How to Encrypt an External Hard Drive Using Native or Third-Party Encryption Software in 2026
Anyone with an external hard drive has several options to encrypt it, most of which do not entail an additional cost. Mac, Windows and Linux have built-in encryption software, and plenty of third-party options are available. This guide will show you encrypt external hard drive options to protect your data.
Encrypting an external drive ensures the highest level of data protection. There are several ways to encrypt an external hard drive, with built-in software or third-party apps being the most prominent. This guide will cover the most accessible ways and teach you how to encrypt external hard drives.
Similar to hard drives, online backup or cloud storage, ensuring your external hard drive is encrypted keeps your data safe from unauthorized users or accidental leaks. Fortunately, the most common methods to enable encryption won’t cost you any money. Read on to learn how to protect your data regardless of your operating system.
-
03/07/2024 Facts checked
Article rewritten with updated steps for most recent versions of the Windows and Mac operating systems.
-
04/24/2024 Facts checked by Igor Kurtz
Added a section for Linux.
-
03/09/2025 Facts checked
We updated the article with more details on the encryption process and our how-to guides.
How Does the Encryption Process Work?
Most modern encryption tools use AES-256 encryption, which is a military-grade standard that makes your data virtually impossible to decrypt without the correct password. The encryption process works by using a mathematical algorithm to scramble your data, preventing unauthorized access. Only a password of your choosing can decrypt it.
Most OSs have built-in encryption software, making it easy to encrypt your hard drive. However, if you want something stronger, you can opt for third-party encryption software.
Full disk encryption protects everything on your drive, including temporary files, system files and deleted file remnants that may still contain sensitive information. Your data will remain private should the unexpected happen and someone unauthorized tries to access your content. Your data will remain protected against anyone who does not have the password to decrypt the external hard drive.
While the methods described in this guide focus on full disk encryption, you can also use file-level encryption to protect individual files or folders, which offers more flexibility but requires you to manually encrypt each important file or folder.
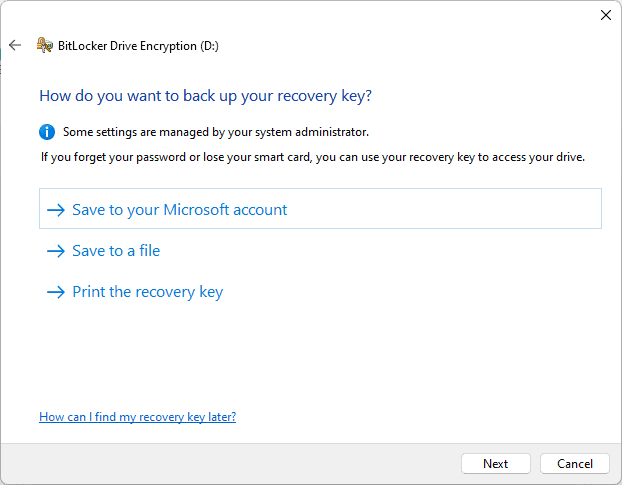
When encrypting your drive, you’ll typically create a recovery key — a special backup code that lets you access your data if you forget your password. Store this recovery key in a secure location separate from your encrypted drive. We recommend using a password manager with strong encryption or printing a physical copy to store in a secure location like a safe.
As you’ll see in the following sections, you’ll need a password to decrypt the hard drive before accessing its contents. However, if you lose or forget your password or misplace your recovery passkey, you won’t be able to access your data.
How Do I Encrypt an External Hard Drive on Windows Using BitLocker?
BitLocker is the best way to encrypt external hard drives on a Windows file system. However, to do so, you’ll need a Windows Pro account. If you don’t have one, don’t worry; you can use third-party encryption software, which we will cover below. If you do have access to BitLocker, follow this process:
- Open “This PC”
From File Explorer, open “this PC” and find the external drive you want to encrypt. If you don’t see it, make sure it’s connected.
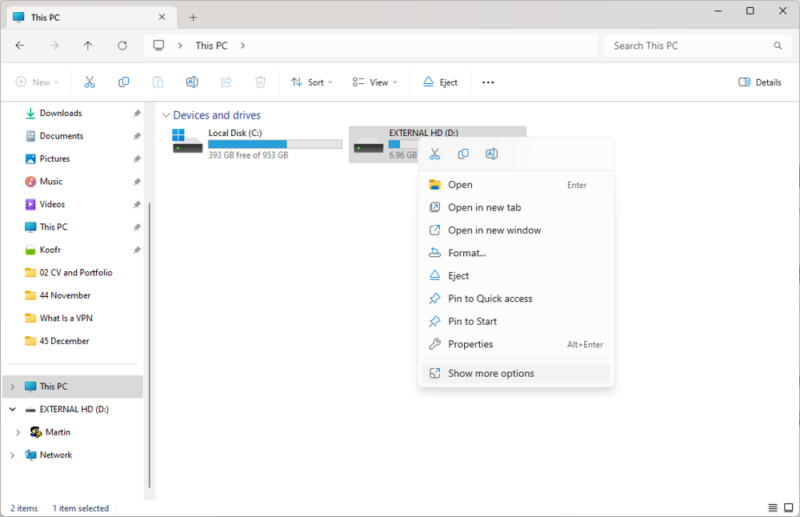
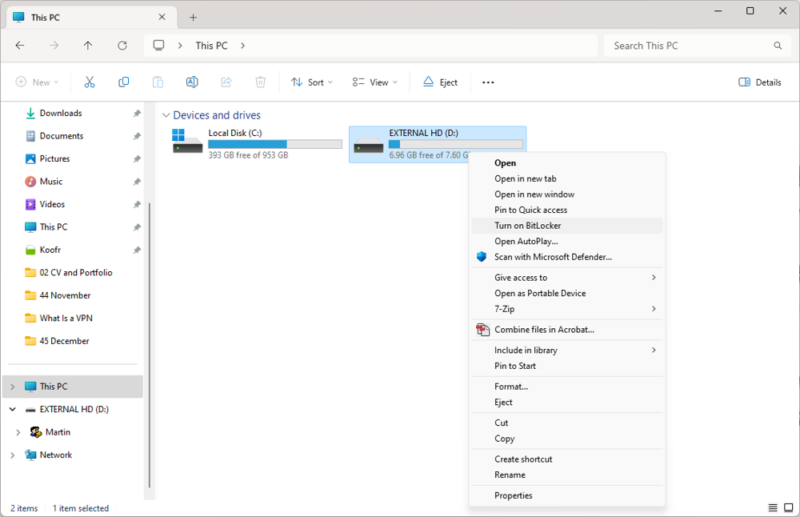
- Turn on BitLocker
Right-click on the external hard drive. You should see a “turn on BitLocker” option. Select “show more options” from the menu if you don’t.
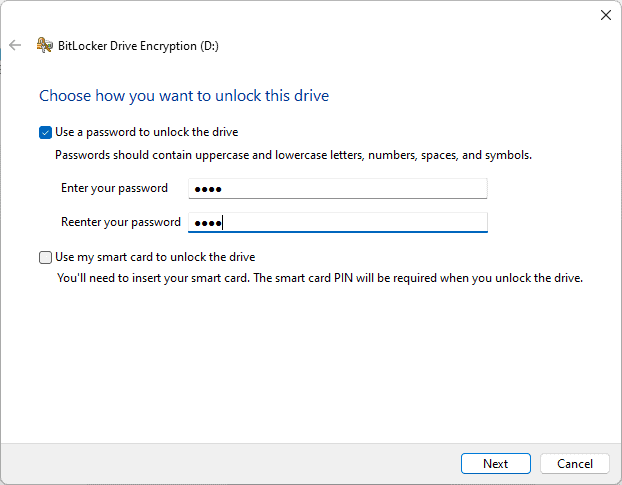
- Choose a Password
As you follow the prompts from the install wizard, you’ll need to choose a password. You can select this option if you have access to a smart card reader.
- Backup Recovery Key
Choose how you want to back up your recovery key. The recovery key is essential if you forget your password.
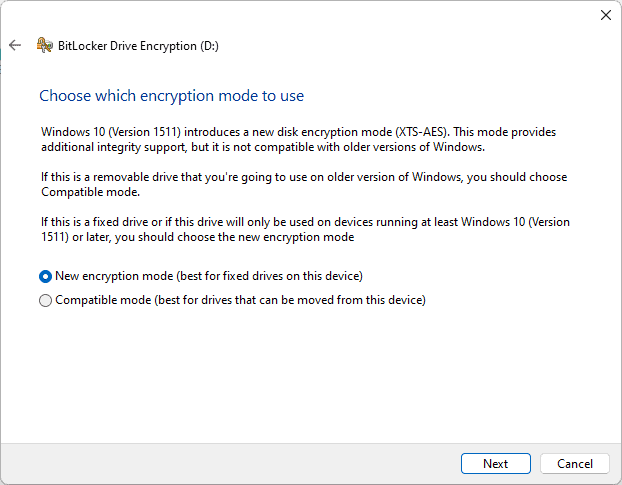
- Choose an Encryption Mode
You can choose “new encryption mode” or ” compatible encryption mode.” Select the best option for your needs. Compatible encryption mode is best for removable devices.
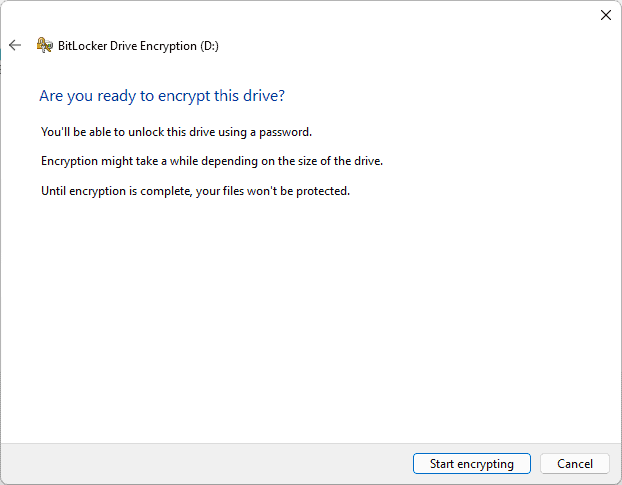
- Encrypt the External Hard Drive
When you’re ready, encrypt the external drive by clicking “start encrypting.” When finished, you’ll have an encrypted volume, and you will need the password the next time you access it.
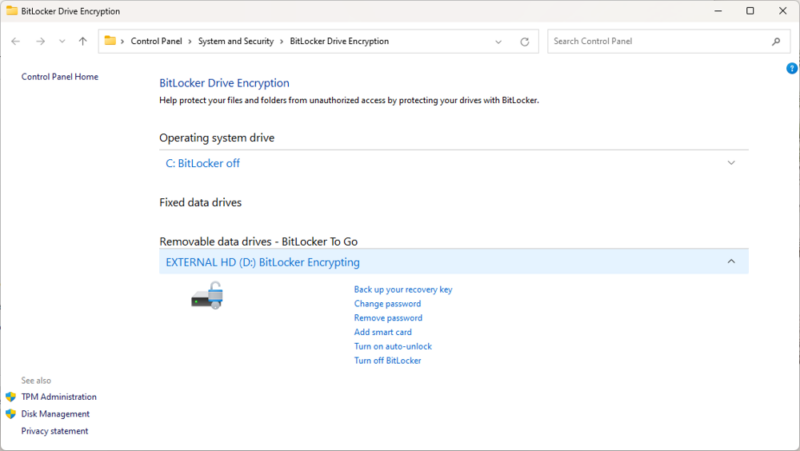
- Manage the Encryption
If you want to change your password or turn off BitLocker, right-click on the external hard drive from the “this PC” menu and select “manage BitLocker.” You’ll see several options on the page.
How Do I Encrypt an External Hard Drive on Mac With Disk Utility?
Mac operating systems come with the Disk Utility application. You can use it to encrypt external hard drives in a few short steps. Macs also have the FileVault app, which encrypts your hard drive. It does not work for encrypting external hard drives.
While FileVault is Apple’s built-in encryption tool for internal drives, the Disk Utility application handles external drive encryption using the same robust encryption standards.
Be aware of file format compatibility issues when encrypting an external drive that will be used across different operating systems, as an encrypted Mac drive may not be readable on Windows without additional software.
To encrypt an external hard drive, you will need to erase it. If you have data you don’t want to lose, transfer it off of your external hard drive first.
- Open Disk Utility
From the Launchpad or Finder, open the Disk Utility app.
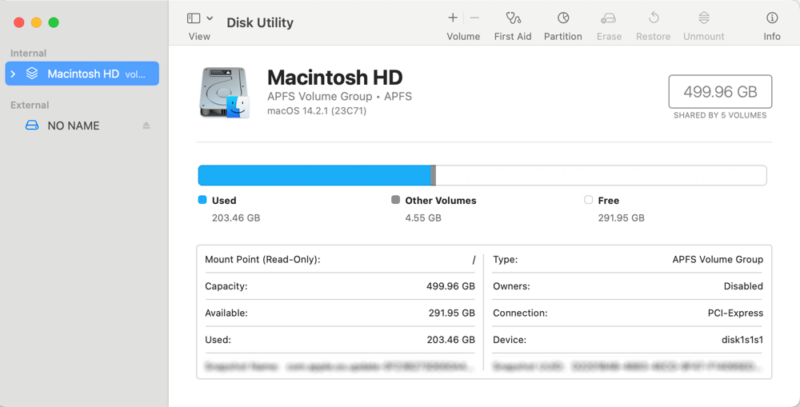
- Access the External Hard Drive
Locate the external hard drive you want to encrypt. If you don’t see your external hard drive after you connect it, go to “view” and “show all devices.”
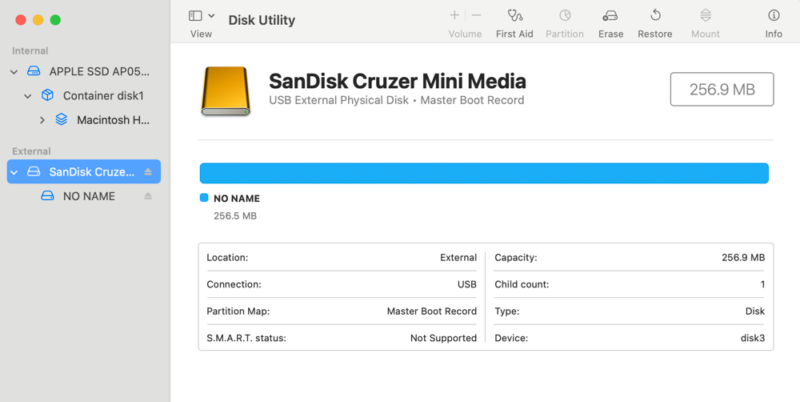
- Erase the External Hard Drive
Click on the “erase” icon in the menu bar. Rename the disk. Choose the GUID partition map from the “scheme” dropdown menu. From the “format” dropdown menu, choose the encrypted data type you want to use. When prompted, enter your chosen password.
Click the “erase” button.
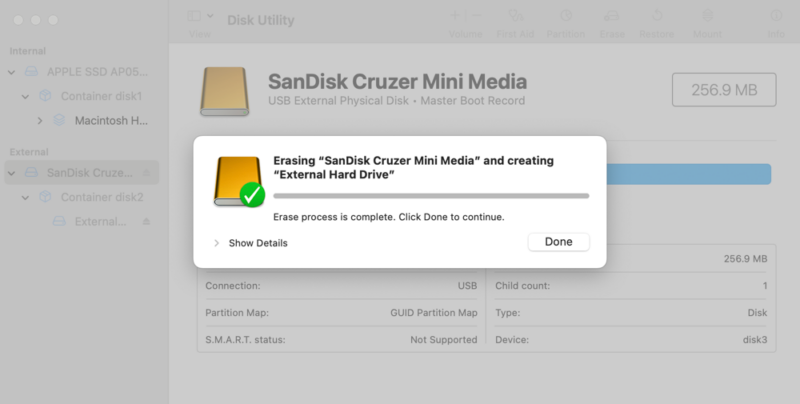
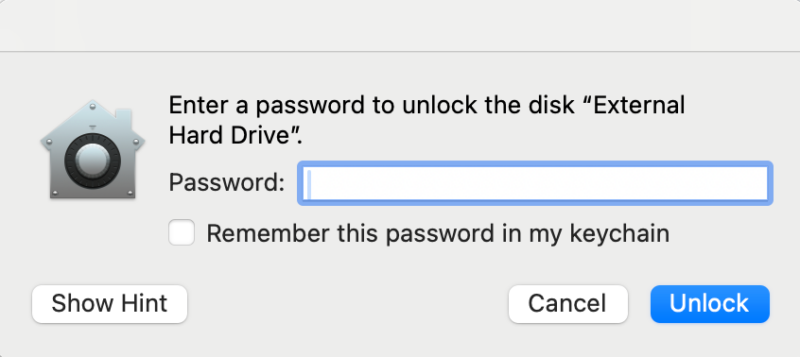
- Verify the Encryption
You’ll see the newly formatted external drive and the word “encrypted” next to it. Remove the device from your Mac and connect it again. You should see a prompt asking for a password to access the drive.
How Do I Encrypt a Hard Drive on Linux Using dm-crypt?
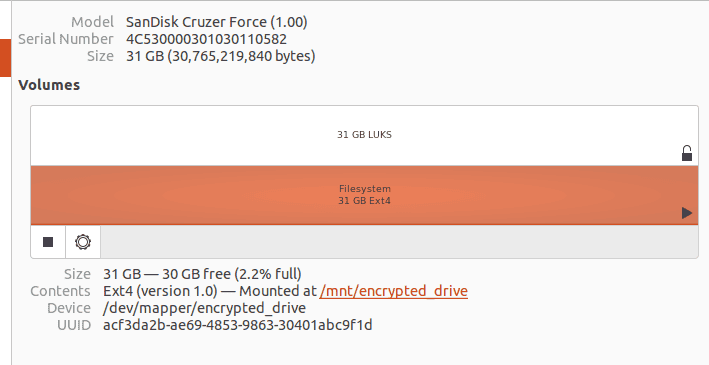
Linux has many distributions, and Ubuntu is one of the most used options. The dm-crypt method uses LUKS (Linux Unified Key Setup), which is the standard for Linux disk encryption that provides a platform-independent format for use in various tools. Here we’ll teach you how to encrypt your external hard drive on Ubuntu.
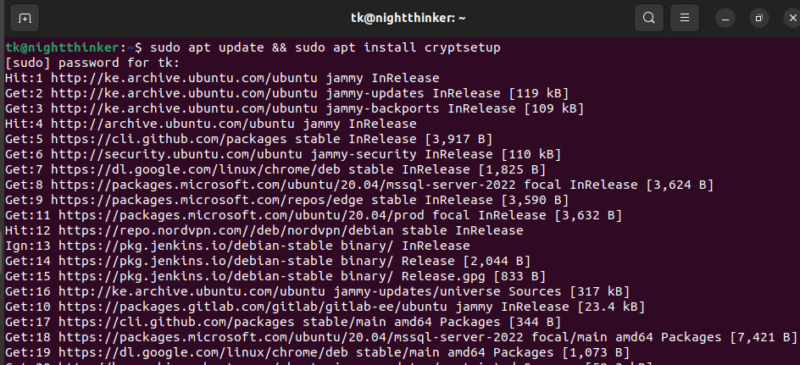
- Install Cryptsetup
Cryptsetup is an interface that configures encryption on block devices. You can install it using this command:
sudo apt update && sudo apt install cryptsetup
- Connect Your External Hard Drive
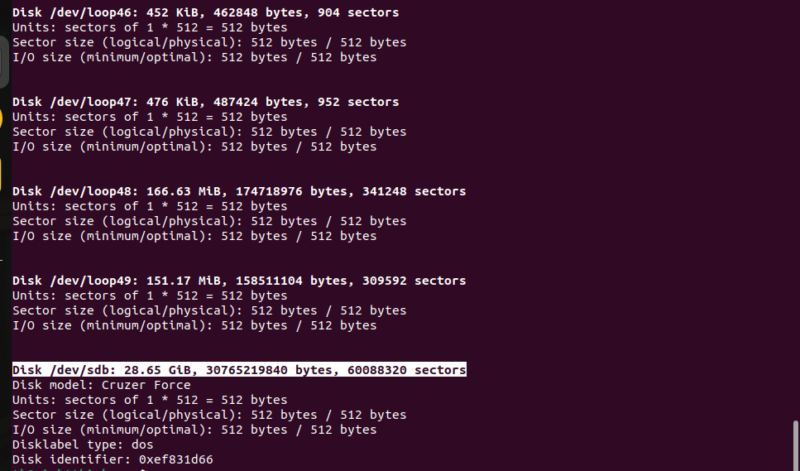
You can check if your drive is connected by browsing the “disks” menu. If it’s connected, you will see the drive below the internal partitions. You can also use this command to check: sudo fdisk -l
Our target disk is now Disk /dev/sdb
- Set Up the LUKS Header
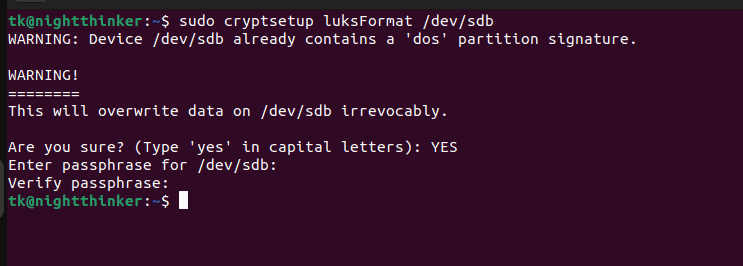
Run this command to set up the LUKS header. Remember to replace “sdb” with your target drive.
sudo cryptsetup luksFormat /dev/sdb
You will be prompted to write “YES” in capital letters to accept the changes.
Then, you will need to set up a strong passphrase and confirm it.
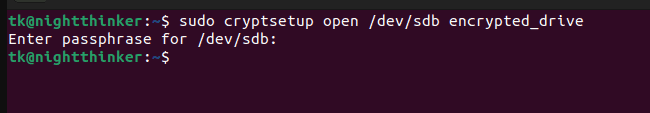
- Open the Encrypted Drive
Now you can set up a mapper device. All the contents you store on this disk will be encrypted. Run this command to get started:
sudo cryptsetup open /dev/sdb encrypted_drive
You can replace encrypted_drive with a name of your choice. You will be prompted to enter the passphrase you set in step three.
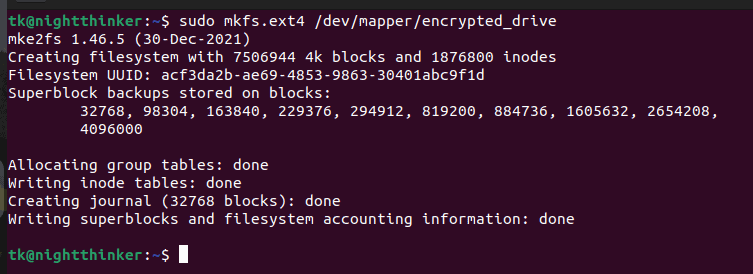
- Create a File System
The file system defines how data will be stored, organized and managed on your encrypted drive. Run this command to create one:
sudo mkfs.ext4 /dev/mapper/encrypted_drive
- Mount the Hard Drive
Mounting the drive makes it accessible and usable within the Unix system. To mount your drive, run these commands:
sudo mkdir /mnt/encrypted_drive
sudo mount /dev/mapper/encrypted_drive /mnt/encrypted_drive
You can now store and access all the encrypted files using this path: /mnt/encrypted_drive
How Do I Encrypt an External Drive With a Third-Party Encryption App?
Many third-party encryption apps exist, including those we feel are the best encryption software available. Third-party solutions create encrypted file containers, which are single files that contain multiple encrypted files and can be more portable across devices than fully encrypted drives.
One such option is Cryptomator. Once you download and install the app, you can encrypt your external drive in a few short steps.
- Start Cyptomator
After downloading and installing, find the app and open it. You should see a window asking if you want to add a vault.
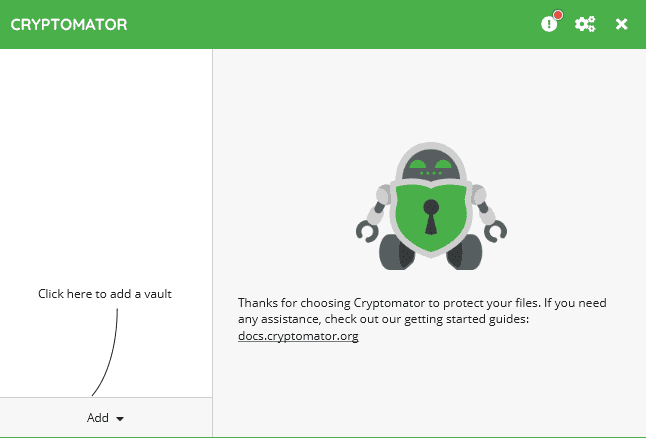
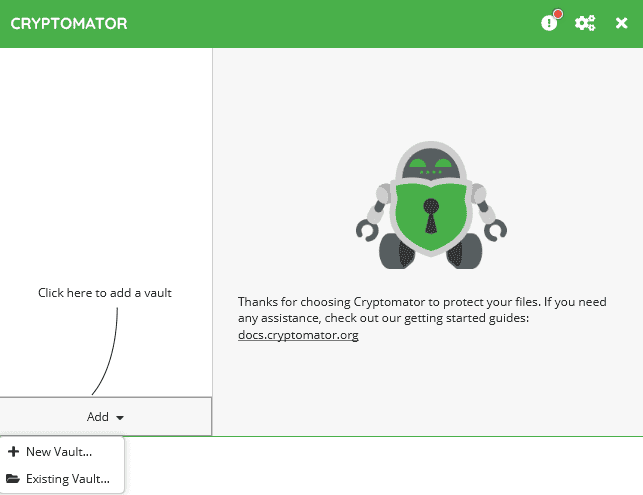
- Add a Vault
You can choose to add a new vault or work with an existing one. For the purposes of this guide, select “new vault.”
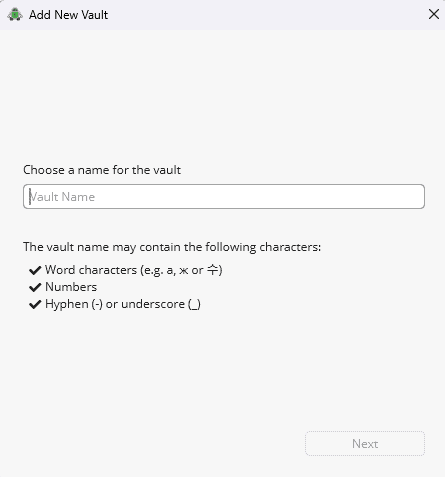
- Name the Vault
The next step is to name your new vault. When ready, select “next.”
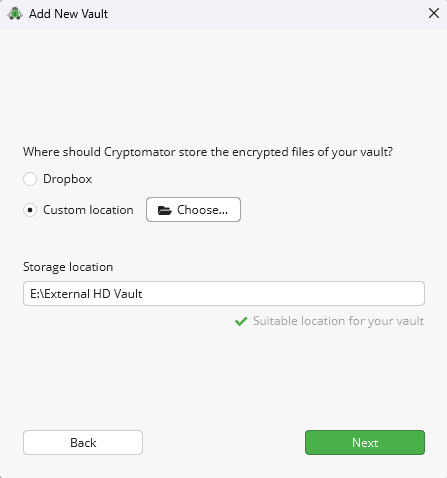
- Choose the Location
You can choose where the new vault will be located. Select “custom location” to find and choose the external drive.
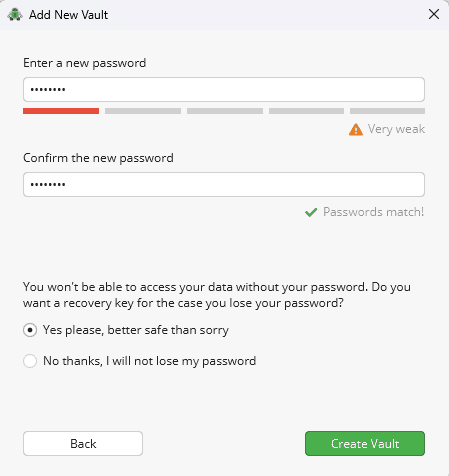
- Choose a Password
Enter a strong password that you won’t forget. To adhere to best practice, enable a recovery key.
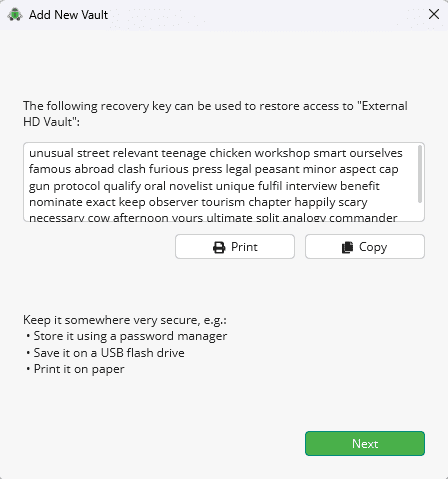
- Recovery Key
If you enable a recovery key, you will see a screen displaying it. Print or copy it.
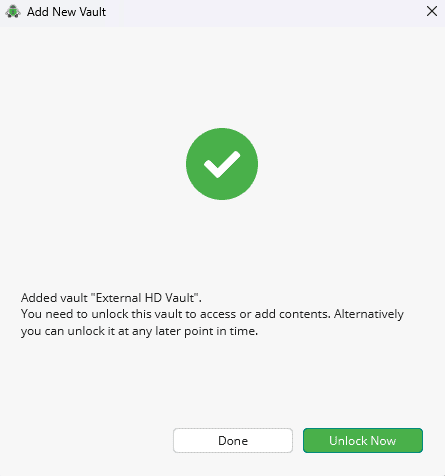
- Create
Clicking “next” on the previous screen creates the new vault. You will see a “success” screen when the process is done. Click “done” to close the window or “unlock now” to access the vault on your external hard drive.
The Best Hard Drive Encryption Software: Cryptomator
Cryptomator is a free, open-source encryption app that works with Mac and Windows computers. It’s effortless to use, with clear instructions while using the app and a fully supported document library if you need help. Above all, it has excellent security, as you’d expect from an encryption software product.
Cryptomator has few features, with the main interface for creating and managing existing vaults providing the bulk of the experience. Cryptomator doesn’t limit the number of devices or file size, making it a flexible option to encrypt multiple items. It has zero-knowledge encryption, and only the provided recovery key will help if you lose your password. Find out more in our Cryptomator review.
Besides Cryptomator, another popular open-source encryption tool is VeraCrypt (the successor to TrueCrypt), which offers strong encryption for both entire drives and individual volumes.
For enhanced security, consider investing in external drives with built-in hardware encryption. These specialized drives include a dedicated encryption processor that handles all cryptographic operations independently from your computer, offering better performance and protection against certain attack vectors that might compromise software-based encryption
How Do I Encrypt a USB Drive? (All Operating Systems)
You can encrypt a USB flash drive following the same steps as above, depending on what you use to encrypt it. You can use Disk Utility on Mac, BitLocker on Windows or a third-party encryption software like VeraCrypt. The process of encrypting a USB is identical to that of an external drive.
Encryption is especially important for removable devices like USB drives since they’re more likely to be lost or stolen due to their portable nature.
How Do I Create an Encrypted Cloud Backup?
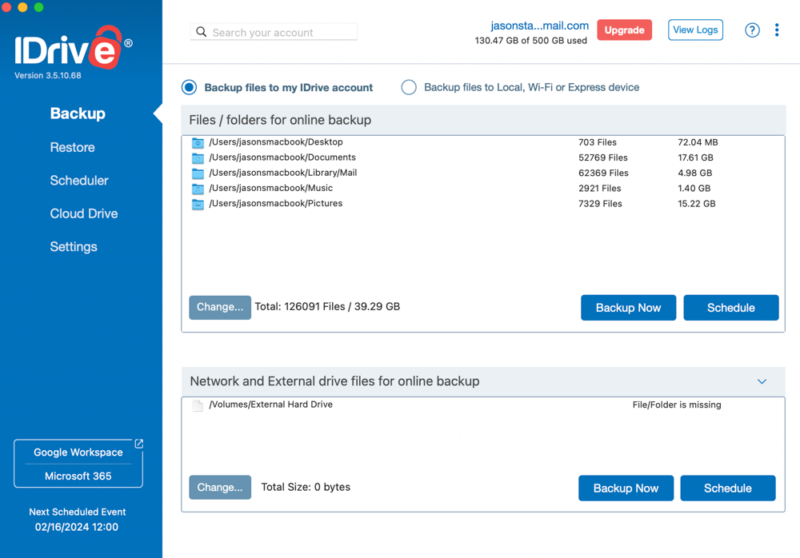
Another option with some providers is to use a cloud backup to encrypt your external drive. IDrive is a cloud backup service that can accomplish this task. When connected to your computer, IDrive will recognize the external drive and allow you to select it for backup.
By default, IDrive does not have private encryption. However, when you first create an account, you have the option to enable private encryption. Doing so ensures the highest level of privacy for your data. Anything you back up to your private encryption-enabled IDrive account will have the same level of protection.
If you don’t have a zero-knowledge IDrive account, you can still encrypt your external hard drive using the previous processes and use IDrive to back up its contents. The following steps assume you have an IDrive account. If not, you can sign up for free and download the desktop app for your operating system.
- Open IDrive
Open the IDrive app for Windows or Mac. Connect your external drive to your computer. You will see it available for backup in the IDrive app.
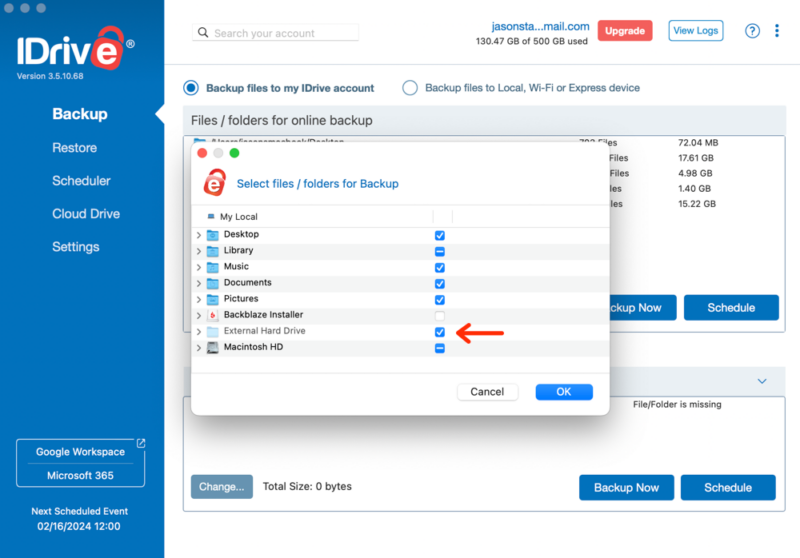
- Backup the External Hard Drive
If you haven’t already, select the external hard drive and choose “backup now” to back up all the data on the external drive.
The Best Cloud Backup for External Hard Drives: IDrive
IDrive is our pick for the best online backup service. It has many features to manage your backups, including cloud storage functionality like file sharing. An IDrive account has separate storage space for your backups and your cloud storage drive folder. Additionally, you can back up multiple devices to one account.
IDrive has an excellent desktop app for Mac and Windows, with several tabs to manage your account. One tab includes robust scheduling tools, while another lets you restore data from a previous backup. The mobile app for iOS and Android devices contains tools to upload your images automatically. We have more details in our IDrive review.
Final Thoughts
Encrypting your external drive is the best way to protect your data. Depending on your operating system, you can use built-in encryption software like Disk Utility on Mac or BitLocker on Windows. You can also use third-party disk encryption software such as Cryptomator.
An alternative method is to invest in self-encrypting drives (SEDs) that come with hardware-based encryption built in, offering better performance than software encryption while maintaining the same level of security.
Air-gapping your computer is another way to secure your data, but remember that no matter which method you choose, you can rest easy knowing your data is safe. For more related guides, check out our articles on how to backup iPhone to an external hard drive and cloud storage vs external hard drive.
When creating passwords for your encrypted drives, use complex passphrases that combine uppercase and lowercase letters, numbers and special characters, with a minimum length of 12 characters. Avoid using personal information or common phrases, and consider using a password manager to generate and store these strong passwords securely.
Do you encrypt your external drive? Have you used any of these methods to encrypt an external hard drive? Are there other ways to encrypt an external hard drive that we missed? Let us know in the comments section below. Thanks for reading our article.
FAQ: Encrypt External Hard Drive
Yes, it is recommended that you encrypt external hard drives. They may not be connected to the internet, but that doesn’t mean your data isn’t vulnerable if left unencrypted.
You should encrypt all the files on an external hard drive. However, if you have to choose, encrypting the ones that contain personal, confidential or sensitive data is essential.
Encryption software that comes with an operating system, such as BitLocker on Windows or Disk Utility on Mac, are excellent tools for creating an encrypted volume. Third-party encryption software such as Cryptomator is also a great option.
Using Disk Utility on a Mac doesn’t involve any additional fees. BitLocker requires a Windows Pro account. Third-party encryption software like Cryptomator or VeraCrypt is free.


