The Best Authenticator App for 2026: Two-Factor Authentication on iPhone & Android
Two-factor authentication keeps accounts safe by providing a second layer of security, making it much more difficult to gain access to data with a stolen password or device. In this review, we’ll pick the best authenticator app from five top contenders.
Two-factor authentication (2FA) is a standard practice for enhancing account security, with authenticator apps serving as a popular method for implementing 2FA and multi-factor authentication (MFA). Several factors come into play when picking the best authenticator app.
The app should offer strong security, user-friendly functionality, cross-platform compatibility and reliable backup options. The top five apps on our list have earned their positions due to their proven track records of meeting these criteria. They offer features like biometric authentication, strong encryption, offline token transfer and multi-user deployment options.
-
03/28/2024 Facts checked
This article has been updated with new information and fresh picks for the best authenticator app choices for 2024.
Cloudwards Editor’s Choice: Duo Mobile
Duo Mobile is our top choice for the best authenticator app because of its cross-platform compatibility, strong features and intuitive app. Its Duo Push authentication method simplifies 2FA by sending push notifications that users can approve when logged in on their smartphone.
It also has multi-account management and device health checks that verify device security before granting access. Duo Mobile uses location-based authentication as well as push notifications. When users receive a login request, they can see where it originated and flag potential malicious attempts at device access.
What Is Two-Factor Authentication?
Two-factor authentication (2FA) is a security process that requires users to provide two different authentication factors to verify their identity before access is granted to an account or system. These factors typically include something the user knows (like a password) and something the user has (such as a fingerprint, a smartphone or an email address to receive a code).
- Enhanced security –2FA provides additional security beyond passwords via an authenticator app, making it harder to access accounts without authorization even if the passwords are compromised.
- Reduced fraud risk — 2FA significantly lowers the risk of fraudulent activity and data breaches, and protects sensitive information.
- Regulation compliant — Tighter authentication security helps organizations meet regulatory requirements and industry standards for data security.
- Increased customer trust — 2FA reassures customers that their accounts are well protected and increases trust in an organization’s commitment to safeguarding data.
- Simplified login process — Features like single sign-on (SSO) integration, which allows users to securely access multiple apps with a single set of login credentials, makes signing in easier but is a risk to security. Authenticator apps for 2FA allow users to utilize SSO to streamline the login process while maintaining a high level of security.
Authenticator apps are best used in conjunction with strong password security, aided by a password manager app. Check out our list of the best password managers to choose the right one for your needs.
How Do Authenticator Apps Work?
Authenticator apps generate time-based one-time passwords (TOTPs) using a shared secret key stored on the user’s device. This key, combined with the current time, produces a unique code that changes every few seconds. When logging into a service, users enter this code along with their username and password to complete the authentication process.
What Is the Difference Between Two-Factor Authentication and Multi-Factor Authentication?
Two-factor authentication requires users to present two distinct authentication factors, whereas multi-factor authentication can require more than two. The factors are usually something users know, something they have and something they are (like biometric data). MFA is considered more secure than 2FA because it involves additional verification factors.
How Do I Choose the Best Authenticator App?
Keep the following points in mind when selecting an authenticator app:
- Look for a user-friendly interface, like what Duo Mobile and Authy offer.
- Cross-platform compatibility makes an app more convenient — OneLogin and Google Authenticator are great for this.
- Backup and account recovery options like what Duo Mobile offers help with preventing data loss.
- There are lots of great free options, so it’s not necessary to pay for an authenticator.
What Are the 5 Best Free Authenticator Apps?
The best free authenticator apps are easy to use and have plenty of features to keep your online accounts safe. Be mindful of potential security risks when downloading an authentication app that’s not on this list. Some free apps may request access to more personal information than they need to function, which can expose your data to security threats.
In addition, be cautious of the source of the app. Only download apps from the Google Play or Apple App stores, and take a look at the reviews to weed out any obviously dangerous software.
1. Duo Mobile
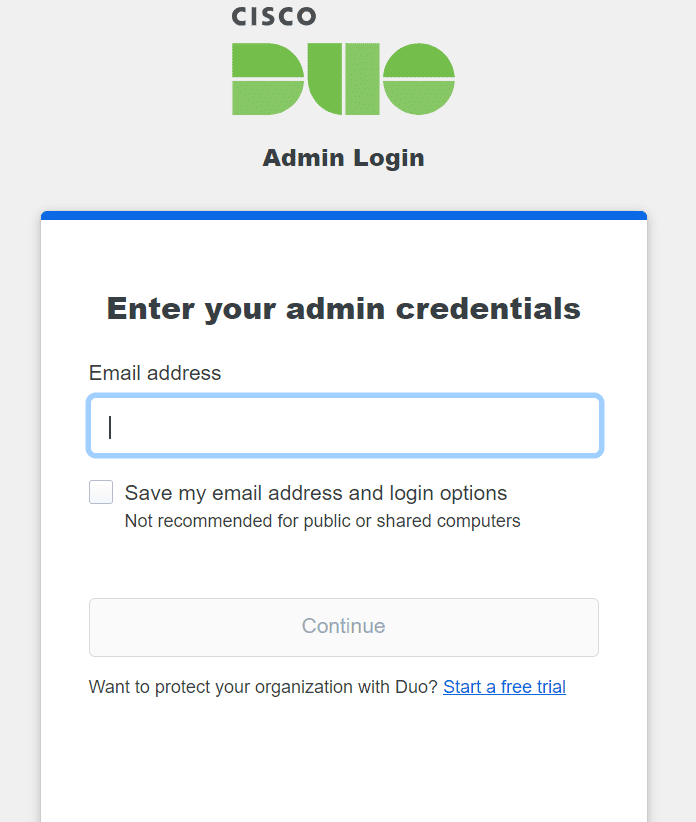
More details about Duo Mobile:
- Pricing: Free/$3
- Website: duo.com
Pros:
- API integrations for SOAR
- Real-time notifications
- RDP control
Cons:
- Authentication delays with free version
- Limited offline access
Duo Mobile has features that make it great for both individuals and businesses. RDP control enables two-factor authentication for remote desktop and Windows logins. API integrations for security orchestration, automation and response (SOAR) applications allow the exchange of real-time alerts and information between Duo Mobile and SOAR apps.
Duo Mobile offers free two-factor authentication; an extraordinarily intuitive, user-friendly experience; real-time notifications; and multi-account management. However, users have reported issues with offline access and delays in push notifications for logins, though we didn’t experience any during our testing.
2. Google Authenticator
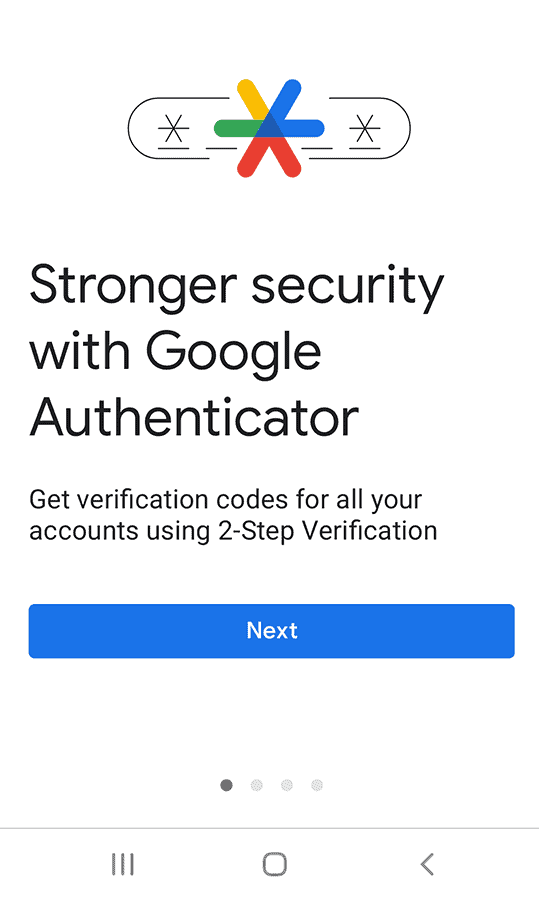
app with many useful features.
More details about Google Authenticator:
- Pricing: Free
- Website: play.google.com
Pros:
- Free
- Simple to use
- Operates offline
Cons:
- Not many features
- Each device requires manual setup
Google Authenticator was one of the first two-factor authentication apps and remains a reliable choice. It efficiently generates time-based one-time passwords without the need for an internet connection. Though it doesn’t support syncing between multiple devices, you can transfer your data by scanning a QR code.
Compared to other 2FA and MFA apps like Duo Mobile, Google Authenticator has some limitations, such as a lack of endpoint protection and less frequent updates. Nevertheless, Google Authenticator is widely used, simple and effective. It’s free on Android and iOS platforms.
3. Microsoft Authenticator
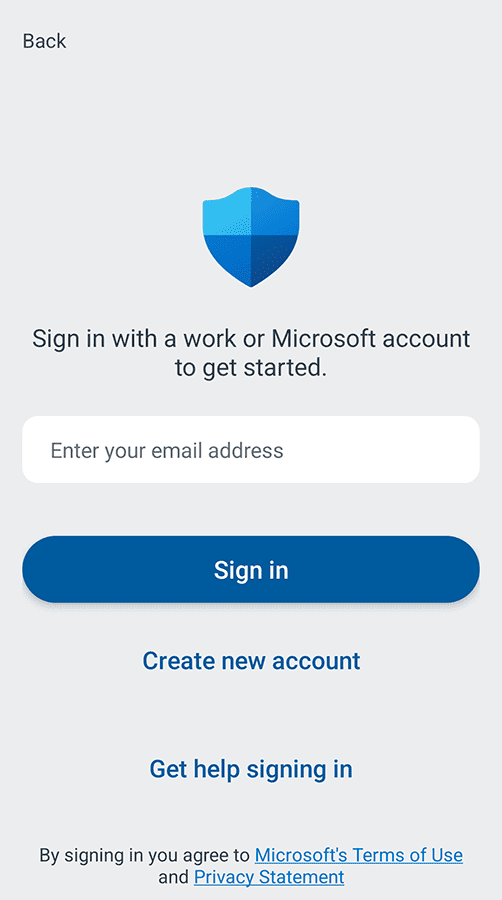
well for businesses and individuals.
More details about Microsoft Authenticator:
- Pricing: Free
- Website: microsoft.com/authenticator
Pros:
- Supports certificate-based authentication
- Integrates very well with Microsoft apps
Cons:
- Requires a Microsoft account for best results
Microsoft Authenticator is a powerful and user-friendly app that functions seamlessly with any services supporting TOTPs. It generates codes on your device with or without an internet connection and has passwordless authentication for Microsoft apps like OneDrive and Office 365.
The app’s certificate-based authentication lets organizations use device certificates for login attempts instead of conventional one-time passwords. Additionally, the app allows for cloud backup of account credentials through Microsoft’s servers on Android or through iCloud on iOS so that users can easily move their accounts to a new device.
The app can be locked, concealing 2FA codes until authentication occurs through the user’s designated method. Microsoft Authenticator is a free app, but it doesn’t work well with non-mobile platforms. If you want your authenticator to work well on both mobile and a laptop or PC, you may want to try one of the other authenticators on this list, such as Authy.
4. Authy
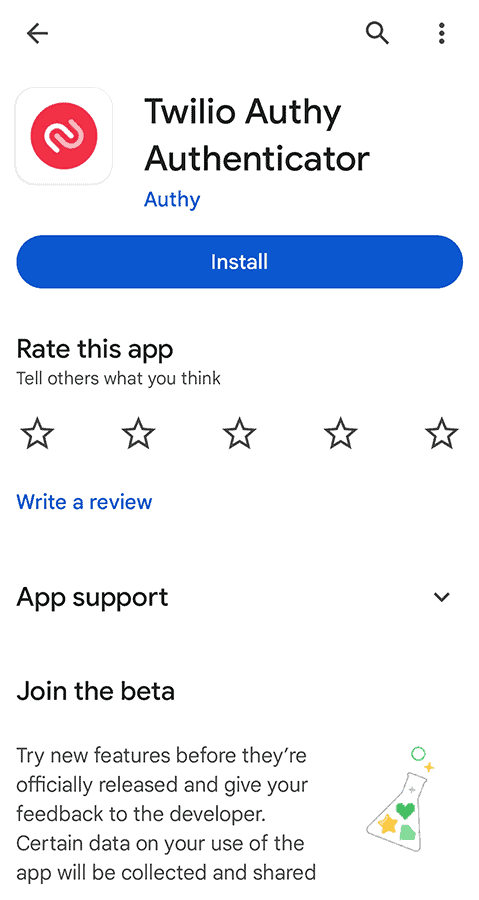
More details about Authy:
- Pricing: Free
- Website: authy.com
Pros:
- Online backups
- Multi-device support
- Cross-platform compatibility
Cons:
- Phone number & email required
Authy is a user-friendly 2FA and MFA app that is free for individuals. It sustains its free service by charging businesses for token generation. Authy can automatically synchronize across multiple devices, has widget support for Android users and is compatible with Apple devices, including the Apple Watch.
Authy’s 2FA tokens are compatible with any service that accepts TOTP-based authenticator apps. It maintains an extensive database of supported services, including popular password managers, cloud storage services, encrypted email providers and crypto wallets.
5. OneLogin
all the product’s features with no financial risk.
More details about One Login:
- Pricing: Starts at $2 per month
- Website: onelogin.com
Pros:
- 30-day free trial
- Easy browser extension
- Over 6,000 integrated apps
Cons:
- Only for businesses
- Slow customer support
Founded in 2010, OneLogin offers cloud-based identity and access management solutions to both small and large businesses and organizations. OneLogin integrates seamlessly with more than 6,000 pre-integrated applications through its single sign-on (SSO) interface.
OneLogin isn’t free, but it does offer a 30-day free trial so enterprises can test the product before committing. The pricing starts at $2 per user per month for single features like MFA or SSO. Alternatively, users can opt for both of these features plus an advanced directory for $4 per month.
Final Thoughts
2FA and MFA enhance account security, reduce fraud risks and increase customer trust. Duo Mobile stands out for its user-friendly interface and cross-platform compatibility. The Duo Push authentication simplifies the two-factor authentication process with real-time notifications and multi-account management.
A good authenticator app requires strong encryption, biometric authentication support and endpoint protection. A user-friendly interface helps you enjoy using the app, and real-time notifications lend practicality.
Which authenticator app features do you prioritize the most? Have you used any of the authenticator apps on this list? If so, what was your experience like? We would love to hear from you in the comments. Thanks for reading!
FAQ: Best Authenticator App
The most secure authenticator depends on your specific needs, but Duo Mobile is a highly secure option that offers endpoint protection, biometric authentication support and regular updates to address new threats.
Microsoft Authenticator is better because it offers advanced features that Google Authenticator doesn’t, like password locking, biometric authentication support and automatic backups. However, Google Authenticator is easier to use, has wide platform availability and receives better user ratings than Microsoft Authenticator.


