How to Set Up a Personal Cloud Server in 2026
A personal cloud server gives you the same functionality as a service like Dropbox, except you retain full control of your data. It does require some setup and technical know-how, though, unless you use built-in tools like Synology Drive Client.
Anyone who has spent time on the internet and has a collection of personal data probably uses some form of cloud storage. You may even use one of the providers we’ve identified as the best cloud storage available. However, average users may not be as familiar with using a personal cloud server.
A personal cloud server is like having Dropbox at home, but without paying a subscription fee. If that sounds appealing, you may be wondering why more people don’t set up their own cloud server. Read on to learn more, including the benefits and drawbacks, as well as an easy way to set one up for yourself using a Synology NAS device.
-
02/20/2025 Facts checked
We rewrote this article to show you the pros and cons of personal cloud storage and ways to implement it.
What Is a Personal Cloud Server?
A personal cloud server lets you store and access data in the cloud, just like you would using a cloud storage provider like Google Drive or pCloud. You can upload and download files using an internet connection outside of your home network. Additionally, you can share data with others, just like you can with a third-party provider.
Using a personal cloud server requires more than just signing up for a service and downloading an accompanying app. You’ll need hardware, and there is some setup involved. Before deciding, check out the following benefits and potential downsides to setting up a personal cloud server.
10,000+ Trust Our Free Cloud Storage Tips. Join Today!

- Demystify cloud storage terminology and key concepts in plain language
- Discover easy-to-implement techniques to securely backup and sync your data across devices
- Learn money-saving strategies to optimize your cloud storage costs and usage
How Do I Set Up My Own Personal Cloud Storage Server at Home With a Synology NAS?
Using a Synology NAS device, you can quickly download the drive client to create a personal cloud server. Better still, the app is included with your account. Follow these steps to access the data on your Synology NAS from your devices even when you are not on your home network.
- Set Up Your Synology NAS
Set up your Synology NAS by logging in to your device and modifying your account. This step includes creating an account with Synology so you can access and connect to the apps. Note: you will need a login and password for your account and device.
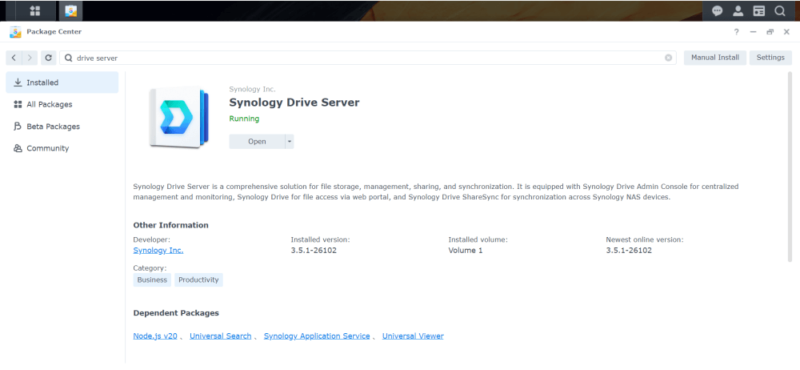
- Install Synology Drive Server
Once you can access the home screen of your Synology NAS, open the package center. You will see several packages pre-installed. Search for “Synology Drive Server.” Once you find it, install it on your device.
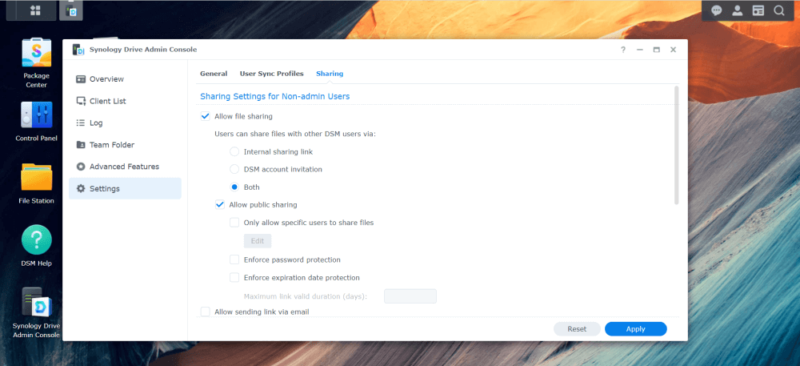
- Open the Admin Console
The drive server has a dedicated admin console that lets you see the devices using the service and other items, such as the space available on your NAS device. If you wish to enable file sharing, navigate to the settings tab and tick the appropriate box.
- Download Apps
You can download the drive client on multiple devices (iOS and Android), as well as the desktop app for Windows, Mac and Ubuntu (Linux), directly from Synology.com. Synology also has an APK available for download.

What Are the Best Third-Party Personal Cloud Storage Server Applications?
You have some options when setting up your personal cloud storage server. For starters, you’ll need to use third-party cloud software. Nextcloud is a great option, especially for businesses. Personal users can check out ownCloud, which is easier to use. If you’re curious about these services and how to set one up, check out our article on the best home cloud storage.
Which Personal Cloud Storage Devices Do We Recommend?
If you’ve made it this far, it should be clear that we are partial to Synology. It tops our list of the best personal cloud storage devices for home media. It has a lot of features that people look for in a NAS device, including affordability and ease of use. Western Digital is another great option, offering excellent affordability.
Synology DiskStation DS223j
Synology DiskStation is a popular NAS option for several reasons. We like it because you can get it up and running in no time, as you can read in our Synology DS223j review. The software and interface are easy to use and navigate. In addition, you can scale Synology DiskStation as your storage needs grow. All NAS solutions have an upfront cost, but DiskStation is affordable for most.
makes it easy with its DiskStation line of NAS devices.
WD My Cloud Home
Western Digital’s My Cloud NAS is an excellent option for anyone looking to get personal cloud storage without breaking the bank. It is one of the most affordable options available. However, there are some drawbacks. It is not as feature-rich as other options, and it cannot scale past the initial storage capacity.
Final Thoughts
Going through the process of setting up a personal cloud server is certainly worth the effort if you want to retain complete control over your data, as you don’t have to worry about a third party accessing it. This solution is not for everyone, though — it requires some technical setup, and you are responsible for keeping it up and running.
Have you set up personal cloud storage in your home? If not, would you consider doing so? If you use personal cloud storage, how is it working for you? Let us know in the comments section below. Thanks for reading our article.
FAQ: How to Make a Server at Home
A personal cloud server functions just like a cloud storage service such as Dropbox or Google Drive. You can access the data on your NAS even when you are away from your home network.
Yes, you can have your own cloud server. You can use a dedicated service like NextCloud or ownCloud. Synology has a service called Drive Client, which turns your NAS device into a cloud server.
You can create a private cloud server by turning your NAS device into a server. Doing so means only you and those whom you allow access can use your cloud server. Don’t confuse this with free cloud storage, though, as there is an upfront cost involved.
You’ll typically pay between $50 to $100 per year for 1TB of cloud storage with most providers. However, the more common plan size is 2TB per year.





