PPTP vs OpenVPN: Differences, Advantages & Disadvantages in 2026
OpenVPN is the top dog of secure VPN protocols, while PPTP is a protocol that has security vulnerabilities. Read on as we compare PPTP vs OpenVPN to find out whether it’s worth using PPTP in today's internet age.
A VPN’s main job is to set up an encrypted tunnel for your internet connection and anonymize your online activity. It does this using what’s known as a VPN protocol, which wraps your traffic in encryption protocols to hide it from interlopers. OpenVPN and PPTP are two such protocols. In this article, we’ll pit PPTP vs OpenVPN to see which one is better to use with your VPN application.
We’ll delve into their features and differences, and in the end, we’ll make a recommendation. Alternatively, if you’re interested in an in-depth look at other protocols, you can read our VPN protocol guide.
-
04/04/2024 Facts checked
We rewrote the article with a new structure, adding more practical information on the VPN protocols and more comparisons to other protocols.
-
06/21/2024
Added custom graphics.
PPTP vs OpenVPN Comparison: At a Glance
One of the few advantages PPTP has over OpenVPN is its fast speed. Unfortunately, OpenVPN is better than PPTP in most other regards, including having better security, better reliability and more customization options.
If you’re still curious, we’ll go in depth on why PPTP is so bad for online security and why OpenVPN has been the darling of the VPN world for more than two decades. You can also read our VPN statistics article for more background on PPTP’s history.
Protect Your Privacy. Get Our Free VPN Guide Now!
- Comprehend the essential role a VPN plays in safeguarding your digital life
- Gain a deep understanding of how VPNs function under the hood
- Develop the ability to distinguish fact from fiction in VPN promotions
At a Glance: Differences Between OpenVPN and PPTP
| PPTP | OpenVPN |
|---|---|
| Not secure | Very secure |
| Some of the fastest speeds | Good speeds |
| Built into most major OSes | Requires OpenVPN client or VPN app to run |
| Encryption up to only 128 bits | Encryption up to 256 bits |
| Can be unstable | Very stable |
Security
OpenVPN is much more secure than PPTP because it uses practically uncrackable AES-256 encryption and solid open-source code. On the other hand, PPTP has been cracked since the ’90s, and you can even find tools online that can decrypt its encryption.
Performance and Speed
PPTP may be the faster protocol, but OpenVPN has the advantage of being more reliable. Not only is it generally more secure, but OpenVPN over TCP also has guaranteed packet delivery, ensuring no data is lost in communication. This can be crucial for applications such as online gaming, where a rock-steady VPN connection can make all the difference.
What Is PPTP?

PPTP stands for “point-to-point tunneling protocol.” A Microsoft-led group developed and released it with Microsoft Windows 95. It operates over TCP port 1723 and uses the GRE protocol to encapsulate data packets. PPTP was once ubiquitous, coming preinstalled on many operating systems, including Windows, macOS, Linux, iOS and Android.
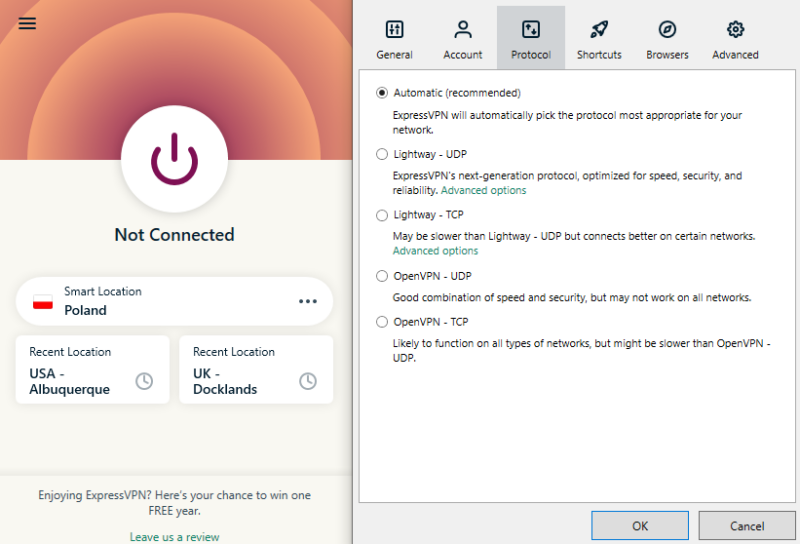
However, PPTP has been replaced by more modern and secure protocols like WireGuard and IKEv2. In fact, almost none of the VPN providers on our best VPN list support PPTP anymore, with the top provider offering a slim selection between OpenVPN and WireGuard or a custom protocol.
PPTP Advantages
These are the advantages of the PPTP protocol:
PPTP Disadvantages
These are the disadvantages of using PPTP:
What Is OpenVPN?

OpenVPN is a robust, highly configurable and secure open-source VPN protocol. It can run over the very secure TCP port 443 or UDP ports like 1194 for faster speeds. Today, it’s considered the gold standard for VPN protocols, and any VPN worth its salt supports it.
OpenVPN Advantages
These are the advantages of using the OpenVPN protocol:
OpenVPN Disadvantages
OpenVPN is great, but not perfect. Here are some of its flaws:
PPTP & OpenVPN vs Other VPN Protocols
Using PPTP can pose a security risk and potentially expose your sensitive data. Here are how some alternative protocols compare to PPTP and OpenVPN, and if there are other secure VPN protocols you should use.
What’s Better for Gaming: PPTP or OpenVPN?
Though PPTP is the faster protocol, we can’t in good conscience recommend using it in any application when there is a more secure option available. So, even though PPTP is technically faster for gaming, OpenVPN is still the superior gaming protocol thanks to its security.
Final Thoughts
Though PPTP was once a popular VPN protocol, more modern and secure options have eclipsed it, like OpenVPN, IKEv2 and WireGuard. When choosing a VPN service, be sure to choose one that offers these modern protocols, and stay away from PPTP if possible.
Have you had any experiences with PPTP? Were you aware of its security flaws? What are your thoughts on OpenVPN? Please let us know in the comments below, and as always, thank you for reading.
FAQ: OpenVPN vs PPTP
Though easy to use, PPTP’s aging encryption standards mean you should avoid it whenever a newer and more secure protocol is available.
PPTP is one of the fastest protocols, though the newer WireGuard can compete with it in speed while also providing much stronger security.
OpenVPN is better than PPTP in almost every aspect, with the exception of speed. In fact, OpenVPN is broadly considered to be the best VPN protocol, with WireGuard as its only serious challenger.
L2TP/IPsec is the more secure option of the two, which makes it better by default; PPTP’s security flaws make it too much of a liability to online privacy.


