The 10 Best Encryption Software for Sensitive Data 2026: Encrypted Data on The Cloud
There’s no shortage of encryption software options available. All will encrypt your data, but some are better for advanced users, while others are a good fit for those new to encrypting data. We cover the best encryption software to help you get the right product.
If you have data that you don’t want anyone gaining unauthorized access to, you should consider using encryption software. Encryption software protects confidential and sensitive information like your medical history or financial information. There is no shortage of choices, so we list the best encryption software to help you find the right solution.
Encryption works by scrambling your data via an encryption algorithm, with the password you choose being the only way to decrypt it. There are several encryption algorithms, but the most common is AES 256-bit. Encryption software lets you encrypt folders and files, and some encrypt your whole disk. Read on to see which product is best for your needs.
-
11/30/2022
Updated with note about Dropbox’s acquisition of Boxcryptor assets.
-
03/15/2024 Facts checked
This article was rewritten with updated encryption software products and features.
How Do I Choose the Best Encryption Software?
Security is the first consideration when choosing encryption software. At minimum, you should look for AES 256-bit encryption, which is military-grade. Anything less isn’t worth considering. Other factors are cost, encryption key management and usability.
- Encryption: AES 256-bit encryption is the most commonly used and is exceptionally secure.
- Encryption key: An encryption key is used to decrypt your data. If anyone but you can access it, it poses a significant privacy concern.
- Cost: Some encryption software products are inexpensive; some are free and open-source.
- Usability: Encryption software can sometimes be overly complicated, though some put the user first, making it easy to encrypt your data.
A Comparison of Top Encryption Software
What Is the Best Encryption Software?
Cryptomator tops our list as the best overall encryption software. It is free, open-source and compatible with Mac and Windows. It is one of many free options that can meet the needs of different user types.
1. Cryptomator — Best Overall Encryption Software
UI, making it easy to encrypt files.
Pros:
- Free, open-source
- Easy usability
- Mobile app
Cons:
- Limited features
- Free iOS app is read-only
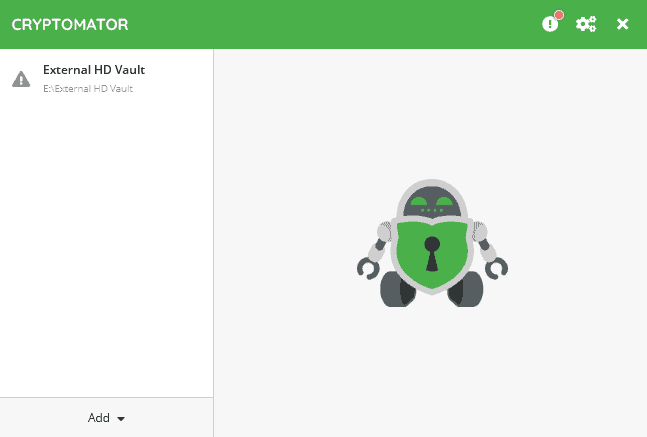
Cryptomator has a lot of flexibility, as you can encrypt data on your device or an external hard drive, or data from other cloud providers such as Dropbox. You start by creating a vault and then adding the data you want to encrypt. Each vault has end-to-end, zero-knowledge encryption. Cryptomator uses AES 256-bit encryption to protect your data.
Cryptomator’s user interface is simple yet effective. It walks you through the encryption process, starting by creating a new vault or working with an existing one. Although Cryptomator has few advanced security features, you can encrypt your data in a few short steps while creating multiple vaults.
your sensitive files using Cryptomator.
What Is Cryptomator’s Pricing and Value?
Cryptomator is free and open-source software available for Windows, Mac and Linux. You can choose to donate and support the service for as little as $16.24, which nets you a supporter certificate. The supporter certificate doesn’t unlock any additional features — just a dark mode for desktops.
iOS devices use a freemium model that’s read-only until purchased, while Android requires a one-time purchase that you can cancel within 14 days. For more information, check out our Cryptomator review.
2. VeraCrypt — Best Encryption for Advanced Users
looking to encrypt files using multiple volumes.
Pros:
- Encrypts hidden volumes
- Full-disk encryption
- Free, open-source
Cons:
- Not easy to use
- No mobile apps
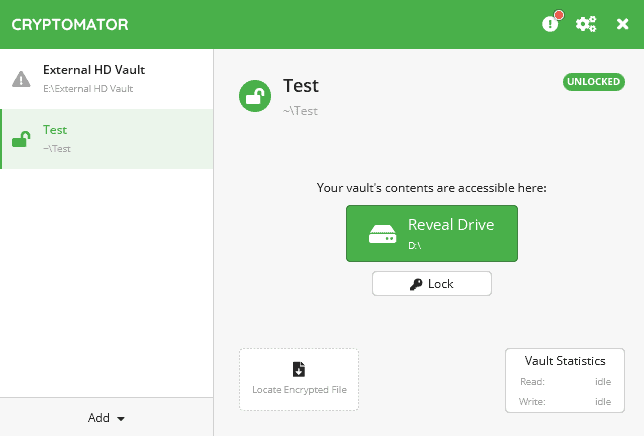
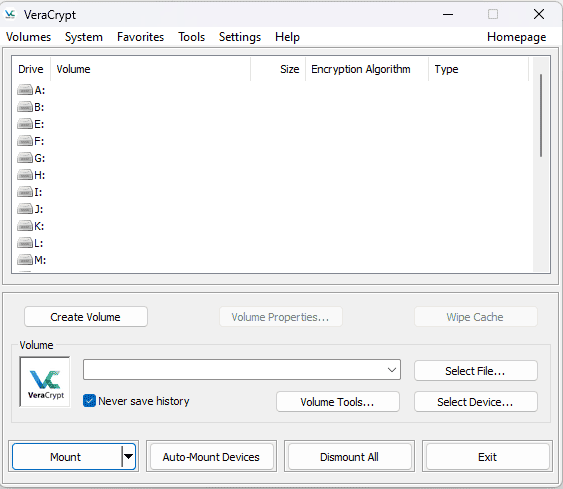
Similar to Cryptomator, VeraCrypt is an open-source encryption application with support for Mac, Windows, Linux and Raspberry Pi. Where VeraCrypt differs is its complexity. It offers many features and granular control over the encryption, which can be intimidating for those unfamiliar with the encryption process.
VeraCrypt uses AES 256-bit encryption to protect your data. Each encryption volume is zero-knowledge. With VeraCrypt, you can encrypt an entire disk volume or choose a file container. Moreover, you are not limited to your computer — you can create a volume on a USB or an external hard drive. Granular controls include choosing the encryption and hash algorithm.
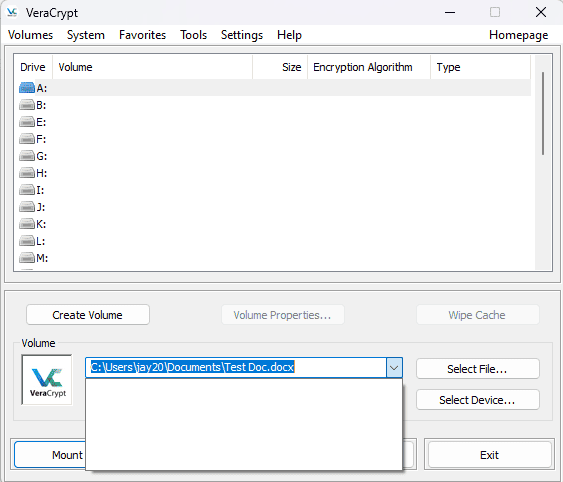
What Is VeraCrypt’s Pricing and Value?
Downloading VeraCrypt doesn’t cost a thing, as it is a free and open-source software product. You can provide a donation via PayPal, a bank transfer or even Bitcoin, but donating is not required to use all of VeraCrypt’s features. You can learn more in our VeraCrypt review.
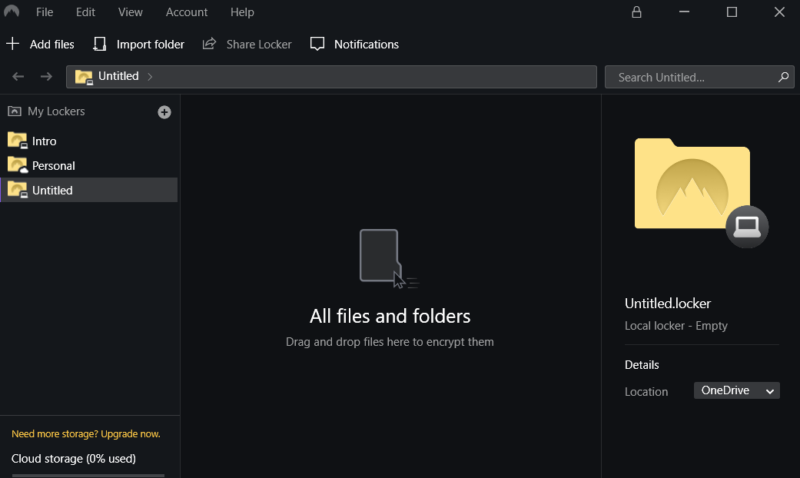
3. NordLocker — Best Mac Encryption Software with Cloud Storage Features
Pros:
- Multiple lockers
- Secure file request
- End-to-end encryption
Cons:
- Can get expensive
- Not great for collaboration
NordLocker encrypts your data by creating lockers that you can use to add folders and files. You are not limited by the number of lockers — only by the amount of storage space you have. Anything you put in a locker is secured with AES 256-bit encryption. Uploads have end-to-end encryption, and anything you share with others requires a security code to access.
NordLocker is as much a cloud storage solution as it is an encryption application. You can securely share with others, and if you have a premium account, you can use the encrypted “request files” feature. NordLocker’s desktop app is compatible with Mac and Windows, and has a mobile app for iOS and Android. Linux users can use NordLocker’s web access.
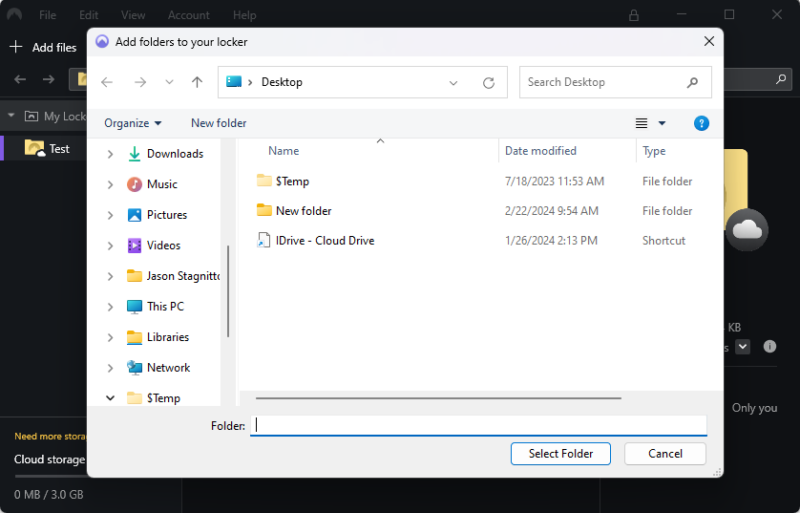
encryption tool creates an individual locker each time.
What Is NordLocker’s Pricing and Value?
NordLocker has two paid plans, one with 500GB and another with 2TB. The best value is to subscribe for a year, as the monthly costs are very high. The 500GB plan costs $2.99 per month, billed annually.
You can try NordLocker for free with a 3GB plan. We provide more details in our NordLocker review.
- 3GB
- 3GB
- 500GB
- 500GB
- 2000GB
- 2TB
- 2TB
4. BitLocker — Best Encryption for Windows Pro Users
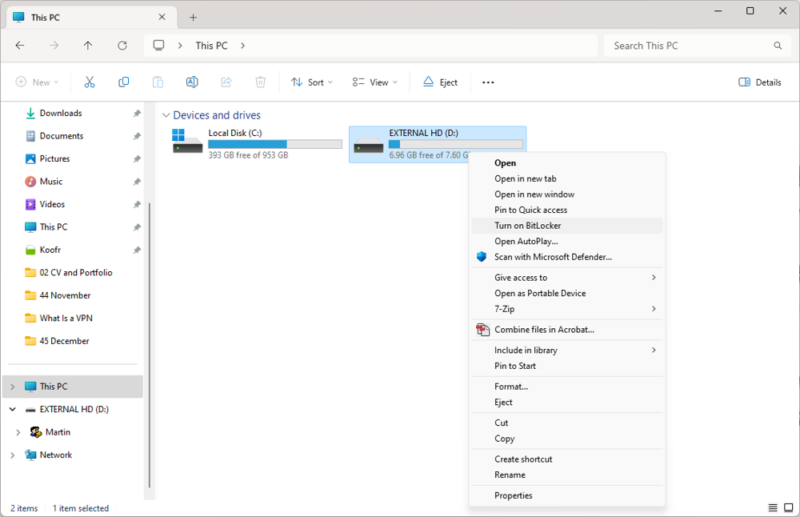
users that works well to encrypt entire volumes.
Pros:
- Encrypts entire volumes
- Built into Windows
- Easy to use
Cons:
- Requires two disk partitions
- Only for Pro users
BitLocker is an encryption program native to the Windows operating system. It is only available to Windows Pro, Enterprise and Education customers, which is limiting. Those with access to BitLocker can encrypt the entire disk volume, protecting more than just folders and files. It has end-to-end encryption and uses AES 256-bit encryption to protect your data.
BitLocker is easy to use and, like most encryption software programs, has a step-by-step process to encrypt your data. In addition to encrypting a disk volume, you can encrypt external hard drives or install BitLocker on a Windows server.
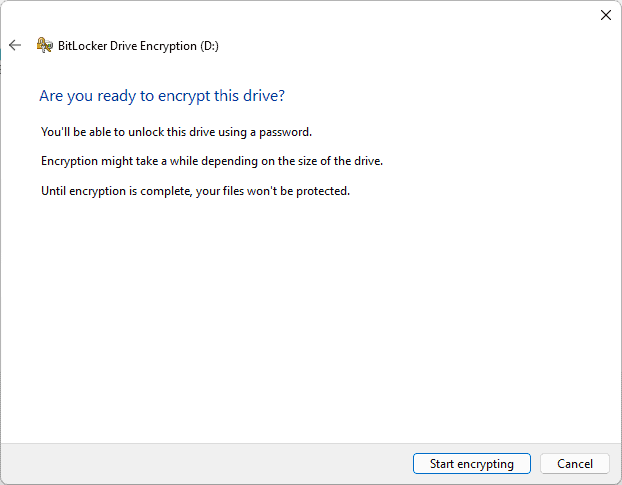
a few steps to encrypt a drive.
What Is BitLocker’s Pricing and Value?
BitLocker is not a standalone product, so you can’t purchase it separately from your PC. If you don’t have Windows Pro, you can upgrade for a one-time cost of $99. If you don’t have BitLocker, you can check out other ways to encrypt your hard drive.
5. AxCrypt — Best Encryption for Individual Files
features, including password management.
Pros:
- 128-bit or 256-bit encryption
- Cloud storage encryption
- Secure sharing
Cons:
- Dated desktop UI
- AES-256 not the default
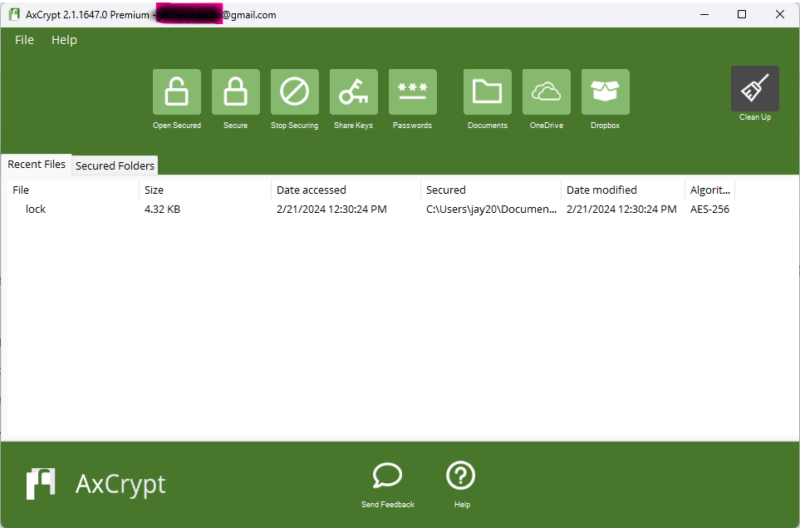
AxCrypt gives users plenty of options and control over which files to secure, the level of encryption and how to manage encryption keys. There’s also a basic password management feature, though better options are available. The best part of AxCrypt is that you can encrypt any file on your computer. However, securing folders requires a bit of a workaround.
AxCrypt creates a “My AxCrypt” folder in your documents folder. You can drag and drop items, which are secured with AES 256-bit encryption if you enable it from the “options” menu in the app. Alternatively, you can right-click on any folder on your computer and use AxCrypt to encrypt it. There’s also an option to “add secure folder” in the file dropdown menu.
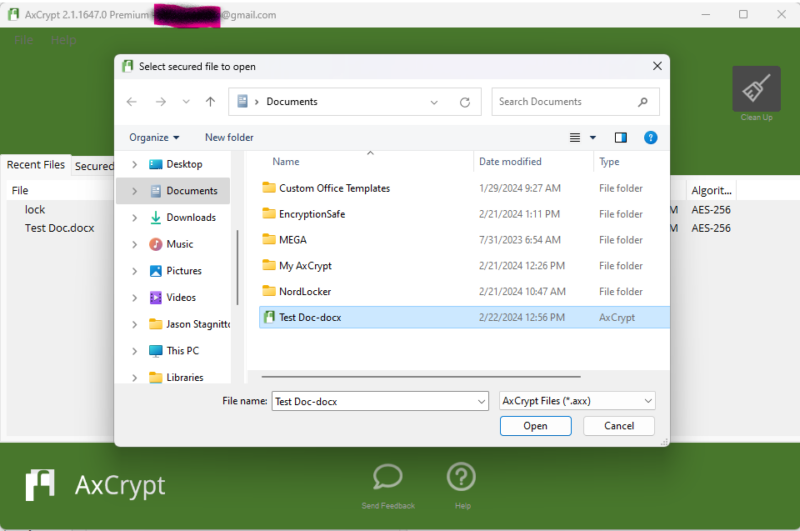
sensitive files with AxCrypt’s secure process.
What Is AxCrypt’s Pricing and Value?
AxCrypt offers three plans, two of which are for its encryption software. The other option lets you purchase only the password manager and costs $0.92 per month, billed annually. The personal Premium plan costs $4.75 per month, billed annually. The other option is the Business plan, which costs $10.33 per user per month, billed annually.
You can try AxCrypt free for 30 days to see if it’s the right fit for you. Check out our AxCrypt review for more details.
- Can only decrypt already encrypted files (view-only)
- Prices are billed in Euros Unlimited devices & passwords.
- Prices are billed in Euros File Limit: unlimited Data Limit: unlimited
- Prices are billed in Euros File Limit: unlimited Data Limit: unlimited
6. EncryptionSafe — Best Windows-Only Free Encryption Software
Pros:
- Zero-knowledge security
- AES 256-bit encryption
- Easy to use
Cons:
- Windows only app
- No full-disk encryption
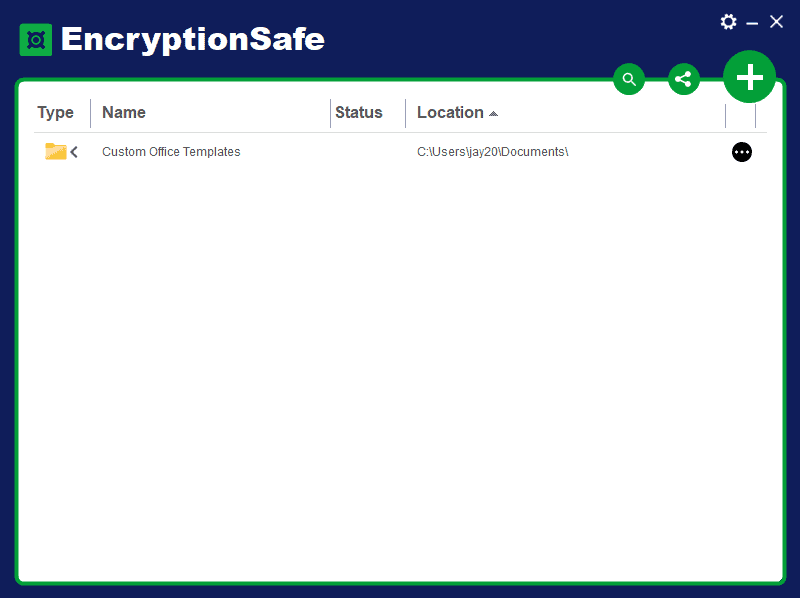
EncryptionSafe is a free encryption software designed for Windows. You can encrypt folders or files using AES 256-bit encryption. EncryptionSafe never has access to your data, making your account zero-knowledge. A paid version called PRO unlocks features like secure file sharing, two-factor authentication and permanent deletion.
The UI has a very simplified style, with only a handful of functional features. You can encrypt any folder or file on your PC, with the option to choose one or the other. You can decrypt any folder or file by clicking on the three-dot menu next to the item.
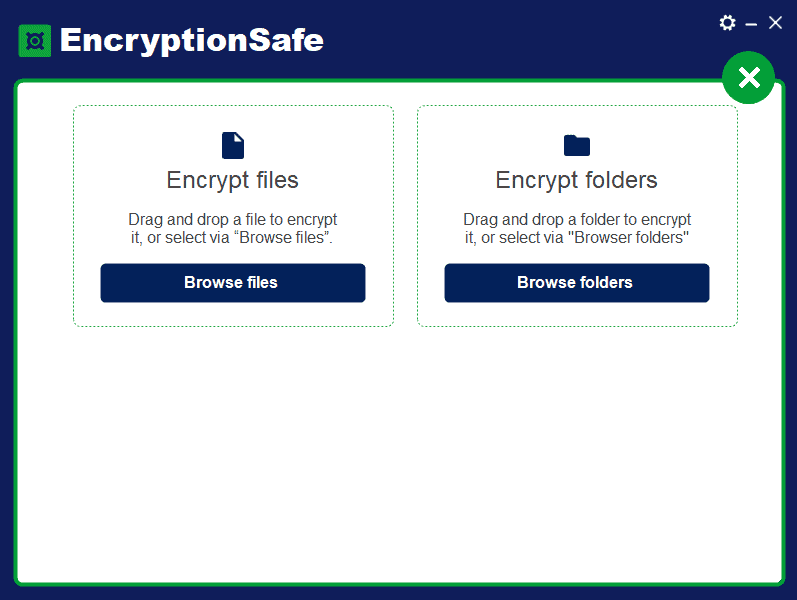
drag-and-drop method or browsing your library.
What Is EncryptionSafe’s Pricing and Value?
EncryptionSafe is a free software solution for Windows users. Upgrading to the PRO version involves a one-time fee of $19.95 for a lifetime license. However, it is not required — if you don’t plan to share your data, you can stick with the free version.
7. Folder Lock — Best Paid Encryption Software for Windows
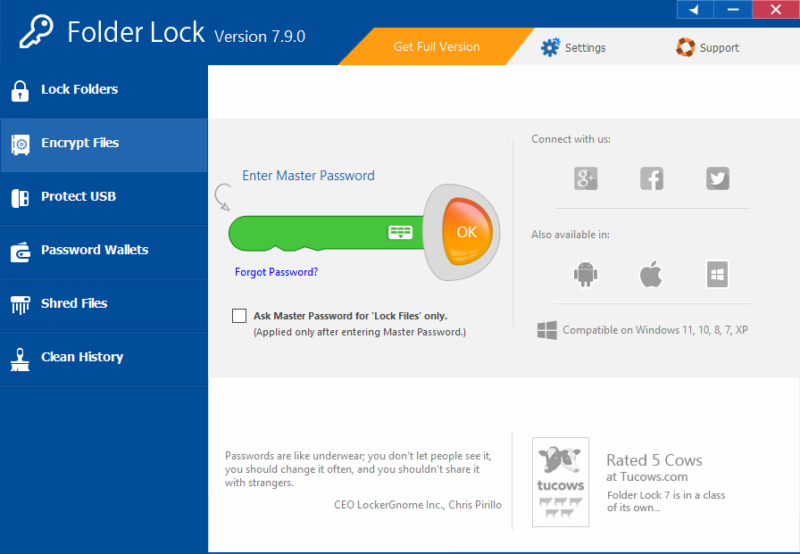
a master password to decrypt Folder Lock.
Pros:
- Password protection
- AES 256-bit encryption
- Private encryption
Cons:
- Windows only app
- No full-disk encryption
Folder Lock is another Windows-only encryption software product, though it does support mobile apps for iOS and Android. You can encrypt folders or files using drag-and-drop with the desktop app. Other features include encrypting USB or external drives and email attachments. The “password wallets” feature secures personal identification and other sensitive information.
Folder Lock has an excellent UI that is easy to use and understand, even for those who are newer to encryption software. Additionally, there are plenty of settings for users to customize how Folder Lock works. Options include password security, hack security and stealth mode.
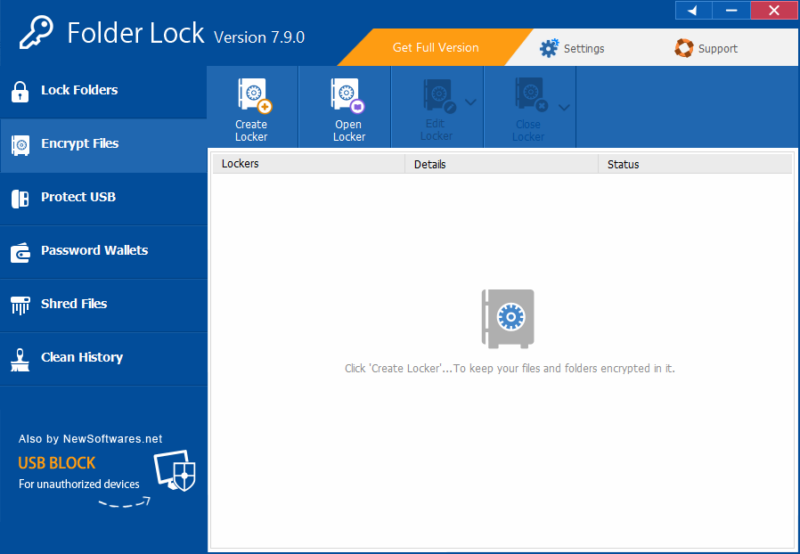
lockers to store your encrypted files and sensitive data.
What Is Folder Lock’s Pricing and Value?
You can download Folder Lock for free and use most of its features. It’s not clear how long the free trial lasts, but frequent notifications continually remind you. A paid plan has a one-time cost of $39.95, which gives you full access to the software.
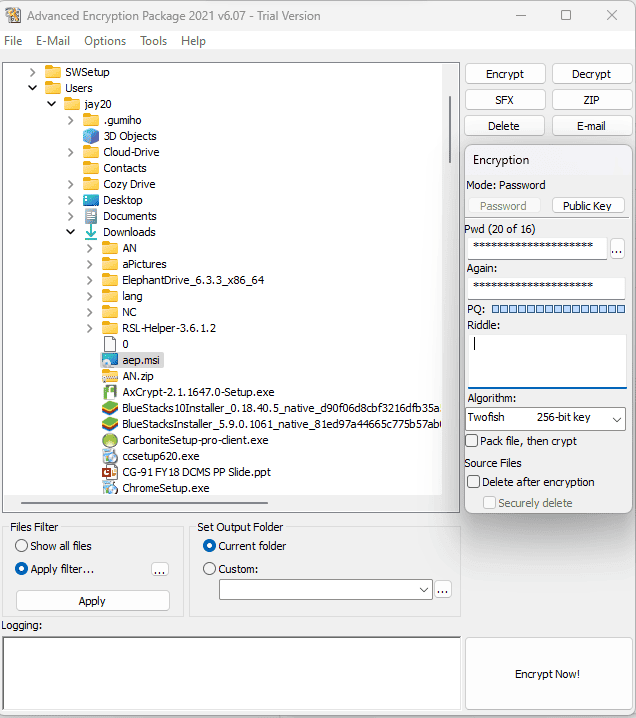
8. Advanced Encryption Package — Best Encryption Software for Advanced Algorithms
making it an excellent security software product.
Pros:
- Command line support
- Multiple algorithms
- Plenty of features
Cons:
- Dated UI
- Not great for beginners
Advanced Encryption Package is another Windows-focused product. There is no Mac version, nor are there mobile options. What Advanced Encryption Package lacks in device flexibility it makes up for in security customization. The focal feature allows you to choose from 17 encryption algorithms to protect your data.
The UI won’t win any aesthetic awards, though the window is logically arranged. Additionally, it does not take long to become familiar with how the encryption process works. You will see all your folders in the C: drive, and you can encrypt entire folders or individual files. Support is limited if you need help, but you can access how-to guides and an online manual.
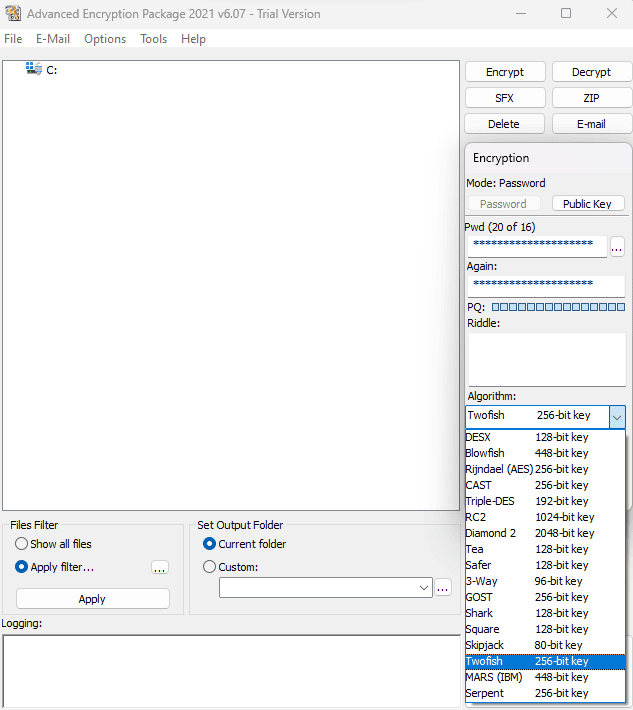
from various encryption algorithms.
What Is Advanced Encryption Package’s Pricing and Value?
You can download and try Advanced Encryption Package free for 30 days. If you decide to purchase a full license, it will cost a one-time fee of $49.95, with the option to purchase up to three PC licenses ($78 for two and $117 for three).
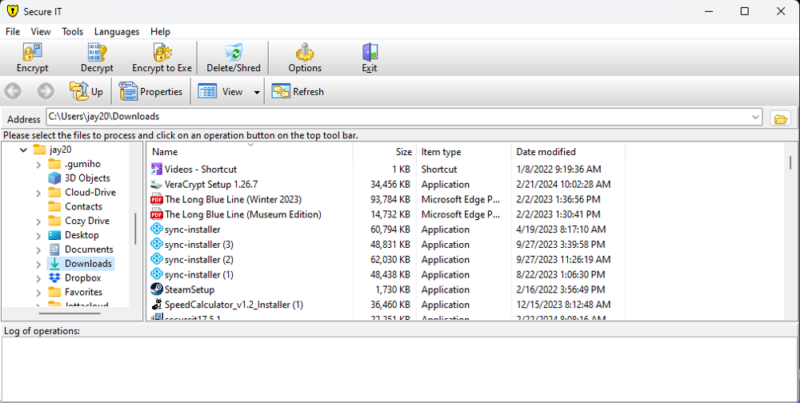
9. Cypherix Secure IT — Best Military-Grade Encryption Software
software tools to protect your encrypted data.
Pros:
- Encrypts multiple data types
- Blowfish 448-bit encryption
- Command line processing
Cons:
- Windows only app
- No mobile apps
Cypherix Secure IT has many features packed into a Windows-only package that blends seamlessly with your PC. It has a dated UI, but it is easy to navigate. Additionally, Secure IT supports a command line interface, giving advanced users plenty of encryption control over their data.
You can encrypt folders and files on your PC by choosing from the list on the left side of the window. The encryption process works by creating a unique password and choosing between two algorithms in AES 256-bit or Blowfish 448-bit encryption. You can also create an “encrypt to” .exe file, which is a self-extracting encrypted file that you can share with others.

protecting each encryption algorithm.
What Is Cypherix Secure IT’s Pricing and Value?
Anyone can try Cypherix Secure IT for free with a 30-day, full-functionality trial. To continue using Secure IT, you’ll need to purchase a license for a one-time fee of $29.95.
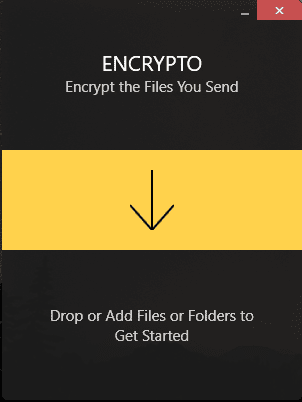
10. Encrypto — Best Encryption Software for Files
share securely or store on your computer.
Pros:
- Cross-platform encryption
- AES 256-bit encryption
- Secure file sharing
Cons:
- No full-disk encryption
- Limited features
Encrypto is very easy to use, with a clean and modern interface. You can encrypt any folder or file on your computer, and Encrypto is compatible with both Windows and Mac. Encrypto’s main appeal is the ability to encrypt a folder or file and easily share it with others. Additionally, you can create a new folder and encrypt it.
Once you encrypt a folder or file using AES 256-bit encryption, you can store it anywhere on your computer or embed it in an email or messaging app to send to others. Encrypto doesn’t support full-disk encryption, nor are there settings to customize the app. No account is required, but Encrypto probably isn’t the best option if you need encryption software with more granularity.
What Is Encrypto’s Pricing and Value?
Encrypto is a free download for anyone with a Mac or PC. There is no license requirement or trial period. Just download the app to start using it.
Which Files Need to Be Encrypted?
It is important to encrypt files that contain personally identifiable information, sensitive information like medical records or confidential documents. Ideally, you should encrypt all of your files. However, these file types should take priority when deciding what to encrypt.
Final Thoughts
Encrypting your data is the only way to protect it against unauthorized access. Using our top choice, Cryptomator, is an easy way to encrypt folders and files. However, any of the products on our list will work. As long as you encrypt your data, you won’t have to worry about unauthorized parties accessing your information.
Cryptomator is an excellent alternative to Boxcryptor. It offers similar functionality but with a different approach.
Have you used any of the encryption software products we listed? If so, what has your experience with them been like? Is there an encryption software product we missed? Let us know in the comments section below. Thanks for reading our article.
FAQ: Software for Encrypted Files
Cryptomator, VeraCrypt and NordLocker are three examples of the strongest encryption software.
AES 256-bit encryption is the most common and is virtually unbreakable. Stronger options include Twofish encryption and Blowfish 448-bit encryption.
Encryption software that uses the Advanced Encryption Standard (AES) is considered the best method for protecting encrypted data.
There are several different software products you can use to encrypt files. Cryptomator, VeraCrypt and NordLocker are three examples.