UDP Transport
The UDP transport layer offers fast data transmission. Because it is connectionless, its default implementation can lead to packet loss, unlike with TCP, which authenticates each incoming packet and guarantees no packet loss. WireGuard implements a separate package confirmation mechanism to fix this issue, so it can leverage UDP’s speed without compromising on reliability.
4. Secure Key Exchange
WireGuard bases its secure key exchange process on the noise protocol framework, using ChaCha20 for encryption, Curve25519 for key agreement and Poly1305 for authentication.
During the initial handshake, each WireGuard interface generates a private and a corresponding public key, which are exchanged between the peers to create a secret key used for encrypting communication between them.
Does WireGuard Use TCP or UDP? What’s the Difference?
WireGuard is built on the user datagram protocol (or UDP) transport layer, as opposed to the slower, yet more reliable transmission control protocol (TCP). This means that WireGuard doesn’t rely on handshakes to verify and establish a connection between the user and the server.
Despite this, the WireGuard protocol does still use a handshake, albeit a simple one, to exchange the symmetric keys that enable communication. This handshake is repeated at intervals in order to provide perfect forward secrecy.
WireGuard Use Cases
Although WireGuard-encrypted tunnels are primarily used for creating VPN connections, it is suitable for a wide range of applications, such as secure communication between devices in the internet of things (IoT), cloud communication or as part of other network security applications.
Which Devices Are Compatible With WireGuard?
WireGuard is compatible with all major operating systems, though it operates slightly differently on each one due to differences in kernel implementation.
What this means for you as a user is that, despite WireGuard’s high speeds on Windows, Android and Linux, it might perform as well (or only slightly better) as the user space-based OpenVPN on macOS and iOS platforms.
Which VPN Services Support WireGuard?
Though not all VPNs on our list of the best VPNs support WireGuard yet, some of our favorites do.
1. NordVPN — Best VPN With WireGuard
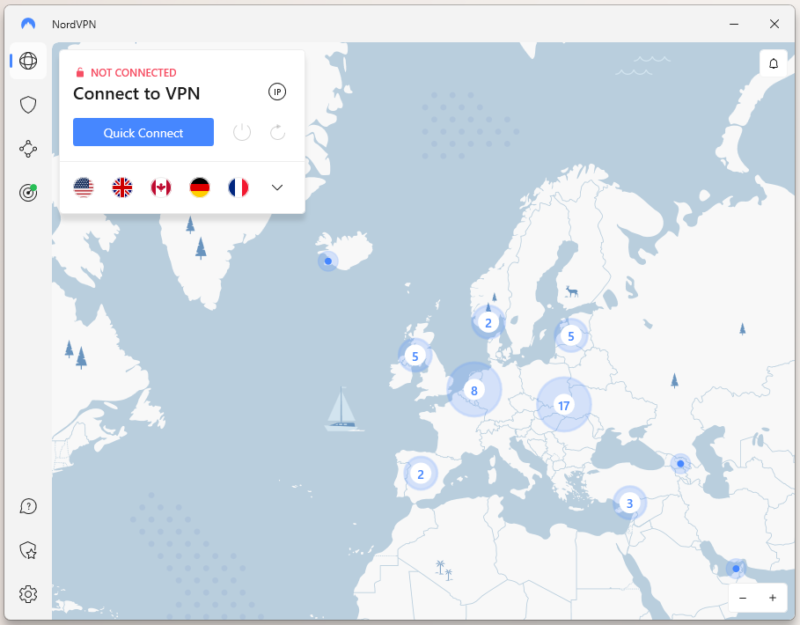
NordVPN is one of the best VPNs out there. It is also among the fastest VPNs, in no small part thanks to NordLynx — NordVPN’s own WireGuard implementation, which adds dynamic IP address distribution to the protocol. NordVPN also solves the lack of obfuscation by offering obfuscated servers even over WireGuard.
However, it is a premium VPN, so it comes with a higher price tag than others. It’s still decently affordable on longer plans, though. You can read our full NordVPN review for more info or try it out using the 30-day money-back guarantee.
- **VAT may apply
- Unlimited GB
- 10
- Yes
- *The prices are charged in the first billing cycle only. Renewal prices vary.
- Unlimited GB
- 10
- Yes
- *The prices are shown only apply for the first 12 months.
- Unlimited GB
- 10
- Yes
- **The prices are applicable only for the first 24 months. Secure, high-speed VPN Threat Protection Pro™: Anti-malware and advanced browsing protection Threat Protection Pro™: Ad and tracker blocker Password manager with Data Breach Scanner 1 TB of encrypted cloud storage Identity and SSN monitoring and alerts Credit monitoring services Up to $1M in identity theft insurance Up to $100K in cyber extortion insurance
- 10
2. Surfshark — Budget-Friendly WireGuard VPN
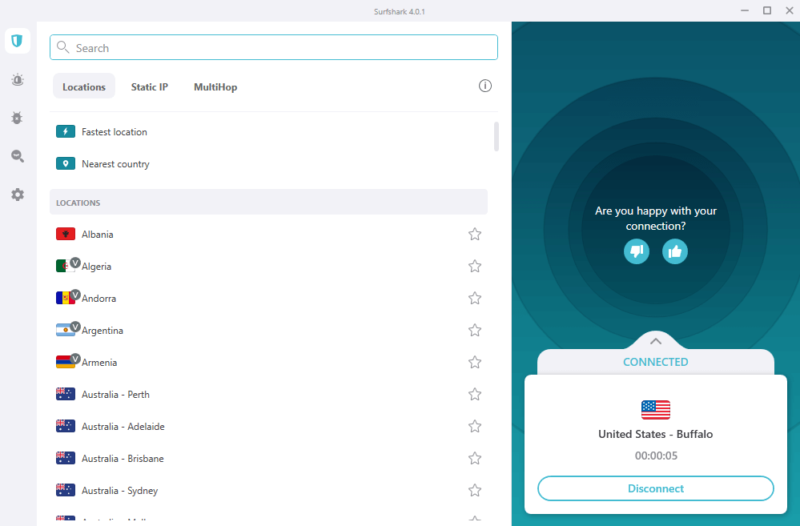
Surfshark is another excellent VPN provider that supports WireGuard, boasting super-fast download speeds. It is also fairly affordable for such a capable VPN. However, in our Surfshark review, we did take issue with its lack of torrenting support — peer-to-peer connections are only available over select servers.
In terms of pricing, Surfshark is among the cheaper VPNs, though its recent price increases have soured our opinion somewhat. We do still recommend Surfshark if you can’t squeeze NordVPN into your budget. Like NordVPN, it also offers a 30-day money-back guarantee that you can use to test the service before buying.
- Unlimited GB bandwidth, Unlimited devices, Secure VPN, Ad blocker, Cookie pop-up blocker. Pricing for the annual and biennial plans only apply for the first payment. Renewal fees vary.
- Unlimited GB
- Unlimited
- Yes
- Everything in Starter, plus Antivirus protection, Identity protection, Email Breach and Credit Card Alerts, Online Alias Pricing for the annual and biennial plans only apply for the first payment. Renewal fees vary.
- Unlimited GB
- Unlimited
- Everything in One, plus Data removal Pricing for the annual and biennial plans only apply for the first payment. Renewal fees vary.
- Unlimited GB
- Unlimited
3. Proton VPN — Best Free VPN With Wireguard

Proton VPN is a rare free VPN that we trust. It only uses the two most secure VPN protocols: OpenVPN and WireGuard. Developed by CERN scientists in Switzerland, Proton VPN is part of a larger digital privacy suite and an offshoot of Proton’s original end-to-end encrypted email business. We believe this showcases Proton’s dedication to user privacy and technical acumen.
Proton VPN has an unlimited free plan. It doesn’t place any hard limits on bandwidth or data use, but its free servers are often congested and slower than paid servers. The paid plans aren’t the cheapest, as they only come bundled with other Proton services, but you can make use of the free plan before deciding whether to upgrade. Read our Proton VPN review for more.
- Unlimited GB
- 1
- Yes
- 500 GB storage 1 user 15 extra email addresses for you Support for 3 custom email domains Unlimited folders and labels Unlimited hide-my-email aliases Dedicated customer support Ultra fast and private VPN Encrypted password manager Encrypted cloud storage for photos and documents Advanced account protection
- Unlimited GB
- 10
- Yes
- **Renewal prices differ for the 1-year and the 2-year plans. Price includes all premium Proton services (Proton Mail, Calendar, Drive, VPN, Pass, & Wallet)
- Unlimited GB
- 10
Configuration: How to Install WireGuard
You don’t install WireGuard yourself as an end user. Instead, you simply install the official WireGuard client or a VPN application that supports it. If you’re a system admin who needs to run a custom WireGuard implementation, you can find installation guides on the official WireGuard website.
- Download and Install a VPN
Download the VPN app of your choice from its website (on desktop) or from your device’s app store (on mobile). Then, install the VPN app by following the instructions in the setup wizard.
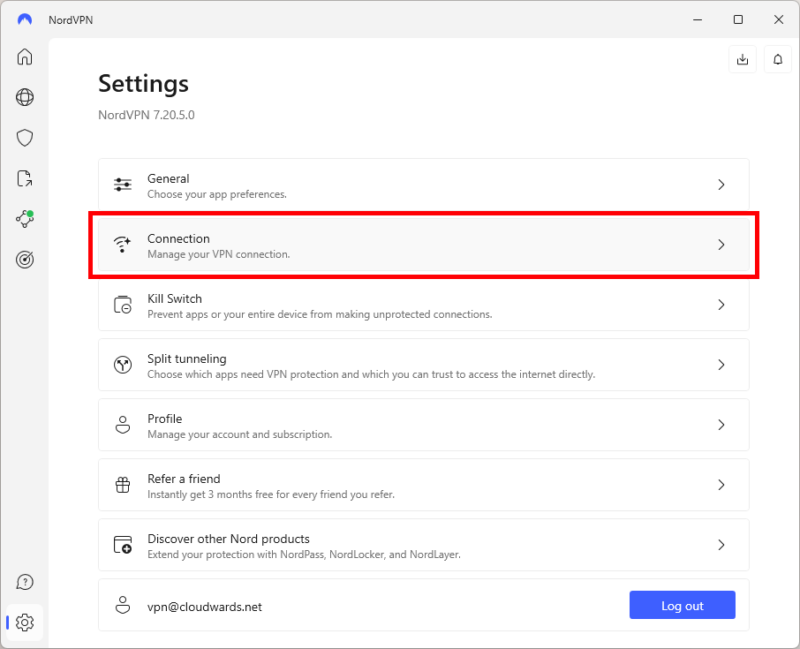
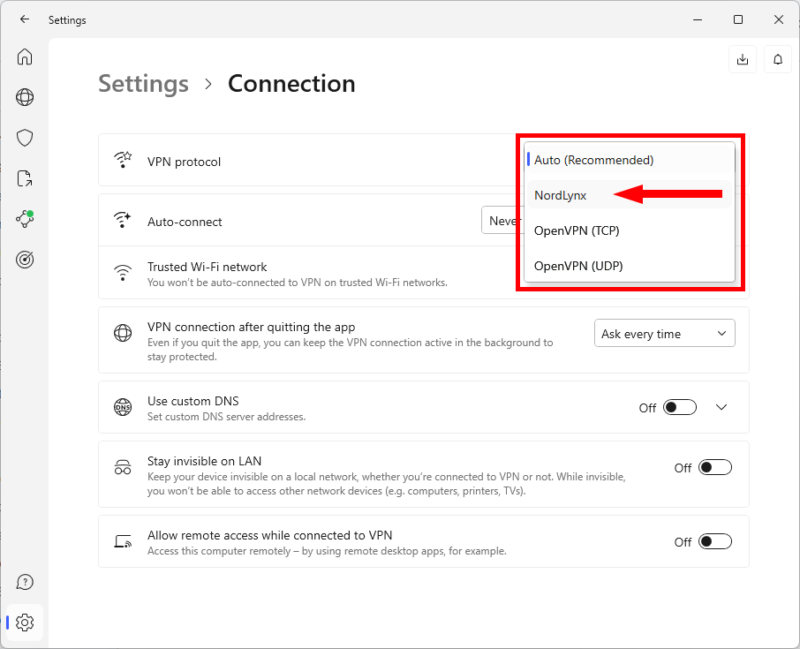
- Change the VPN Protocol to WireGuard
Change the VPN protocol from its default to WireGuard (or NordLynx if using NordVPN).
Final Thoughts
WireGuard is a modern and innovative VPN protocol that offers a unique combination of simplicity, performance and security with its lean codebase, advanced cryptographic algorithms and efficient design. Though it might not be suitable for all VPN applications, it is undoubtedly a strong contender in the VPN market, where speed and mobility are priorities.
As WireGuard continues to gain traction among VPN service providers, developers and users, it is likely we’ll see further improvements and extensions to the protocol. What are your thoughts on WireGuard? Do you use WireGuard or a different protocol in your VPN app? Let us know in the comments below, and as always, thank you for reading.
FAQ: VPN WireGuard Protocol
Yes, WireGuard is an excellent, fast and secure VPN protocol.
Yes, WireGuard is open source and completely free to use.
WireGuard is one of the fastest and most secure VPN protocols, which means you should use it whenever it’s available. However, Mac and iPhone users might not see the same speed benefits as others.
Not only is WireGuard compatible with Linux, but it was built primarily for Linux and is integrated into Linux’s kernel.