What is Perfect Forward Secrecy? A Guide for 2026
Cybersecurity is an ever-evolving field, with new threats, loopholes and exploits continuously being discovered and dealt with.
This running battle against cybercriminals presents an exceptional challenge for security experts, as tomorrow’s exploit can compromise today’s traffic, a problem that “perfect forward secrecy” was invented to prevent. So, what is perfect forward secrecy? Keep reading this article to find out.
What Is Perfect Forward Secrecy (PFS)?
Perfect Forward Secrecy (PFS) is a crucial security feature for websites, designed to safeguard communication, information, and data from future exploits and breaches. With PFS, each transaction’s encryption is isolated, preventing compromise of current and past interactions.
In the past, encrypted data relied on a single private encryption key held by the server, enabling decryption of all historic communication using a public key. However, this approach posed a significant security risk as attackers could eavesdrop on encrypted traffic for extended periods, storing data for potential misuse.
With all this data in hand, all the attacker needs to do is wait for any potential future security exploit that would allow them to get their hands on the server’s private key, which can then be used to decrypt all the data they have been harvesting over time.
How Perfect Forward Secrecy Solves the Problem
Perfect forward secrecy solves this problem by removing the reliance on a single server private key. Rather than using the same encryption key for every single transaction, a new, unique session key is generated every time a new data transaction occurs.
In effect, this means that even if an attacker manages to get their hands on a session key, it will only be useful for decrypting the most recent transaction, rather than all the data they may have collected in the past.
Instead of the standard RSA key exchange, these session keys are generated using either Diffie-Hellman encryption, or better yet, elliptic-curve Diffie-Hellman encryption. The encryption keys are ephemeral, meaning they’re not stored anywhere and cannot be reused for a later transaction.
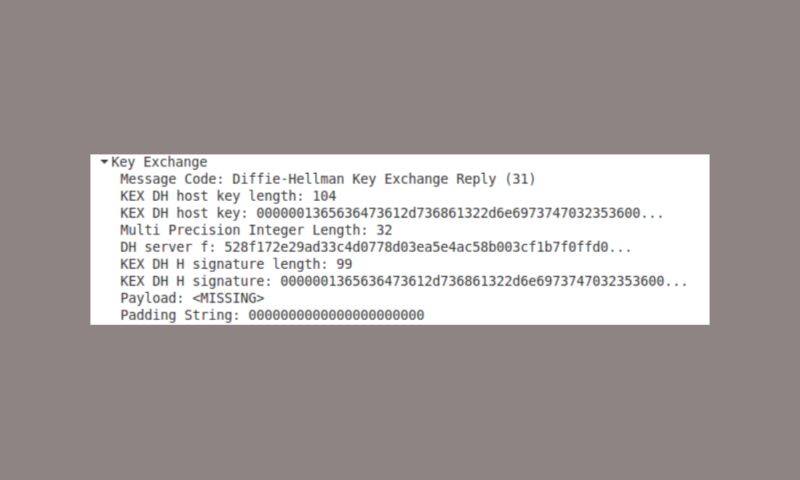
Similarly, the server’s private key will be completely useless to the attacker because it cannot be used to decrypt any of the traffic between the server and clients.
Although this method of attack might require more patience and resources than a single cybercriminal has access to, the same cannot be said for intelligence organizations.
Entities like the National Security Agency easily have the capacity to listen in on many encrypted connections, even going so far as to tap the giant underwater cables that connect servers across continents.
This massive capacity to collect data — combined with the institutional patience of an organization like the NSA — means that they have little trouble collecting and storing vast amounts of encrypted data.
In the event that some future exploit or loophole presents itself — allowing them to get their hands on the required private key — they can then use this encryption key to decrypt potentially millions or billions of data transactions in a single stroke.
For a more in-depth explanation of encryption, in general, be sure to read our description of encryption.
How PFS Keeps Your Website Safe
The most obvious way that perfect forward secrecy keeps your website safe is by providing you and your users with additional security in the event of a data breach. At worst, an attacker will only be able to decipher a single data transaction, and although this might still present a risk, the damage is greatly contained.
Furthermore, servers employing perfect forward secrecy present less attractive targets for attackers. Even though there’s still information stored on the server that’s protected by the original private key, this is all the attacker will be able to get their hands on, significantly limiting the payoff of the attack.
Of course, this is no guarantee against an attack, but it does make one less likely, as attackers might opt for more rewarding targets instead.
Google was one of the first major software companies to implement perfect forward secrecy on its servers. Because of this, it’s very likely that, at some point in the future, Google will use its position as the dominant search engine to encourage the adoption of PFS by rewarding sites that employ it by ranking them higher in its search results, as was the case with HTTP vs. HTTPS.
Perfect Forward Secrecy and Heartbleed
There is perhaps no better example for why perfect forward secrecy is essential than the infamous Heartbleed exploit. To understand why, it’s important to first know what Heartbleed is, and why it was so damaging.
Heartbleed exploits a bug introduced in 2012 to OpenSSL — one of the most popular implementations of the TLS (transport level security) protocol — but this wasn’t discovered until two years later in 2014.
Understanding SSL/TLS
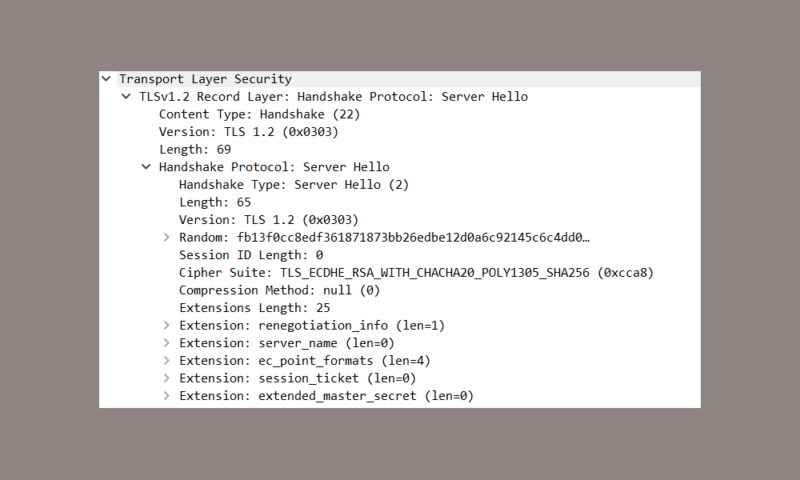
You don’t need to know exactly how TLS works, but in short, it is a security protocol that encrypts traffic between a client and server using a private encryption key, with HTTPS being the example you’re probably most familiar with.
Although answering the question “how does TLS work?” is outside the scope of this article, you can check out our article on SSL vs. TLS to learn more.
The bug takes advantage of the Heartbeat extension for TLS, which is designed to test TLS communication by sending a payload (usually a bit of text) as well as a number specifying the size of the payload. The server then responds by sending the payload back to the original sender.
The problem was that the server would not actually check the content of the payload, but just the number specifying its size. It would use this number to retrieve a certain amount of data from the memory buffer, which was intended to just be the original payload sent to the server.
However, because the payload itself was not checked, this opened up the possibility for sending a smaller payload than what was specified in the number representing its size. This resulted in the server returning not just the original payload, but also additional information stored in the memory buffer in order to reach the requested message size.
Heartbleed in Action
As an example, the malicious Heartbeat message might request the server to return the word “test” but specify that the length should be 500 characters. This would lead the server to return the requested word “test” but also 496 additional characters from the memory.
Although the attacker would have no way of determining exactly what information they would get back, there’s a good chance that these additional characters would contain sensitive information, such as the server’s private key.
Thus, once Heartbleed arrived on the scene, any cybercriminal that had spent any length of time listening in on encrypted traffic suddenly had a perfect avenue of attack for acquiring the private key of any server exposed to the bug.
Using these encryption keys, they could then decrypt all the data they had previously collected, which resulted in a huge amount of compromised information.
How to Enable Perfect Forward Secrecy on Your Server
Enabling the perfect forward secrecy feature on your server is actually a very straightforward process that does not require a significant amount of effort on the part of the system administrator.
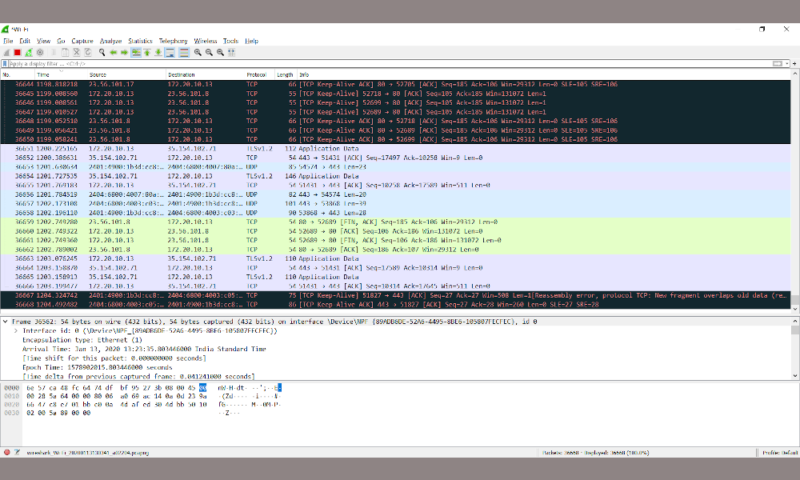
The process obviously varies depending on the server architecture you’re employing, so we will run you through how to do so with Apache and Nginx, two popular architectures.
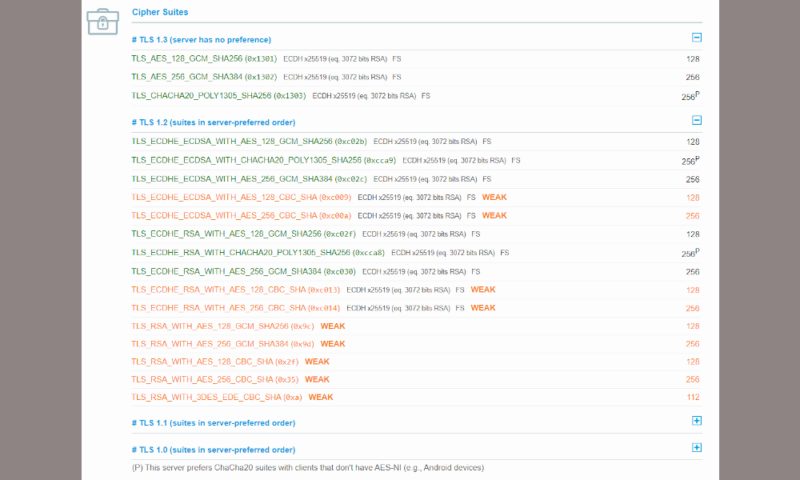
In general, what you need to do is set up your server to prioritize the DHE and ECDHE cipher suites, but you should still retain RSA support as a backup. This is because older systems and browsers may not support PFS, meaning they won’t be able to load your site unless you make sure that other cipher suites are still available.
For more specific instructions, we’ve compiled a step-by-step guide for how to enable perfect forward secrecy on Apache and Nginx servers.
How to Configure PFS on Apache
- Locate your SSL configuration with the command: “grep -I -r “SSLEngine” /etc/apache”
- Enforce the cipher order by typing: “SSLProtocol all -SSLv2 -SSLv3 SSLHonorCipherOrder on”
- Set the cipher order like this: “ssl_ciphers ‘EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDH’;”
- Finally, restart Apache with the command: “apachectl -k restart”
How to Configure PFS on Nginx
- Locate your SSL configuration by typing: “grep -r ssl_protocol nginx base directory” (replace “nginx base directory” with the appropriate path)
- Alter the configuration by entering: “ssl_protocols TLSv1.2 TLSv1.1 TLSv1; ssl_prefer_server_ciphers on;”
- Set the cipher order by typing the command: “ssl_ciphers ‘EECDH+AESGSM:EDH+AESGCM:AES256+EECDH:AES256+EDH’;”
- Restart Nginx with the following command: “sudo service nginx restart”
Final Thoughts
There it is, everything you need to know about perfect forward secrecy. Although there’s not much that consumers can do to encourage its use, it’s important to know that even encrypted data travelling over a secure connection is potentially vulnerable to a future attack.
The onus to implement perfect forward secrecy lies with server operators and system administrators, and the aim of this guide is to encourage its adoption, which would lead to a more secure internet for websites and users alike.
For users who are particularly concerned about whether or not their favorite websites use PFS transportation to secure their data, the Qualys SSL Labs test allows you to check just that. If a lot of your favorite websites aren’t up to snuff, the best way to protect yourself is hands down downloading a virtual private network to add an extra level of encryption to your traffic.
You can check out our list of the best VPN providers that will give you this extra layer of protection, or if you want to skip right to our top pick, check out our NordVPN review.
What did you think of our explanation of perfect forward secrecy? Did it shed some new light on a technical phrase you may have seen pop up more frequently in recent years, or are you still as confused as you were when you began reading? Let us know in the comments below. As always, thank you for reading.

